In the high-stakes realm of cybersecurity, the role of a penetration tester stands out as both highly coveted and fiercely competitive. Navigating an interview for such a position comes with its own set of challenges.
在高风险的网络安全领域,渗透测试人员的角色既令人垂涎又竞争激烈。驾驭这样一个职位的面试有其自身的一系列挑战。
But fear not. Whether you’re a hopeful candidate or a recruiter searching for top-tier talent, we’ve got you covered.
但不要害怕。无论您是充满希望的候选人,还是寻找顶级人才的招聘人员,我们都能满足您的需求。
Our guide to 15 carefully curated penetration testing interview questions, answered by seasoned infosec professionals, is here to help!
我们的 15 个精心策划的渗透测试面试问题指南,由经验丰富的信息安全专业人士回答,随时为您提供帮助!
1. What is penetration testing, and can you explain the difference between vulnerability scanning and pentesting?
1. 什么是渗透测试,您能解释一下漏洞扫描和渗透测试之间的区别吗?
💡Interviewers ask this question to see if the candidate understands what a pentester does and can see the bigger picture of why organizations undergo a pentest.
💡面试官问这个问题是为了看看候选人是否理解渗透测试者的工作,并能看到组织为什么要进行渗透测试的更大图景。
Answer: 答:
“A penetration test is an organized, targeted, and authorized attack that tests the security posture and defensive capabilities of IT infrastructure.
“渗透测试是一种有组织的、有针对性的、授权的攻击,用于测试IT基础设施的安全态势和防御能力。
Normally, there’s a specific agreed-upon time frame that a penetration test will span, rules of engagement, and a clearly defined scope.
通常,渗透测试将跨越一个特定的商定时间框架、交战规则和明确定义的范围。
In the end, the expected deliverable is a detailed penetration test report that security teams can use to mitigate any vulnerabilities that were discovered.
最后,预期的可交付成果是一份详细的渗透测试报告,安全团队可以使用该报告来缓解发现的任何漏洞。
Sample penetration testing report template 👇
渗透测试报告模板👇样本
A real-world example of a penetration testing report created by the HTB Academy team. Use it as a template for your next report!
HTB Academy 团队创建的渗透测试报告的真实示例。将其用作下一份报告的模板!
Penetration tests are important because they are a great way to check if your security controls and processes are actually working. Without conducting penetration tests, I believe organizations can have a false sense of security.
渗透测试很重要,因为它们是检查安全控制和流程是否实际工作的好方法。如果不进行渗透测试,我相信组织可能会有一种虚假的安全感。
A simple comparison I keep in mind is that pentesting is like checking if the door to your home is actually locked and the alarm is armed.
我记住的一个简单比较是,渗透测试就像检查你家的门是否真的锁上了,警报器是否被武装起来。
I may think “Did I actually lock my door and arm the alarm?” I can turn around and check by trying to open the door.
我可能会想,“我真的锁上了门并打开了警报器吗?我可以转过身来,试着打开门检查。
A penetration test takes this a step further and emulates a malicious attacker without all the destructive elements.
渗透测试更进一步,在没有所有破坏性元素的情况下模拟恶意攻击者。
It makes sure the security controls are doing what they are expected to do. Or even identifies the need for security controls where there are none.
它确保安全控制正在执行预期操作。甚至在没有安全控制的地方确定对安全控制的需求。
The main focus of a vulnerability assessment is to identify and categorize risk associated with vulnerabilities discovered in IT assets. Typically they are conducted using automated scanning tools like Nessus or OpenVAS.
漏洞评估的主要重点是识别和分类与 IT 资产中发现的漏洞相关的风险。通常,它们使用 Nessus 或 OpenVAS 等自动扫描工具进行。
They are commonly conducted as completely different assessments than penetration tests and do not focus on penetrating further into the network environment through the active use of exploits and attack chaining.
它们通常作为与渗透测试完全不同的评估进行,并且不侧重于通过积极使用漏洞利用和攻击链进一步渗透到网络环境中。
Organizations often have a vulnerability assessment done because they are required to for compliance reasons.
组织通常会进行漏洞评估,因为出于合规性原因,他们需要这样做。
PCI-DSS (Payment Card Industry Data Security Standard) is one example, they require an internal and external vulnerability scan quarterly as outlined on page 23 of the PCI DSS v3.2.1 Quick Reference Guide.
PCI-DSS(支付卡行业数据安全标准)就是一个例子,它们需要每季度进行一次内部和外部漏洞扫描,如 PCI DSS v3.2.1 快速参考指南第 23 页所述。
That said, a vulnerability assessment is not as comprehensive as a penetration test.”
也就是说,漏洞评估不如渗透测试全面。
Hack The Box content to help you answer this question in an interview:
Hack The Box 内容可帮助您在采访中回答这个问题:
Related read: Interested in landing a job as a SOC analyst? Brush up on these SOC analyst interview questions!
