Rapid7’s Managed Detection and Response (MDR) team continuously monitors our customers’ environments, identifying emerging threats and developing new detections.
Rapid7 的托管检测和响应 (MDR) 团队持续监控客户的环境,识别新出现的威胁并开发新的检测方法。
In August 2023, Rapid7 identified a new malware loader named the IDAT Loader. Malware loaders are a type of malicious software designed to deliver and execute additional malware onto a victim’s system. What made the IDAT Loader unique was the way in which it retrieved data from PNG files, searching for offsets beginning with 49 44 41 54 (IDAT).
2023 年 8 月,Rapid7 发现了一个名为 IDAT Loader 的新恶意软件加载程序。恶意软件加载程序是一种恶意软件,旨在将其他恶意软件传递和执行到受害者的系统上。IDAT 加载程序的独特之处在于它从 PNG 文件中检索数据的方式,搜索以 49 44 41 54 (IDAT) 开头的偏移量。
At the time, the loader was seen being distributed via a FakeUpdates campaign. In two recent investigations, Rapid7’s Managed Detection & Response (MDR) observed the loader being used again. Based on the recent tactics, techniques and procedures observed (TTPs), we believe the activity is associated with financially motivated threat groups.
当时,人们看到加载器是通过 FakeUpdates 活动分发的。在最近的两项调查中,Rapid7 的托管检测和响应 (MDR) 观察到装载机再次被使用。根据最近观察到的策略、技术和程序 (TTP),我们认为该活动与出于经济动机的威胁组织有关。
In this two-part blog series, we will examine the attack chain observed in two separate incidents, offering in-depth analysis of the malicious behavior detected. The incidents discussed in the series stem from opportunistic infections, wherein threat groups utilize malvertising and drive-by downloads in order to have their initial malicious payloads executed by users.
在这个由两部分组成的博客系列中,我们将研究在两个独立事件中观察到的攻击链,并对检测到的恶意行为进行深入分析。该系列中讨论的事件源于机会主义感染,其中威胁组织利用恶意广告和偷渡式下载,以便用户执行其初始恶意负载。
This first installment focuses on an incident triggered by a user downloading an application, which subsequently triggered the execution of the IDAT Loader and the BruteRatel C4 (BRC4) framework following initial access to a compromised asset.
第一部分重点介绍用户下载应用程序触发的事件,该事件随后在初始访问受损资产后触发了 IDAT Loader 和 BruteRatel C4 (BRC4) 框架的执行。
Technical Analysis 技术分析
Stage 1: The drive by
第 1 阶段:开车经过
In a recent incident, we observed a user navigate to a website that hosted popular Korean shows. Upon attempting to watch the video, the website redirected the user’s browser through multiple websites, eventually leading to the download of an application named AppFile_v1.1.exe. Threat actors utilize website redirection in order to make it difficult for network technologies to scan links for malicious content.
在最近的一次事件中,我们观察到一个用户导航到一个托管热门韩国节目的网站。在尝试观看视频时,该网站通过多个网站重定向了用户的浏览器,最终导致下载了一个名为 AppFile_v1.1.exe 的应用程序。威胁行为者利用网站重定向,使网络技术难以扫描链接中的恶意内容。
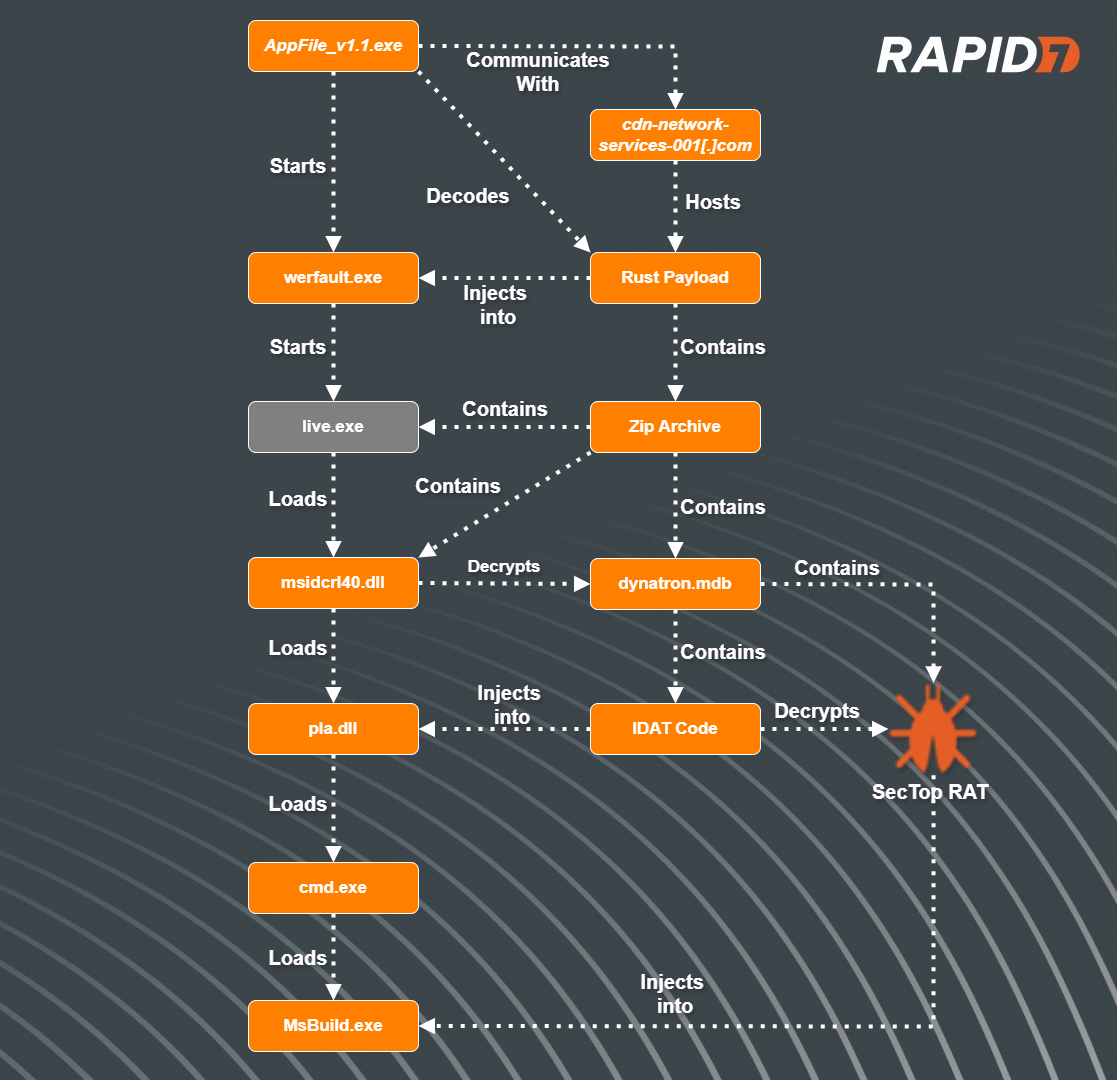
图1 – 攻击流
Binary Analysis: Shaking off the Rust
二元分析:甩掉锈迹
After initial analysis of the binary AppFile_v1.1.exe, we determined the program was written in Rust.
