I am Harish SG, a security researcher who studies Masters in Cybersecurity at UT Dallas and AI security intern at Cisco,previously hunted on the Microsoft Bug Bounty Program and Google VRP
我是Harish SG,是一名安全研究员,在德克萨斯大学达拉斯分校攻读网络安全硕士学位,在思科大学担任人工智能安全实习生,之前曾在Microsoft漏洞赏金计划和谷歌VRP中被发现
I am sharing this article for security awareness and educational purposes only and I am sharing only personal opinions and none of these are related to my work at Cisco. I am not responsible if someone abuse this methods against tesla car owner and I wrote this article to bring awareness among tesla owner and Note this is not a vulnerability in Tesla vehicle or Tesla’s infrastructure
我分享这篇文章只是为了安全意识和教育目的,我只分享个人观点,这些都与我在思科的工作无关。如果有人滥用这种方法来对付特斯拉车主,我不负责,我写这篇文章是为了提高特斯拉车主的意识,请注意,这不是特斯拉汽车或特斯拉基础设施中的漏洞
In this article I am gonna share How I used OSINT techniques to hack tesla cars and what was the reply from tesla when I reported about this to them and How can impacted tesla owners protect themselves
在这篇文章中,我将分享我如何使用 OSINT 技术来破解特斯拉汽车,以及当我向他们报告此事时特斯拉的回应是什么,以及受影响的特斯拉车主如何保护自己
What is teslamate? 什么是特斯拉酸盐?
TeslaMate is an open-source, self-hosted data logger for your Tesla vehicle. It’s designed for Tesla owners who want detailed insights into their driving habits, charging behavior, efficiency, and other metrics related to their Tesla vehicle.
TeslaMate 是一款用于 Tesla 车辆的开源自托管数据记录器。它专为希望详细了解其驾驶习惯、充电行为、效率以及与特斯拉汽车相关的其他指标的特斯拉车主而设计。
Here are some features and aspects of TeslaMate:
以下是 TeslaMate 的一些功能和方面:
Detailed Dashboards: TeslaMate provides visual dashboards that display data on drives, charges, efficiency, and more. It makes use of Grafana for creating visually appealing and detailed data visualizations.
详细的仪表板:TeslaMate 提供可视化仪表板,显示有关驱动器、费用、效率等的数据。它利用 Grafana 来创建具有视觉吸引力和详细的数据可视化。
Charging Stats: It provides insights into your charging habits, how much you’ve spent on electricity, efficiency, and more.
充电统计:它可以深入了解您的充电习惯、您在电费上花费了多少、效率等。
Drive Tracking: You can get detailed statistics about each drive, including the path taken, efficiency, and other relevant metrics.
驱动器跟踪:您可以获得有关每个驱动器的详细统计信息,包括所采用的路径、效率和其他相关指标。
Geofencing: This allows you to define specific areas (like “Home” or “Work”) and get statistics based on those areas. It can help in understanding how much you drive within specific regions.
地理围栏:这允许您定义特定区域(如“家庭”或“工作”)并根据这些区域获取统计信息。它可以帮助您了解您在特定区域内的驾驶量。
Privacy: Since TeslaMate is self-hosted, all your data remains with you. Unlike some third-party services that might store your data on their servers, with TeslaMate, you have full control.
隐私:由于 TeslaMate 是自托管的,因此您的所有数据都保留在您身边。与某些可能将您的数据存储在其服务器上的第三方服务不同,使用 TeslaMate,您可以完全控制。
Updates & Community: Being open-source means there’s a community around it that can contribute to its development. This can lead to frequent updates, new features, and community support.
更新和社区:开源意味着它周围有一个社区可以为其发展做出贡献。这可能会导致频繁的更新、新功能和社区支持。
Integration with Home Automation Systems: Some advanced users have integrated TeslaMate with their home automation systems to make intelligent decisions based on vehicle state, like adjusting thermostats when the car is nearing home.
与家庭自动化系统集成:一些高级用户已将 TeslaMate 与他们的家庭自动化系统集成,以根据车辆状态做出智能决策,例如在汽车接近家时调整恒温器。
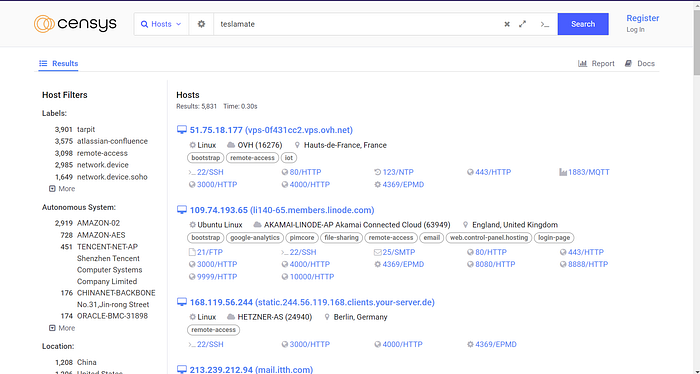
I used censys to find teslamate instances using this query “teslamate” i found that most of them secured with authentication
我使用 censys 使用此查询“teslamate”查找 teslamate 实例,我发现它们中的大多数都通过身份验证进行保护
I started to read documentation of the teslamate available here https://docs.teslamate.org/docs/installation/docker/ and while read the documentation I found that teslamate can installed and integrated with tesla cars without authentication
我开始阅读此处提供的 teslamate 文档 https://docs.teslamate.org/docs/installation/docker/ 在阅读文档时,我发现 teslamate 无需身份验证即可安装并与特斯拉汽车集成
Then I used the following query to find all teslamate dashboard without authentication
然后,我使用以下查询查找所有未经身份验证的teslamate仪表板
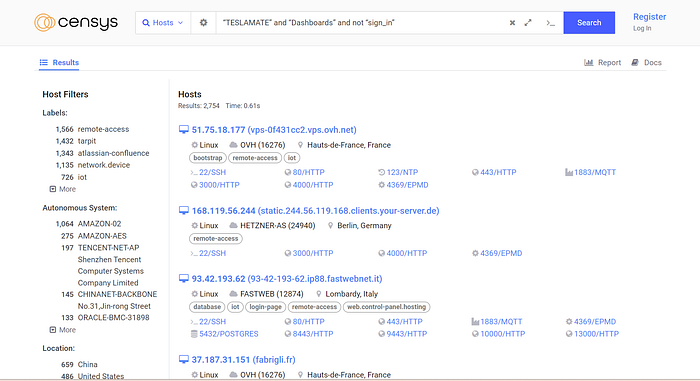
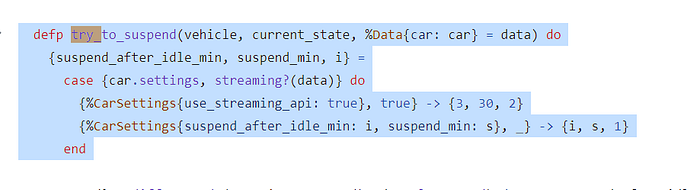
Out of curiosity I opened one of results and I found this below response cached by censys. (This is not realtime) this means that instance is misconfigured and it does not have authentication.
出于好奇,我打开了其中一个结果,我发现下面由 censys 缓存的响应。(这不是实时的)这意味着实例配置错误,并且没有身份验证。