相关阅读: 有兴趣找到一份 SOC 分析师的工作吗?复习这些 SOC 分析师面试问题!
2. Can you describe the differences between risk analysis and penetration testing?
2. 您能描述一下风险分析和渗透测试之间的区别吗?
💡Interviewers may ask this question to uncover any risk analysis experience you have and ensure that you understand the differences between the two.
💡面试官可能会问这个问题,以发现您拥有的任何风险分析经验,并确保您了解两者之间的区别。
Answer: 答:
“Both risk analysis and penetration testing are important aspects of cybersecurity and can complement each other well.
“风险分析和渗透测试都是网络安全的重要方面,可以很好地相辅相成。
A risk analysis is the process of studying all potential threats and faults that could lead to vulnerabilities in software.
风险分析是研究可能导致软件漏洞的所有潜在威胁和故障的过程。
It doesn’t require any scanning tools or applications, instead, a risk analysis aims to identify assets, vulnerabilities, threats, and the overall impact on the company if the vulnerability were exploited.
它不需要任何扫描工具或应用程序,相反,风险分析旨在识别资产、漏洞、威胁以及漏洞被利用时对公司的整体影响。
On the other hand, a penetration test is the act of lawfully attacking a system to identify any vulnerabilities. This tests whether existing systems and processes are actually working.
另一方面,渗透测试是合法攻击系统以识别任何漏洞的行为。这测试了现有系统和流程是否真正起作用。
Overall, a risk analysis is more practical, identifying potential risks and impacts. Whereas, a penetration test is more technical, going beneath the surface to uncover vulnerabilities.”
总体而言,风险分析更实用,可以识别潜在的风险和影响。然而,渗透测试更具技术性,深入表面之下以发现漏洞。
3. Can you describe the different phases of a typical penetration testing engagement?
3. 您能描述一下典型渗透测试的不同阶段吗?
💡Interviewers typically ask this interview question to see if the candidate understands how a penetration tester typically approaches an engagement.
💡面试官通常会问这个面试问题,看看候选人是否了解渗透测试人员通常如何处理参与。
Answer: 答:
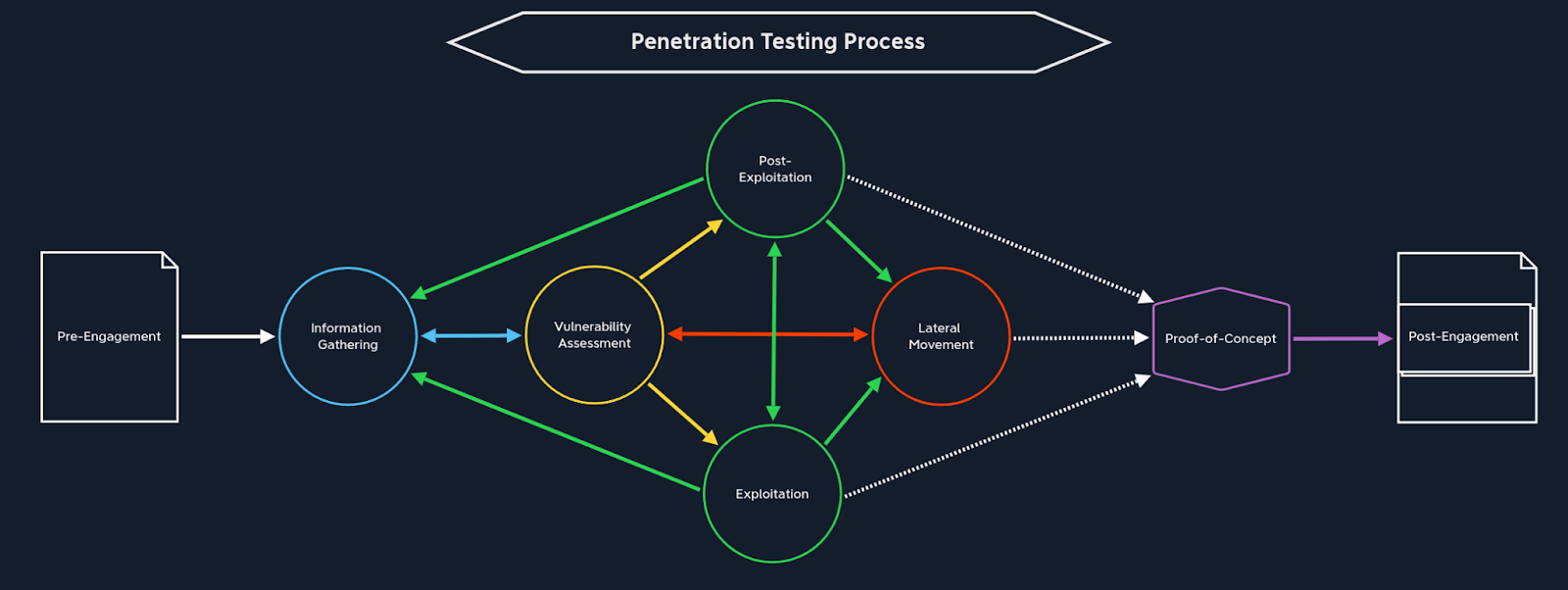
“The phases and the order in which they are done can differ depending on who you talk to. In general, these are the phases of a penetration test, many of which will be repeated as the test progresses:
“阶段和完成的顺序可能会有所不同,具体取决于您与谁交谈。一般来说,这些是渗透测试的阶段,其中许多阶段将随着测试的进行而重复:
-
Pre-engagement 订婚前
-
Information gathering 信息收集
-
Vulnerability assessment (as a phase built-in to the pentest)
-
Exploitation
-
Post-exploitation
-
Lateral movement
-
Post-engagement
During the pre-engagement phase, all of the important work (not as exciting) is done to ensure all relevant parties understand and document the details and expectations of the test.