在对二进制AppFile_v1.1.exe进行初步分析后,我们确定该程序是用 Rust 编写的。
During execution, the program will query the name of the executable. If the executable’s name matches AppFile_v1.1.exe, the program will continue. Most sandboxes will rename the files (sometimes based on the hash) of submitted programs. This technique helps to evade sandboxes, ensuring the malicious functions are not run. If the program name does not match its original intended name, the program will quit and display an error message, showing an image that a web page could not be loaded.
在执行过程中,程序将查询可执行文件的名称。如果可执行文件的名称AppFile_v1.1.exe匹配,则程序将继续。大多数沙盒会重命名已提交程序的文件(有时基于哈希值)。此技术有助于规避沙箱,确保恶意功能不运行。如果程序名称与其原始预期名称不匹配,程序将退出并显示错误消息,显示无法加载网页的图像。
图2 — 检查失败时AppFile_v1.1.exe显示的错误消息
Next, the program will check to see if it resides within a debugger by querying the function IsDebuggerPresent. If the check passes, it will decrypt a hard-coded string that resolves to “Normal”. If not, the program will decrypt another hard-coded string that resolves to “Debugger” and then exit.
接下来,程序将通过查询函数 IsDebuggerPresent 来检查它是否驻留在调试器中。如果检查通过,它将解密解密解析为“正常”的硬编码字符串。如果没有,程序将解密另一个解析为“调试器”的硬编码字符串,然后退出。
Once the anti-debug check passes, the program retrieves an encrypted string and XOR decrypts it, revealing the URL hxxps://cdn-network-services-001[.]com/update/minor/1/release.json.
一旦反调试检查通过,程序就会检索一个加密的字符串,然后 XOR 对其进行解密,从而显示 URL hxxps://cdn-network-services-001[.]com/update/minor/1/release.json。
The program will then perform anti-analysis techniques, specifically querying for the username and open process and comparing them to a list of known sandbox usernames and tools. The list of usernames and processes are also XOR-encrypted and are decrypted at runtime. Based on Open Source Intelligence, we determined that another malware known as Serpent Stealer contained a similar table of user names. See Appendix A below for the complete list.
然后,该程序将执行反分析技术,特别是查询用户名和打开的进程,并将它们与已知的沙盒用户名和工具列表进行比较。用户名和进程列表也经过异或加密,并在运行时解密。根据开源情报,我们确定另一种名为 Serpent Stealer 的恶意软件包含类似的用户名表。有关完整列表,请参阅下面的附录 A。
| Usernames | Known Sandbox ToolsProcesses |
|---|---|
| hbyldjtckyn1 | httpdebuggerui.exe |
| lubi53an14cu | immunitydebugger.exe |
| rgzcbuyrznreg | ksdumperclient.exe |
| 8lnfaai9qdjr | httpanalyzerstdv7.exe |
| j6sha37ka J6SHA37Ka型 | ida64.exe |
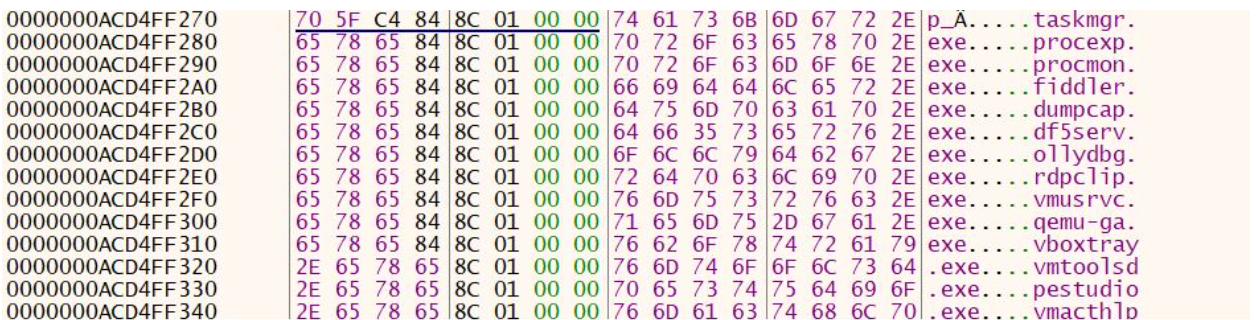
图3 — x64Debugger的示例输出显示要检查的进程列表
If any of the checks fail, the program will exit and display the message box. If the checks pass, the program will then utilize Rust library tokio-1.32.0/src/net/tcp/stream.rs in order to read in data from the decrypted URL and store the contents in memory.
如果任何检查失败,程序将退出并显示消息框。如果检查通过,程序将利用 Rust 库 tokio-1.32.0/src/net/tcp/stream.rs 从解密的 URL 中读取数据并将内容存储在内存中。
Upon initial analysis, the downloaded data appeared to be encoded. Subsequently, the data is passed into a function tasked with decoding it. The decoding process involves reading each byte and subtracting the hexadecimal value 32.
经过初步分析,下载的数据似乎是编码的。随后,数据被传递到负责解码的函数中。解码过程包括读取每个字节并减去十六进制值 32。
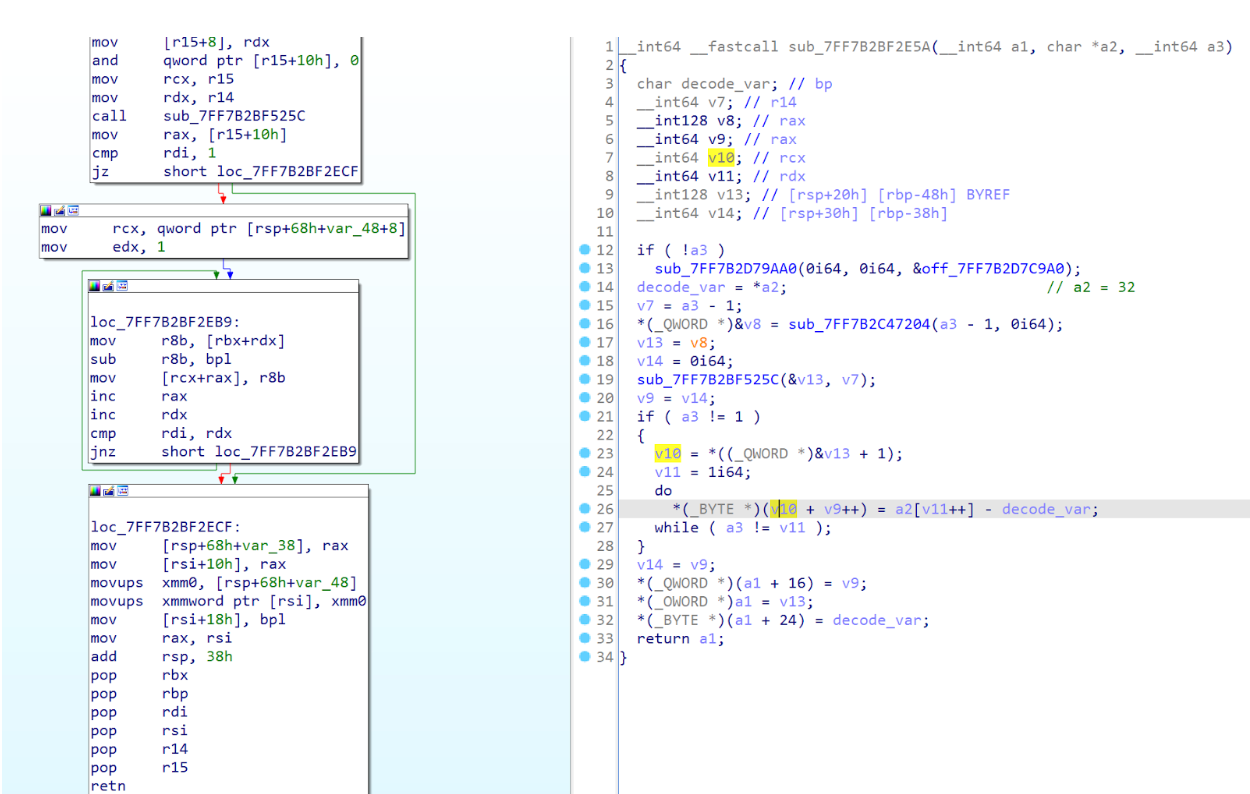
图4 – 数据解码例程
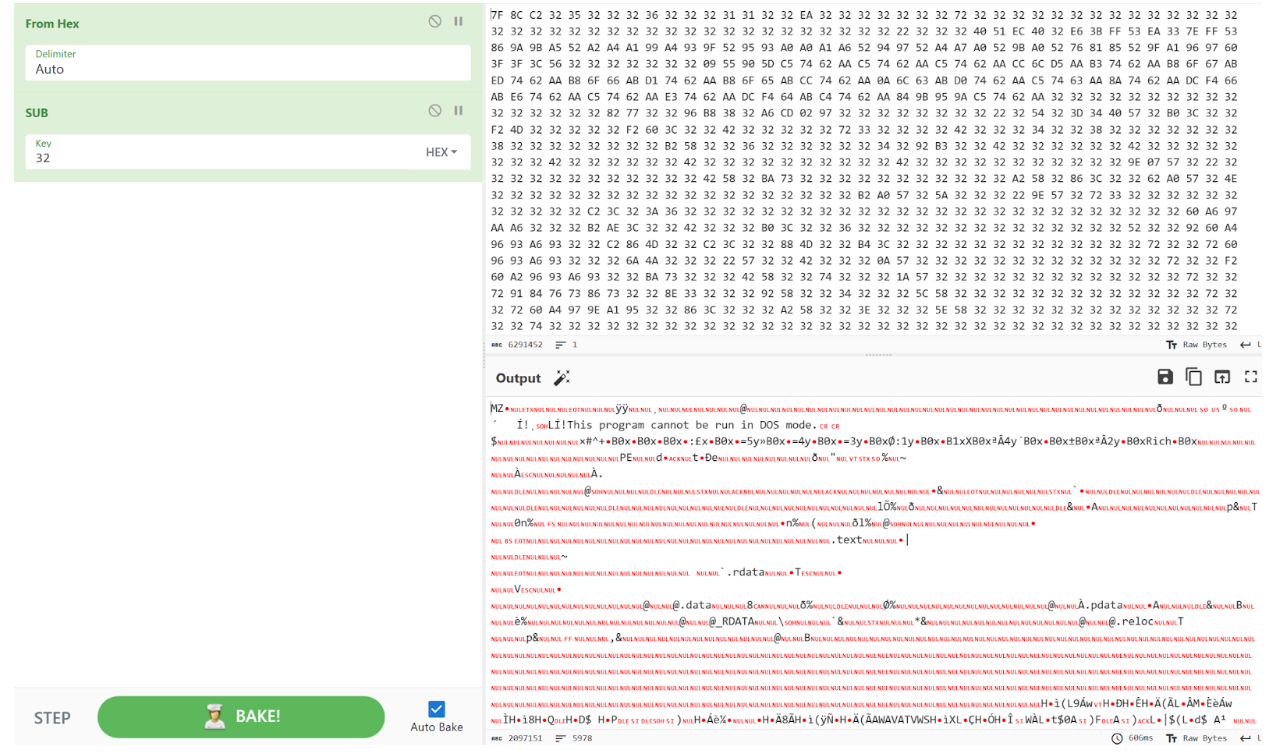
图 5 – 使用 CyberChef 解码下载的字节
After the downloaded data is decoded, the program XOR decrypts another string, revealing a path to the executable C:\Windows\system32\werfault.exe. Using syscalls, the program then does the following:
对下载的数据进行解码后,程序 XOR 会解密另一个字符串,从而显示可执行文件 C:\Windows\system32\werfault.exe 的路径。然后,使用系统调用,程序执行以下操作:
| Windows API Function | Syscall ID | Description |
|---|---|---|
| NtOpenProcess NtOpen进程 | 0x0026 | Used to start the process werfault.exe 用于启动进程werfault.exe |
| NtCreateUserProcess | 0x00c8 | Used for spoofing Parent Process ID (PPID) 用于欺骗父进程 ID (PPID) |
| NtAllocateVirtualMemory | 0x0018 | Allocate new space within memory, storing the new executable 在内存中分配新空间,存储新的可执行文件 |
| NtGetContextThread | 0x00F2 | Used to retrieve the context of a thread within the target process (werfault.exe). 用于检索目标进程 (werfault.exe) 中线程的上下文。 |
| The thread in this case is a pointer to the entry point of the new executable 在本例中,线程是指向新可执行文件入口点的指针 |
||
| NtSetContextThread NtSetContext线程 | 0x0018B | Used to point to the thread from NtGetContextThread 用于指向 NtGetContextThread 中的线程 |