At the information-gathering phase, the test and fun begins. This is where I start doing open source intelligence (OSINT) and enumerating hosts, the network, and any reachable services.
I will be documenting any promising findings that the client should know about, like:
-
Unexpected services and IP subnets that are reachable.
-
Secrets found in public-facing GitHub repos, AWS S3 buckets, and other cloud storage technologies.
-
Social media activity from employees that may reveal what technologies are used at the company (commonly found on job descriptions).
-
A visual network diagram to assist me in enumeration and discovery throughout the engagement.
At the vulnerability assessment stage, I start using the information we gathered to determine if there are any vulnerabilities present that can be exploited.
I might start looking up known vulnerabilities based on service and software versions, noting any CVEs, finding proof of concept exploits (PoCs), and carefully planning the attack attempts.
At the exploitation phase, I’ll perform the attack and/or series of planned attacks to attempt to exploit any vulnerabilities.
If I have been brought on to test an environment externally and internally, I will be attempting to exploit a vulnerable public-facing system to see if the vulnerability will allow me to pivot from that external-facing system onto internal IT infrastructure.
There are some companies that still host their own websites on-prem in a DMZ, but it is more common for companies to use 3rd party website hosting services or cloud providers for website or web application hosting.
If the engagement calls for me to test from the internal perspective, my contact will provide me with remote access via virtual private network (VPN) or even use an attack VM that gets spun up somewhere on their internal network environment.
如果参与要求我从内部角度进行测试,我的联系人将通过虚拟专用网络 (VPN) 为我提供远程访问,甚至使用在其内部网络环境中某处启动的攻击 VM。
Regardless, I will document each attack I attempt (successful and unsuccessful), including the date and time for full transparency.
无论如何,我将记录我尝试的每次攻击(成功和失败),包括日期和时间,以实现完全透明。
In the post-exploitation phase, I will check to see what kind of privileges the account I landed on has. If it is a Windows system I’ll run a series of commands to live off the land, discover interesting files, and find potential pathways for privilege escalation, including but not limited to:
在开发后阶段,我将检查我登陆的帐户具有什么样的权限。如果是 Windows 系统,我将运行一系列命令来生存,发现有趣的文件,并找到权限提升的潜在途径,包括但不限于:
-
whoami /priv
-
ipconfig /all
-
netstat -antp
-
arp -a ARP -A(英语:ARP -A)
-
Systeminfo 系统信息
-
wmic qfe get Caption, Description, HotFixID, InstalledOn
wmic qfe get 标题、说明、 HotFixID、 InstalledOn
I’ll also look for any interesting files on the system using a series of search-centric commands and scripts (example: WinPEAS) that are configured to look in common directories using keywords that may find files containing sensitive information.
我还将使用一系列以搜索为中心的命令和脚本(例如:WinPEAS)在系统上查找任何有趣的文件,这些命令和脚本配置为使用关键字在公共目录中查找,这些关键字可能会找到包含敏感信息的文件。
Depending on how secure the environment is, I may choose not to run any type of pre-made scripts to attempt to avoid any potential detections. That said, I understand that it isn’t always bad to get detected as a tester.
It helps the organization see what they are doing right as well, I just wouldn’t want the engagement to end too soon 😊.
At the lateral movement phase, I will use information gathered from what I did in post-exploitation to determine if I can—and how I should—try to move laterally to another system on the network.
Lateral movement and post-exploitation are very closely related, as are all the phases. This may mean that I discover the Windows system I land on is part of a Windows domain, and I try to harvest domain user credentials that I could use to remotely access another system on the network through WinRM.
During the post-engagement phase, the report will be prepped to be delivered to the client. I would, of course, use whatever template our company uses to remain in line with our quality standards, operational practices, and style.