| NtResumeThread NtResume线程 | 0x0052 | Starts the thread set by NtSetContextThread 启动 NtSetContextThread 设置的线程 |
After analysis of the decoded binary, we determined that it was another executable written in Rust. The program’s executable contains a zip archive within the .rdata section. During execution, the program generates a folder with a randomly generated name in the %TEMP% directory and extracts the contents of the archive into this newly created folder.
在分析了解码的二进制文件后,我们确定它是另一个用 Rust 编写的可执行文件。该程序的可执行文件在 .rdata 部分包含一个 zip 存档。在执行过程中,程序会在 %TEMP% 目录中生成一个具有随机生成名称的文件夹,并将存档的内容提取到这个新创建的文件夹中。
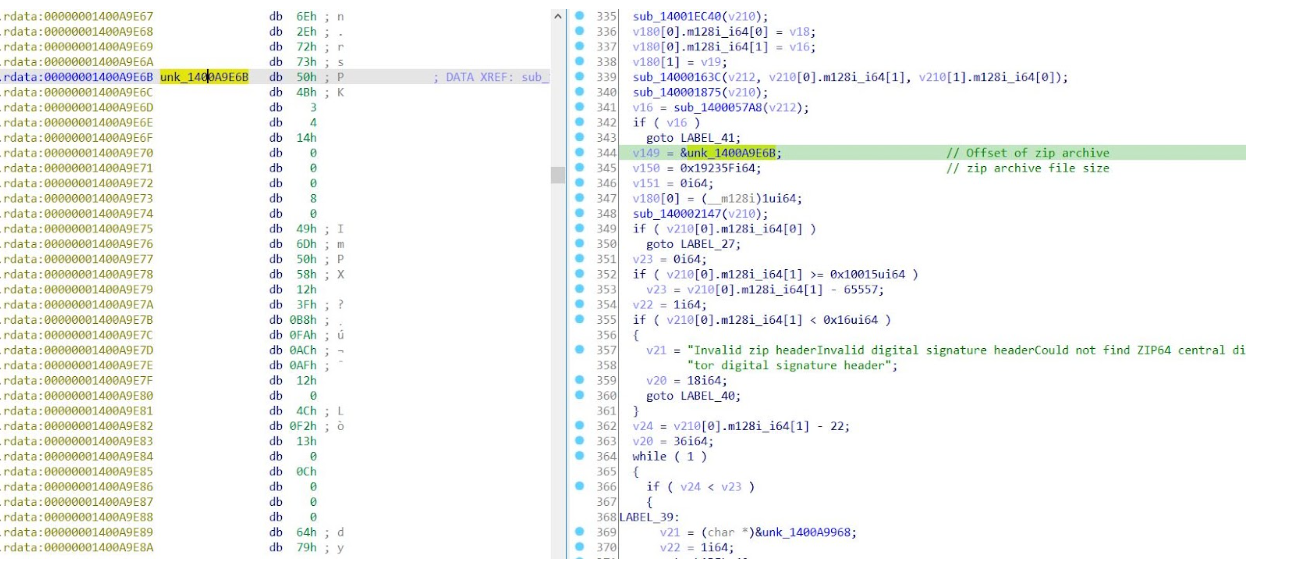
图6 – 新 Rust 可执行文件中包含的 ZIP 存档
The archive contained a DLL, msidcrl40.dll, an executable named live.exe and an encrypted file, dynatron.mdb. Initial analysis of the DLL msidcrl40.dll showed that the DLL’s signature was corrupted, indicating the DLL was tampered with. Further analysis showed that the DLL contained code related to the IDAT Loader.
存档包含一个 DLL、msidcrl40.dll、一个可执行namedlive.exe和一个加密文件 dynatron.mdb。对 DLL msidcrl40.dll的初步分析表明 DLL 的签名已损坏,表明 DLL 已被篡改。进一步的分析表明,DLL 包含与 IDAT 加载程序相关的代码。
IDAT Loader IDAT装载机
After the rust program drops the contents of the zip archive, it then proceeds to execute the binary live.exe, which sideloads the DLL, msidcrl40.dll, containing the IDAT Loader code.