As a team, we may come together to discuss the scoring of each vulnerability to communicate impact and prioritize mitigation based on severity.
We would also work with the client to schedule a time when we can discuss our findings with all the relevant stakeholders.”
Hack The Box content to help you answer this question:
-
All Hack The Box Academy modules in the Penetration Tester Job Role Path
4. What makes a system vulnerable?
4. 是什么使系统容易受到攻击?
💡Assessing vulnerabilities is an important part of pentesting. So interviewers will want to understand your ability to exploit them.
💡评估漏洞是渗透测试的重要组成部分。因此,面试官会想了解你利用他们的能力。
Answer: 答:
“There are various ways a system can be vulnerable, generally falling into the categories of patch management, vulnerability management, and configuration management. Some common examples are as follows:
“系统有多种易受攻击的方式,通常分为补丁管理、漏洞管理和配置管理等类别。以下是一些常见的示例:
Running an out-of-date service or application with a known vulnerability that has a public exploit proof-of-concept available.
运行具有已知漏洞的过期服务或应用程序,该漏洞具有可用的公共漏洞利用概念验证。
A misconfigured service or application that can be leveraged to gain unauthorized access (i.e., weak or default credentials, lack permissions, no authentication required, etc.)
配置错误的服务或应用程序,可用于获取未经授权的访问(即弱凭据或默认凭据、缺少权限、无需身份验证等)
A web application that is vulnerable to web application vulnerabilities such as those covered under the OWASP Top 10.
A system that is part of an Active Directory environment that can be accessed via credential reuse or any other myriad of Active Directory attacks.
An end-of-life or unstable system that may be “fragile” and subject to a denial of service condition when stressed.”
Hack The Box can help you answer this question:
5. How would you handle sensitive data or information you come across during a penetration test?
💡Interviewers may ask this pentesting interview question to see if candidates understand the ethical implications and responsibilities that come with being a penetration tester.
Answer:
“Every vulnerability discovered on a client’s network can technically be considered sensitive data or information. Our job as a pentesting team is to help our clients improve security and teach them how they can do so.
As we document our findings, we must be careful and responsible with client data as we’re trusted to do right by them. Suppose we are doing a test for a healthcare provider. It is not my job as a tester to go poking around a database of protected health information (PHI) out of curiosity.
It is my job to discover the vulnerability in the system and understand the impact and potential risk it poses for the client.
Then, document this in a report and deliver it to the client. Some information will be redacted, but we, as a pentesting firm, will likely be keeping a copy of that report on our own company-owned systems.
(We will want to ensure reports are stored on encrypted drives and when moved around over the network, that protocols and message systems use the strongest encryption possible.)
It is also possible that a tester can come across certain information on a system that may be considered illegal content. If this happened to me I would immediately stop the test and consult with my supervisor.
We would likely then communicate the details of what was found and we may even consult with our own legal counsel on how and if we should proceed.”
然后,我们可能会传达所发现内容的细节,我们甚至可以咨询我们自己的法律顾问,讨论如何以及是否应该继续进行。
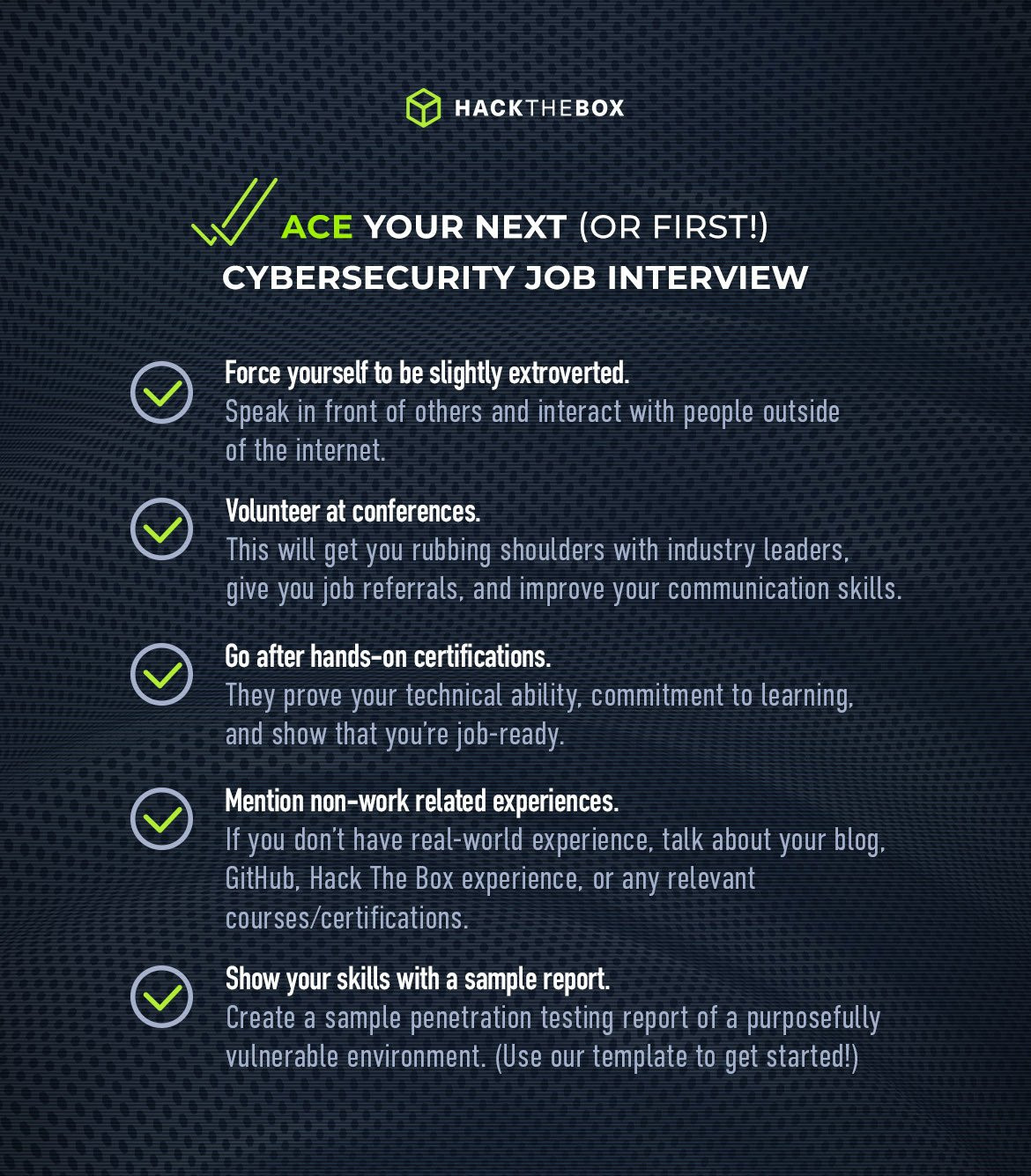
Need help preparing for interviews?
需要帮助准备面试吗?
-
Master complex concepts with free guided cybersecurity courses on the HTB Academy. (Student discounts are available.)
通过HTB学院的免费网络安全指导课程掌握复杂的概念。(提供学生折扣。 -
Prove that you have job-ready cybersecurity skills by taking the CPTS penetration testing certification (you’ll have example reports and pentests to share in interview assignments).
通过参加 CPTS 渗透测试认证来证明您具备为工作做好准备的网络安全技能(您将在面试作业中分享示例报告和渗透测试)。 -
Show your investment in your skills development and earn CPE credits by solving Machines, Challenges, Endgames, and real-world cybersecurity labs.
展示您对技能发展的投资,并通过解决机器、挑战、残局和现实世界的网络安全实验室来获得 CPE 学分。
6. Explain the difference between asymmetric encryption and symmetric encryption?
6. 解释一下非对称加密和对称加密的区别?
💡Organizations often use encryption to protect their data, so understanding the difference between the two main types is important.
💡组织经常使用加密来保护其数据,因此了解这两种主要类型之间的区别非常重要。
Answer: 答:
“Symmetric encryption uses a single shared key for both encryption and decryption and is generally faster, requiring less computing resources. It’s ideal for bulk data encryption where efficiency is a key consideration.
“对称加密使用单个共享密钥进行加密和解密,通常速度更快,需要更少的计算资源。它是批量数据加密的理想选择,其中效率是一个关键考虑因素。
Asymmetric encryption uses a public and private key pair. The public key is used for encrypting the data, while the private key is used to decrypt (or vice versa). This type of encryption is most commonly used for secure key exchange, digital signatures, and other forms of secure communication.
One practical scenario where both encryption types are in use is when using SSH (Secure Shell) to connect to a server. Asymmetric encryption is used for the initial connection in which a secure key exchange is performed. Symmetric encryption is used for data encryption during the session.
Another scenario is web browsing. Asymmetric encryption is used when first establishing a secure connection to a website via the web browser, while symmetric encryption is used to quickly and efficiently encrypt the data that is transmitted during the browsing session.”
7. How do you stay up-to-date with the latest security vulnerabilities and attack techniques?
💡Interviewers may ask candidates this question to see their continuous learning strategy.
Answer:
“I use a mixture of passive and active learning to stay updated. Of course, I’m on social media sites like LinkedIn, Twitter and YouTube. I’m intentional about following people who post IT and cybersecurity-focused content.
I also subscribe to newsletters like SANs NewsBites. I’ve found this method is faster than waiting on traditional news and media outlets. It is also fun as I may be sitting on the couch or relaxing while learning.