在 rust 程序删除 zip 存档的内容后,它继续执行二进制live.exe,该二进制旁加载包含 IDAT 加载程序代码的 DLL msidcrl40.dll。
After the binary live.exe loads the DLL msidcrl40.dll, the DLL executes the function containing the IDAT Loader. The loader then reads in encrypted contents contained within the file dynatron.mdb, searching for the offset 49 44 41 54 (IDAT) followed by C6 A5 79 EA. After decrypting the contents, the loader will then decompress the contents using RtlDecompressBuffer and execute additional code into a newly created process, cmd.exe.
binarylive.exe加载 DLL msidcrl40.dll后,DLL 将执行包含 IDAT 加载程序的函数。然后,加载程序读取文件dynatron.mdb中包含的加密内容,搜索偏移量 49 44 41 54 (IDAT),后跟 C6 A5 79 EA。解密内容后,加载程序将使用 RtlDecompressBuffer 解压缩内容,并在新创建的进程 cmd.exe 中执行其他代码。
The IDAT loader employs advanced techniques such as Process Doppelgänging and the Heaven’s Gate technique in order to initiate new processes and inject additional code.
IDAT加载器采用先进的技术,如进程分身和天堂之门技术,以启动新进程并注入其他代码。
The code contained within cmd.exe is responsible for decrypting the final payload and injecting it into a newly created process, msbuild.exe.
msbuild.exe,包含withincmd.exe的代码负责解密最终有效负载并将其注入到新创建的进程中。
Using our IDAT Loader config extractor, we were able to extract the final payload and determined that it was SecTop RAT. During execution of the SecTop RAT, we observed that it communicated with the IP address 152.89.217[.]215.
使用我们的 IDAT Loader 配置提取器,我们能够提取最终有效载荷并确定它是 SecTop RAT。在执行 SecTop RAT 期间,我们观察到它与 IP 地址 152.89.217[.]215.
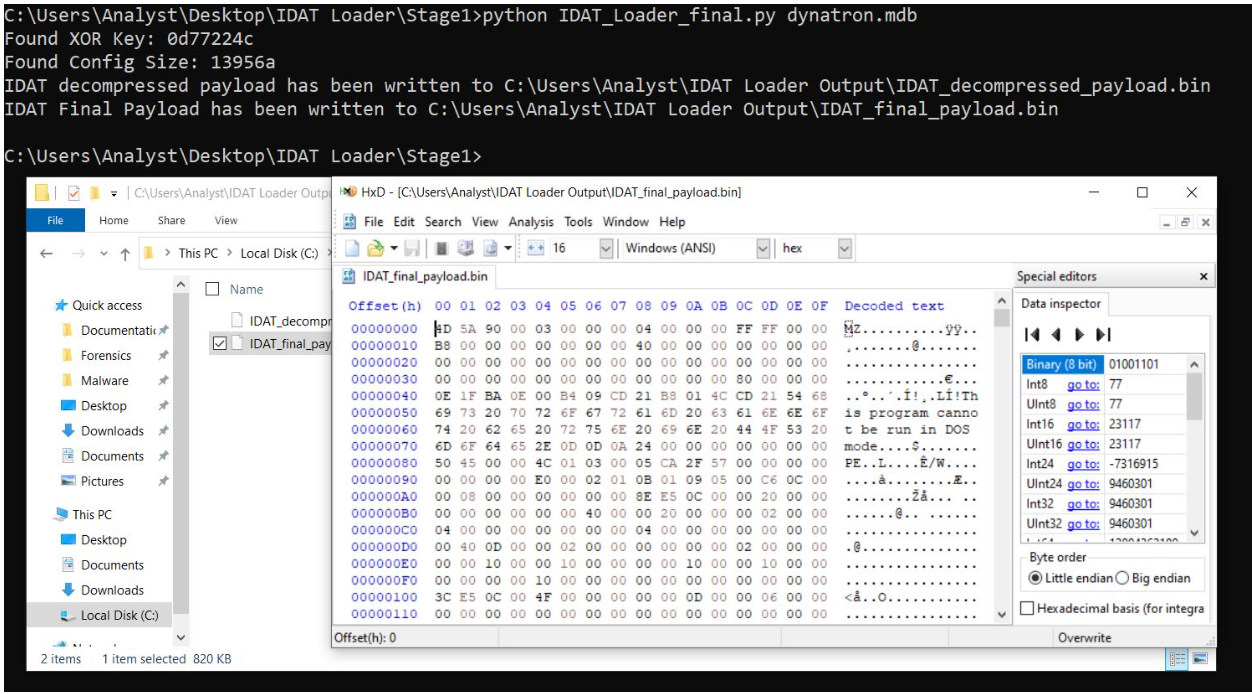
图 7 – IDAT Loader Python 脚本提取的 SecTop RAT 有效负载Figure 7 – SecTop RAT payload extracted by our IDAT Loader Python Script
Post-Exploitation: BRC4 Deployment
开发后:BRC4 部署
After the SecTop RAT was executed successfully, Rapid7 observed follow-on activity in which the threat actor executed another version of the IDAT loader from within the folder path C:\ProgramData\. We observed the following related files were dropped by the threat actor into C:\ProgramData:
成功执行 SecTop RAT 后,Rapid7 观察到后续活动,其中威胁参与者从文件夹路径 C:\ProgramData\ 中执行了另一个版本的 IDAT 加载程序。我们观察到威胁参与者将以下相关文件拖放到 C:\ProgramData 中:
| Files | Description |
|---|---|
| glib-2.0.dll | Benign executable loaded by rvm.exe 由 rvm.exe 加载的良性可执行文件 |
| iconv.dll | Benign executable loaded by rvm.exe 由 rvm.exe 加载的良性可执行文件 |
| intl.dll | Benign executable loaded by rvm.exe 由 rvm.exe 加载的良性可执行文件 |
| rvm.exe | Legitimate executable that loads vmtools.dll during execution 在执行过程中加载vmtools.dll的合法可执行文件 |
| spank.mpg | Encrypted file containing IDAT sections, read in by vmtools.dll 包含IDAT部分的加密文件,由vmtools.dll读入 |
| vmtools.dll | Tampered DLL containing IDAT Loader, loaded by rvm.exe 被篡改的 DLL 包含 IDAT Loader,由 rvm.exe 加载 |
After analysis of the files, we determined that rvm.exe was a renamed executable rvmsetup.exe, a legitimate tool that is a part of the VMWare Tools toolset. The binary is used to join a VMWare source virtual machine to an active directory domain. We also observed that the binary vmtools.dll had a corrupted signature, indicating the binary’s code was tampered with. We observed that the DLL vmtools.dll contained code related to the IDAT Loader.
在分析文件后,我们确定rvm.exe是一个重命名的可执行rvmsetup.exe,这是一个合法工具,是 VMWare 工具集的一部分。二进制文件用于将 VMWare 源虚拟机加入 Active Directory 域。我们还观察到binaryvmtools.dll的签名已损坏,表明二进制文件的代码被篡改。我们观察到 DLL vmtools.dll包含与 IDAT 加载程序相关的代码。
During execution of the executable, rvm.exe, the program loads vmtools.dll. After vmtools.dll is loaded, the DLL is directed to execute a function that contains the IDAT Loader. The IDAT Loader proceeds to read in contents from within spank.mpg, searching for the same offset, 49 44 41 54 (IDAT) followed by C6 A5 79 EA. After decrypting the contents within spank.mpg, the IDAT Loader spawns a new process, cmd.exe, injecting additional code that is responsible for decrypting the final payload and injecting it into a newly created process, explorer.exe.
在执行可执行文件 rvm.exe 期间,程序会加载vmtools.dll。加载vmtools.dll后,DLL 被定向执行包含 IDAT 加载程序的函数。IDAT 加载程序继续从 spank.mpg 中读取内容,搜索相同的偏移量 49 44 41 54 (IDAT),后跟 C6 A5 79 EA。解密spank.mpg中的内容后,IDAT 加载程序会生成一个新进程 cmd.exe,注入负责解密最终有效负载并将其注入新创建的进程 explorer.exe。
Using our static config extractor, we extracted the final payload, a 64-bit executable. During initial analysis of the final payload, we observed that the program utilized the API functions VirtualAlloc and VirtualProtect. During execution of the program, it utilized VirtualAlloc to read in and store additional code, including encrypted data, into a new region of memory. The program then called upon the function VirtualProtect, changing the newly allocated region of memory (containing the new code) to be executable. We also observed the 64 bit executable (obtained from the IDAT Loader python script) had the capability to perform process hollowing by starting a new process, notepad.exe, and injecting the code into the newly created process.
使用我们的静态配置提取器,我们提取了最终的有效负载,一个 64 位可执行文件。在对最终有效载荷的初步分析中,我们观察到该程序利用了 API 函数 VirtualAlloc 和 VirtualProtect。在程序执行期间,它利用 VirtualAlloc 将其他代码(包括加密数据)读入并存储到新的内存区域中。然后,程序调用函数 VirtualProtect,将新分配的内存区域(包含新代码)更改为可执行的。我们还观察到 64 位可执行文件(从 IDAT Loader python 脚本获取)能够通过启动新进程、notepad.exe并将代码注入新创建的进程来执行进程空心化。
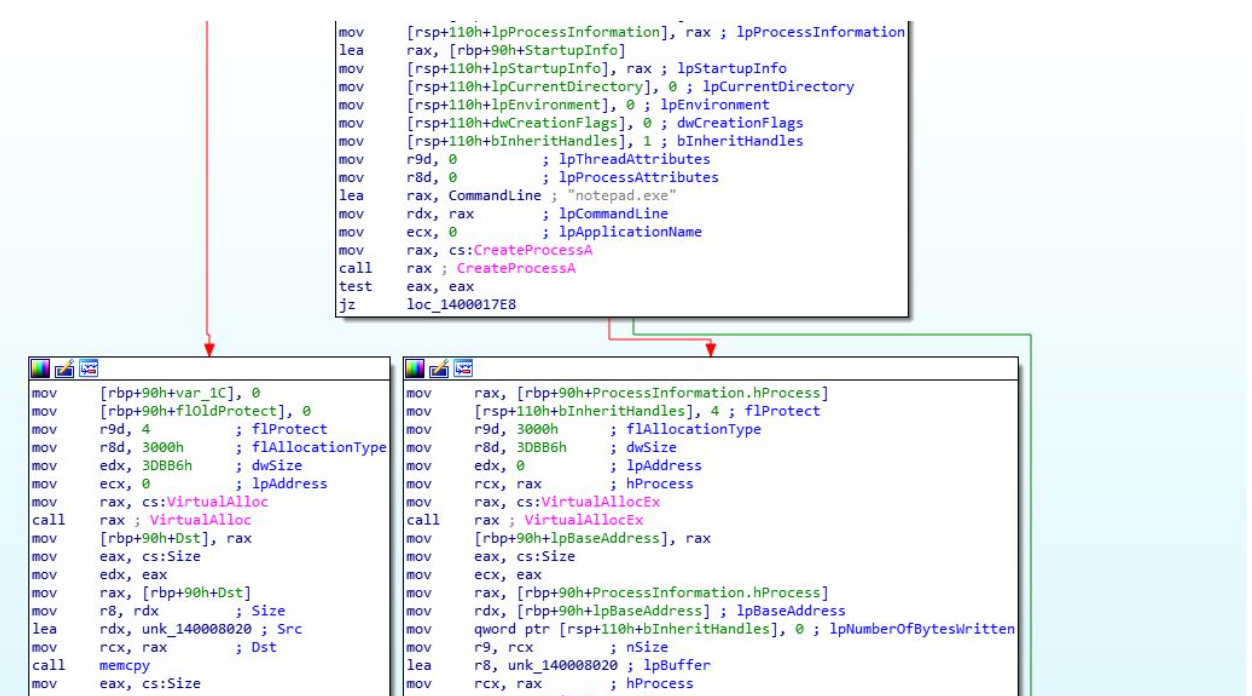
图8 – 显示注入notepad.exe的最终有效载荷
The newly allocated code was responsible for decrypting the encrypted data using RC4, copying the decrypted code into an allocated memory buffer via VirtualAlloc, and setting the memory buffer to have executable permission using VirtualProtect. Rapid7 determined the decrypted code was a Brute Ratel C4 (BRC4) “badger”.