My favorite resources to follow are:
I also like active learning using sites like Hack The Box because this helps me realize the impact and reality of what is mentioned in the news.
The Academy modules and Boxes that get released are often inspired by recent vulnerabilities that have been discovered in the industry.
Exploit CVE-2023-4911 now
立即利用 CVE-2023-4911
-
- The TwoMillion machine is vulnerable to Looney Tunables, and is available to play on Hack The Box right now.
TwoMillion 机器容易受到 Looney Tunables 的攻击,现在可以在 Hack The Box 上玩。
Often I may come across a post on Twitter that links to a GitHub repo with a PoC exploit for a vulnerability found in Active Directory or something, and I’ll try that PoC in my own home lab. I did this with NoPac when it was first announced.
我经常会在 Twitter 上看到一篇帖子,该帖子链接到一个 GitHub 存储库,其中包含针对 Active Directory 或其他漏洞的 PoC 漏洞,我会在我自己的家庭实验室中尝试该 PoC。当 NoPac 首次发布时,我就用它做到了这一点。
As soon as I saw it work on my lab domain controller, I immediately started notifying my friends and contacts who lead security teams so they could mitigate.”
当我看到它在我的实验室域控制器上工作时,我立即开始通知领导安全团队的朋友和联系人,以便他们能够缓解。
8. What are the strengths and differences between Windows and Linux for web application testing?
8. Windows 和 Linux 在 Web 应用程序测试方面的优势和区别是什么?
💡Interviewers may ask candidates this question to determine their experience with both systems and their analytical skills.
💡面试官可能会问候选人这个问题,以确定他们在这两个系统中的经验和分析技能。
Answer:
“Windows and Linux both have strengths and weaknesses when it comes to web application testing. For beginners, Windows can be more user-friendly than Linux, which is more challenging to use.
However, Linux is much more reliable and secure in comparison to Windows. This is because inexperienced users often use Windows, making the OS more vulnerable to attackers.
In terms of usability for web application testing, Linux has a wider variety of native penetration testing tools, as well as a high degree of customization. The command-line interface in Linux is ideal for scripting and automation.
Having said this, Windows can be easier to navigate and offers many commercial tools. It’s also important to consider that many organizations use Windows, meaning that pentesting from a Windows machine will much better mimic those real-world scenarios.
I personally advocate for a hybrid approach, upskilling my web application testing using both machines, enabling me to benefit from both.”
HTB content that can help you answer this question:
9. What are your top 3 must-have tools for an AD-centric pentest and why?
💡Interviewers may ask candidates this question to see how well candidates understand Active Directory pentesting.
Answer:
“My top 3 AD-centric tools are:
BloodHound because it is a comprehensive AD enumeration tool that creates a nice visual map to quickly visualize relations between AD objects, domain, trusts, group policies, group permissions, and more. It quite literally helps me see different attack vectors.
PowerShell because it is already built-in to Windows clients and servers. I like to live off the land whenever possible. Most IT admin teams are already using PowerShell for administrative tasks and many of those same tasks can be useful for pentesters during a pentest.
PowerShell 因为它已内置于 Windows 客户端和服务器中。只要有可能,我就喜欢在土地上生活。大多数 IT 管理团队已将 PowerShell 用于管理任务,其中许多相同的任务在渗透测试期间对渗透测试人员很有用。
One example of this would be the ActiveDirectory PowerShell module. This allows admins to interact with AD through the PowerShell command line on a Windows host.
其中一个示例是 ActiveDirectory PowerShell 模块。这允许管理员通过 Windows 主机上的 PowerShell 命令行与 AD 进行交互。
If I was able to find my way to an IT admin’s desktop I may just be able to use their system to gain remote access to the domain controller. Especially if they are using the AD PowerShell module in their daily work.
如果我能够找到进入 IT 管理员桌面的方法,我可能只能使用他们的系统来远程访问域控制器。特别是当他们在日常工作中使用 AD PowerShell 模块时。
PowerView.ps1 which is part of the PowerSploit project because it has so many useful tools for enumerating AD objects, discovering shares, and even harvesting TGS tickets to attempt a Kerberoasting attack.”
PowerView.ps1 是 PowerSploit 项目的一部分,因为它具有许多有用的工具,可用于枚举 AD 对象、发现共享,甚至收集 TGS 票证以尝试 Kerberoasting 攻击。
HTB content that can help you answer this question:
可以帮助您回答此问题的 HTB 内容:
10. What types of attacks is the Diffie-Hellman (DH) exchange potentially vulnerable to?
10. Diffie-Hellman (DH) 交易所可能容易受到哪些类型的攻击?
💡Interviewers may ask this question to assess your understanding of the Diffie-Hellman exchange.
💡面试官可能会问这个问题,以评估您对 Diffie-Hellman 交易所的理解。
Answer:
“The Diffie-Hellman exchange is a method of securely exchanging keys over a public channel. The parties need no prior knowledge of each other to share this secret cryptographic key.
If not implemented and configured correctly, the Diffie-Helmman key exchange can be vulnerable to several types of attacks, the most common being a Man-in-the-Middle (MitM) attack, Logjam attack, brute-force attack, and side-channel attacks.”
11. What is union-based SQL Injection?
💡Interviewers may ask candidates this question to gauge a candidate’s understanding of different types of SQL injection attacks.
Answer:
“The term ‘union’ in Union-based SQL injection refers to the SQL UNION operator, which combines the results of two or more SELECT queries into a single result set.
In a Union-based SQL injection attack, an attacker appends a crafted UNION SELECT statement to the original query to force the application to return additional data that was not intended to be disclosed.
During a penetration test, I would attempt to identify Union-based SQL Injection vulnerabilities by carefully examining how user inputs are handled in the application. I’d look for potential points of entry where untrusted data is used in SQL queries without proper validation or parameterization.”
Hack The Box content to help you answer this question:
12. What is privilege escalation and how do you handle it?
💡Privilege escalation is a crucial phase during any security assessment, meaning interviews may ask you about it.
Answer:
“Privilege escalation is a type of attack that aims to gain unauthorized privileged access into a system.
The goal of privilege escalation after gaining a foothold on a system is to further our access to the level of an administrative user or find some bit of data (such as a password in a script file) that can be used to move laterally within the network.
Privilege escalation always starts with a detailed enumeration of the system we land on, including but not limited to: the operating system type and version, kernel level, running processes, installed services and applications, current user privileges, network traffic sniffing, hunting for sensitive data in various file types (configuration files, scripts, password managers, spreadsheets, etc.”
Hack The Box content to help you answer this question:
13. What is XXE and what can it be used for?
💡Interviewers may ask candidates this cybersecurity interview question to gauge a candidate’s understanding of XML external entity injection attacks.
Answer:
“XXE occurs when an attacker can inject malicious XML data into an application’s input fields, which is then processed by the server. When the server parses the XML, it may include external entities defined within the XML data, leading to unintended consequences.
My focus would be to identify and exploit XXE vulnerabilities in web applications to demonstrate their impact and potential risks to the organization.
I would use a combination of manual and automated testing techniques to detect and verify these issues. This includes fuzzing, payload injection, and examining application behavior in response to different XML inputs. A wide range of critical actions and information can be gathered through this kind of attack, including but not limited to:
-
Information Disclosure: Attackers can read files from the server’s filesystem by specifying external entities that point to local files. This can reveal sensitive information like passwords, configuration files, or system data.
-
Denial of Service (DoS): Attackers can trigger resource-intensive processing by defining large external entities, causing the server to consume excessive CPU and memory resources and potentially leading to a denial of service.
拒绝服务 (DoS):攻击者可以通过定义大型外部实体来触发资源密集型处理,从而导致服务器消耗过多的 CPU 和内存资源,并可能导致拒绝服务。 -
Server-side request forgery (SSRF): Attackers can abuse XXE to make the server perform unintended HTTP requests to internal or external resources, leading to further attacks like scanning internal systems or accessing sensitive APIs.
服务器端请求伪造 (SSRF):攻击者可以滥用 XXE 使服务器对内部或外部资源执行意外的 HTTP 请求,从而导致进一步的攻击,例如扫描内部系统或访问敏感 API。 -
Port scanning: An attacker can use XXE to scan ports of internal systems, potentially identifying other vulnerable services.”
端口扫描:攻击者可以使用 XXE 扫描内部系统的端口,从而可能识别其他易受攻击的服务。
Hack The Box content to help you answer this question:
Hack The Box 内容可帮助您回答此问题:
14. What is data packet sniffing?
14. 什么是数据包嗅探?
💡Interviews may ask this question as data packet sniffing is a common pentesting technique.
💡面试可能会问这个问题,因为数据包嗅探是一种常见的渗透测试技术。
Answer: 答:
“Packet sniffing is a technique used to capture and analyze data packets as they are traveling across a network.
“数据包嗅探是一种用于捕获和分析数据包在网络上传输的技术。
The process can be used for diagnostic, monitoring, security (i.e., pentesting)., or malicious purposes.
When performing packet sniffing, the device’s network interface card (NIC) is set to promiscuous mode, which allows it to capture all packets on the network regardless of their destination.
The packet sniffing tool is used to intercept and copy data packets on the same network segment where the device is connected. This can include packets not destined for the device running the sniffing tool.
数据包嗅探工具用于拦截和复制设备所连接的同一网段上的数据包。这可能包括不发往运行嗅探工具的设备数据包。
These packets are then analyzed offline for purposes such as troubleshooting network issues, monitoring network performance, or extracting sensitive information (such as credentials if we are performing a penetration test).