新分配的代码负责使用 RC4 解密加密数据,通过 VirtualAlloc 将解密的代码复制到分配的内存缓冲区中,并使用 VirtualProtect 将内存缓冲区设置为具有可执行权限。Rapid7 确定解密的代码是 Brute Ratel C4 (BRC4) “badger”。
Brute Ratel originated as a post-exploitation tool intended for penetration testers, designed to mimic adversary tactics as of December 2020. Its development aimed to replicate the functionality of established Command and Control (C2) software like Cobalt Strike, Mythic and Sliver. Following a successful compromise of a target, the attacker deploys the Brute Ratel “badger,” tasked with establishing communication with the attacker’s Command and Control domain.
Brute Ratel 起源于一种用于渗透测试人员的开发后工具,旨在模仿截至 2020 年 12 月的对手战术。它的开发旨在复制已建立的命令和控制(C2)软件的功能,如Cobalt Strike,Mythic和Sliver。在成功入侵目标后,攻击者会部署 Brute Ratel“獾”,其任务是与攻击者的命令和控制域建立通信。
During execution of the BRC4 program, we observed that it reached out to the domain updatenazure[.]com.
在执行 BRC4 程序期间,我们观察到它到达了域 updatenazure[.]com。
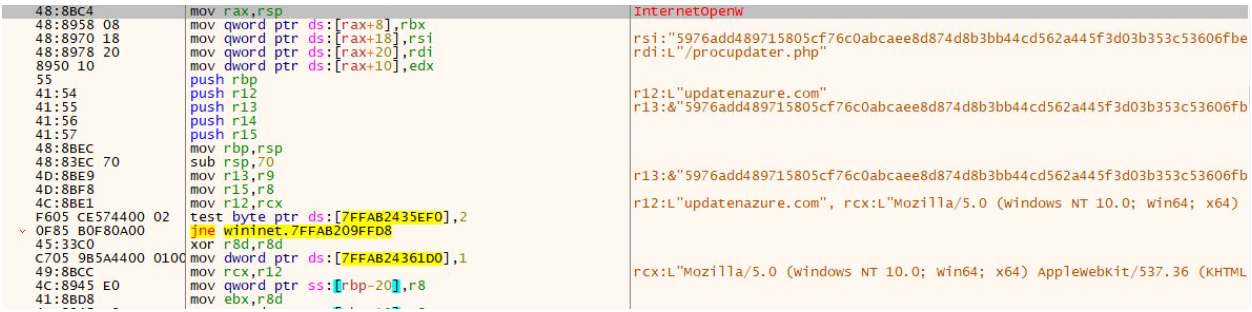
图9 – 调试BRC4 C2通信
After the BRC4 program was executed, we observed the threat actor attempting to enumerate the domain controller by using the command nltest /dclist.
执行 BRC4 程序后,我们观察到威胁参与者尝试使用命令 nltest /dclist 枚举域控制器。
Rapid7 Customers Rapid7 客户
InsightIDR and Managed Detection and Response customers have existing detection coverage through Rapid7’s expansive library of detection rules. Rapid7 recommends installing the Insight Agent on all applicable hosts to ensure visibility into suspicious processes and proper detection coverage. Below is a non-exhaustive list of detections deployed and alerting on activity described:
InsightIDR 和 Managed Detection and Response 客户通过 Rapid7 广泛的检测规则库拥有现有的检测覆盖范围。Rapid7 建议在所有适用的主机上安装 Insight Agent,以确保对可疑进程的可见性和适当的检测范围。下面是已部署的检测和所述活动警报的非详尽列表:
- Network Discovery – Nltest Enumerate Domain Controllers
网络发现 – Nltest 枚举域控制器 - Suspicious Process – Execution From Root of ProgramData
可疑进程 – 从程序数据根目录执行 - Suspicious Process – PowerShell Uncommon Upper And Lower Case Combinations
可疑进程 – PowerShell 不常见的大写和小写组合 - Suspicious Process – explorer.exe in Non-Standard Location
可疑进程 – explorer.exe在非标准位置
Appendix A: Known Sandbox Usernames and Analysis Tools
附录 A:已知沙盒用户名和分析工具
| Usernames | Processes |
|---|---|
| hbyldjtckyn1 | httpdebuggerui.exe |
| lubi53an14cu | immunitydebugger.exe |
| rgzcbuyrznreg | ksdumperclient.exe |
| 8lnfaai9qdjr | httpanalyzerstdv7.exe |
| j6sha37ka J6SHA37Ka型 | ida64.exe |
| keecfmwgj | 32dbg.exe |
| pwouqdtdq | 64dbg.exe |
| qmis5df7u | protection_id.exe |
| txwas1m2t | vmsrvc.exe |
| uox1tzamo | x32dbg.exe |
| rb5bnfur2 | x64dbg.exe |
| cm0uegn4do | x96dbg.exe |
| douyo8rv71 斗友8RV71 | prl_cc.exe |
| paul jones 保罗·琼斯 | windbg.exe |
| pxmduopvyx | scylla.exe |
| fnbdsldtxy | idau64.exe |
| gexwjqdjxg | idaq64.exe |
| gjam1nxxvm | idag64.exe |
| jcotj17dzx JCOTJ17DZX系列 | taskmgr.exe |
| 05kvauqkpqk5 | procexp.exe |
| 64f2tkiqo5k5h | procmon.exe |
| of20xqh4vl | fiddler.exe |
| harry johnson 哈里·约翰逊 | dumpcap.exe |
| 4tgiizslims | df5serv.exe |
| bvjchrpnsxn | ollydbg.exe |
| kfu0lqwgx5p | rdpclip.exe |
| nok4zg7zhof NOK4ZG7ZHof(诺克4ZG7ZHOF酒店) | vmusrvc.exe |
| ogjb6gqgk0o5 | qemu-ga.exe |
| xplyvzr8sgc | vboxtray.exe |
| ykj0egq7fze | vmtoolsd.exe |
| ryjijkiroms | pestudio.exe |
| nzap7ubvas1 | vmacthlp.exe |
| 9yjcpseyimh | procexp64.exe |
| uhuqiuwoefu 呜 | wireshark.exe |
| 6o4kyhhjxbir | prl_tools.exe |
| 7wjlgx7pjlw4 | importrec.exe |
| 8nl0colnq5bq | vmwaretray.exe |
| g2dbyldgzz8yo | vmwareuser.exe |
| pqonjhvwexsst | xenservice.exe |
| rdhj0cnfevzxf | scylla_x86.exe |
| xmimmckziitdl | scylla_x64.exe |
| l3cnbb8ar5b8 | vboxservice.exe |
| vzy4jmh0jw02 | |
| 21zlucunfi85 | |
| sal.rosenburg 萨尔·罗森堡 | |
| defaultaccount 默认帐户 | |
| wdagutilityaccount wdagutility帐户 |
MITRE ATT&CK Techniques MITRE ATT&CK 技术