然后,这些数据包将脱机分析,以用于解决网络问题、监控网络性能或提取敏感信息(例如,如果我们正在执行渗透测试,则为凭据)。
The process may also be used by malicious actors to attempt to intercept sensitive data.
恶意行为者也可能使用该过程来尝试拦截敏感数据。
Packet sniffing can be countered by ensuring that secure network protocols and strong encryption are employed across the network. An Intrusion Detection System (IDS) can also be used to alert administrators to malicious packet sniffing activities.”
通过确保在整个网络中采用安全的网络协议和强加密,可以对抗数据包嗅探。入侵检测系统(IDS)也可用于提醒管理员注意恶意数据包嗅探活动。
15. Describe an XSS vulnerability in high-level terms. Ideally, as if you were explaining it to someone with only high-level technical knowledge.
15. 用高层次描述XSS漏洞。理想情况下,就好像您正在向只有高级技术知识的人解释它一样。
💡Interviewers may ask candidates this question to grasp a candidate’s ability to communicate complex technical information in an easy-to-understand manner.
💡面试官可能会问候选人这个问题,以掌握候选人以易于理解的方式传达复杂技术信息的能力。
Answer: 答:
“A cross-site scripting (XSS) vulnerability is a type of security issue that occurs when malicious code is injected (e.g., malicious SQL statements) into a website or web application, allowing attackers to execute their code on the browsers of unsuspecting users.
“跨站点脚本 (XSS) 漏洞是一种安全问题,当恶意代码(例如恶意 SQL 语句)注入网站或 Web 应用程序时,就会发生,允许攻击者在毫无戒心的用户的浏览器上执行其代码。
Imagine your website as a house with different rooms for various functionalities. Such as login, messaging, or user profiles.
XSS is like an intruder who finds a way to slip a harmful message or piece of code inside one of these rooms. When an unsuspecting visitor enters that room (opens a specific page or clicks a link), the intruder’s code executes in the visitor’s browser.
This can have several negative consequences, including but not limited to:
-
Data theft: The attacker can steal sensitive user information, such as login credentials, personal details, or payment card data.
-
Session hijacking: By exploiting XSS, the attacker could hijack an authenticated user’s session, gain unauthorized user access to their account, and perform actions on their behalf.
-
Malicious actions: Attackers might use the vulnerability to trick users into unknowingly performing harmful actions, such as changing account settings or making unauthorized transactions.
-
Phishing attacks: XSS can be used to present fake login forms, leading users to believe they are entering their credentials on a legitimate website, but in reality, they are providing the information to the attacker.
To protect against XSS, it’s essential to follow secure coding practices, validate and sanitize user input, and implement security mechanisms that restrict the execution of untrusted code on the website.”
为了防止XSS,必须遵循安全的编码实践,验证和清理用户输入,并实施安全机制来限制在网站上执行不受信任的代码。
Hack The Box content to help you answer this question:
Hack The Box 内容可帮助您回答此问题:
Preparation is key 准备工作是关键
These are just some of the questions you may come across in a penetration tester interview, but they are by no means set in stone.
这些只是您在渗透测试人员面试中可能遇到的一些问题,但它们绝不是一成不变的。
So, it’s important to be a lifelong learner and consistently upskill to ensure that you’re up to speed with the latest threats and techniques.
因此,成为终身学习者并不断提高技能以确保您跟上最新威胁和技术的步伐非常重要。
But remember, you aren’t expected to know everything, no one is! It’s impossible to know everything, so don’t pretend to. Be honest if you’re unsure of an answer.
但请记住,你不应该知道一切,没有人知道!不可能知道一切,所以不要假装。如果您不确定答案,请诚实。
You’ve got this! 你有这个!
At Hack The Box, we’re here to help cybersecurity professionals get hired and recruiters hire the best candidates.
在 Hack The Box,我们在这里帮助网络安全专业人员被录用,并帮助招聘人员雇用最优秀的候选人。
Aspiring hackers can apply directly to roles posted by companies worldwide. This includes roles from organizations like Amazon Web Services, NTT, Verizon, Daimler, DAZN, Context Information Security, and more.
有抱负的黑客可以直接申请全球公司发布的职位。这包括来自 Amazon Web Services、NTT、Verizon、Daimler、DAZN、Context Information Security 等组织的角色。
At the same time, recruiters can access a growing pool of talented individuals and look for their next cybersecurity star hire. Our new and revamped Talent Search helps recruiters find the perfect candidate more quickly and confidently than ever.
同时,招聘人员可以接触到越来越多的人才,并寻找下一个网络安全明星。我们全新改进的人才搜索功能可帮助招聘人员比以往任何时候都更快、更自信地找到完美的候选人。
原文始发于mrb3n:15 penetration testing interview questions (answered by experts)
转载请注明:15 penetration testing interview questions (answered by experts) | CTF导航