| Tactics | Techniques | Details |
|---|---|---|
| Initial Access 初始访问 | Drive-by Compromise (T1189) 偷渡式妥协 (T1189) |
Threat Actors utilize drive-by downloads in order to direct browsers to download their initial payloads without users consent 威胁参与者利用偷渡式下载来指导浏览器在未经用户同意的情况下下载其初始有效负载 |
| Execution 执行 | User Execution: Malicious File (T1204.002) 用户执行:恶意文件 (T1204.002) |
Users execute the binary AppFile_v1.1.exe 用户执行二进制AppFile_v1.1.exe |
| Execution 执行 | Native API (T1106) 本机 API (T1106) | The IDAT injector and IDAT loader are using Heaven’s Gate technique to evade detection IDAT喷油器和IDAT加载器正在使用天堂之门技术来逃避检测 |
| Defense Evasion 防御规避 | Hijack Execution Flow: DLL Search Order Hijacking (T1574.001) 劫持执行流:DLL 搜索顺序劫持 (T1574.001) |
run.exe loads a malicious wbxtrace.dll run.exe加载恶意wbxtrace.dll |
| Defense Evasion 防御规避 | Process Injection (T1055) 工艺注入 (T1055) |
IDAT injector implements NtCreateSection + NtMapViewOfSection Code Injection technique to inject into cmd.exe process IDAT 注入器实现 NtCreateSection + NtMapViewOfSection 代码注入技术以注入到cmd.exe进程中 |
| Defense Evasion 防御规避 | Deobfuscate/Decode Files or Information (T1140) 对文件或信息进行反混淆/解码 (T1140) |
msidcrl40.dll decrypts dynatron.mdb msidcrl40.dll解密dynatron.mdb |
| Defense Evasion 防御规避 | Process Injection: Process Doppelgänging (T1055.013) 工艺注入:工艺分身 (T1055.013) |
IDAT loader implements Process Doppelgänging technique to load the SecTop RAT IDAT 加载器实现进程分身技术来加载 SecTop RAT |
| Defense Evasion 防御规避 | Masquerading (T1036) 伪装 (T1036) | dynatron.mdb file masqueraded to a .png file 伪装成.png文件的dynatron.mdb文件 |
| Defense Evasion 防御规避 | Virtualization/Sandbox Evasion: Time Based Evasion (T1497.003) 虚拟化/沙盒规避:基于时间的规避 (T1497.003) |
Execution delays are performed by several stages throughout the attack flow 在整个攻击流程中,执行延迟由多个阶段执行 |
IOCs 国际奥委会
| IOC | Sha256 | Notes |
|---|---|---|
| AppFile_v1.1.exe | A3A5E7011335A2284E2D4F73FD464FF129F0C9276878A054C1932BC50608584B | Rust Loader responsible for downloading IDAT Loader Rust Loader 负责下载 IDAT Loader |
| msidcrl40.dll | 02D5E281689EC2D4AB8AC19C93321A09113E5D8FA39380A7021580EA1887B7A5 | Malicious DLL executed by live.exe live.exe执行的恶意DLL |
| dynatron.mdb | C5C52331B208CAD19DC710786E26AC55090FFCA937410D76C53569D731F0BB92 | Encrypted payload decrypted by msidcrl40.dll 由 msidcrl40.dll 解密的加密有效负载 |
| vmtools.dll | BEFE0DF365F0E2DC05225470E45FDF03609F098A526D617C478B81AC6BB9147F | Malicious DLL executed by rvm.exe rvm.exe执行的恶意DLL |
| spank.mpg | E05E561C5118EFDBCA113CA231C527B62E59A4BFFAE3BD374F7B4FCDD10E7D90 | Encrypted payload decrypted by vmtools.dll 由 vmtools.dll 解密的加密有效负载 |
| hxxps://cdn-network-services-001[.]com/update/minor/1/release.json | Downloads additional Rust binary containing IDAT Loader 下载包含 IDAT Loader 的其他 Rust 二进制文件 |
|
| 152.89.217[.]215 | SecTop RAT domain SecTop RAT 域名 | |
| updatenazure[.]com | BRC4 Domain BRC4 域名 |
References 引用
| Article | URL |
|---|---|
| Uncovering the “Serpent” 揭开“蛇” |
https://malware.news/t/uncovering-the-serpent/76253 |
| Process Doppelgänging 工艺分身 | https://malware.news/t/uncovering-the-serpent/76253 |
| Analysis of “Heaven’s Gate” part 1 《天堂之门》第一部分分析 |
https://sachiel-archangel.medium.com/analysis-of-heavens-gate-part-1-62cca0ace6f0 |
| A Deep Dive Into Malicious Direct Syscall Detection 深入了解恶意直接系统调用检测 |
https://www.paloaltonetworks.com/blog/security-operations/a-deep-dive-into-malicious-direct-syscall-detection/ |
| Fake Update Utilizes New IDAT Loader To Execute StealC and Lumma Infostealers 虚假更新利用新的 IDAT 加载程序执行 StealC 和 Lumma 信息窃取程序 |
https://www.rapid7.com/blog/post/2023/08/31/fake-update-utilizes-new-idat-loader-to-execute-stealc-and-lumma-infostealers/ |
Rapid7 Labs GitHub
原文始发于Tom Elkins:Stories from the SOC Part 1: IDAT Loader to BruteRatel
转载请注明:Stories from the SOC Part 1: IDAT Loader to BruteRatel | CTF导航