I did not opened dashboard since it might be illegal even though it got exposed publicly or it might be legal gray area so I tried to contact owner to get permission but unfortunately I failed in that attempt of finding the owner then out of curiosity to know what can an attacker do if they can access this misconfigured teslamate I started to read their documentation and project’s github repository. I attacker can do following in misconfigured teslamate without authentication.
我没有打开仪表板,因为它可能是非法的,即使它被公开曝光,或者它可能是合法的灰色地带,所以我试图联系所有者以获得许可,但不幸的是,我试图找到所有者失败了,然后出于好奇,想知道如果攻击者可以访问这个配置错误的 teslamate,我可以做什么,我开始阅读他们的文档和项目的 github 存储库。攻击者可以在没有身份验证的情况下在错误配置的 teslamate 中执行以下操作。
- Track live location 跟踪实时位置
- check if driver present in that car or not
检查司机是否在那辆车里 - check if car is locked or not
检查汽车是否上锁 - make online car to sleep
让在线汽车入睡 - check if trunk of car is open or not
检查汽车后备箱是否打开 - check if car is in sentry mode or not
检查汽车是否处于哨兵模式
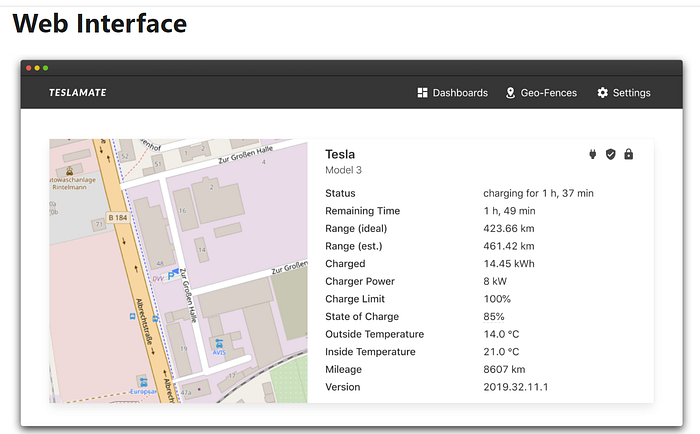
项目 github 存储库的屏幕截图

截图来自 Teslamates’repo
截图来自 Teslamates’repo

截图来自 Teslamates’repo
above screenshot shows what are the car data attacker can see in the misconfigured teslamate dashboard
上面的屏幕截图显示了汽车数据攻击者可以在配置错误的 Teslamate 仪表板中看到的内容
How can does this data can be used against tesla owners who have misconfigured teslamate dashboard?
如何利用这些数据来对付配置错误teslamate仪表板的特斯拉车主?
Attacker can do physical damage to the tesla owner who have their cars connect to a misconfigured teslamate dashboard
攻击者可以对特斯拉车主造成物理损害,因为他们的汽车连接到配置错误的特斯拉仪表板
How can tesla owner who has misconfigured teslamate protect themselves?
配置错误的特斯拉车主如何保护自己?
- Enable authentication in their teslamate’s instance by following this https://docs.teslamate.org/docs/guides/traefik
按照以下 https://docs.teslamate.org/docs/guides/traefik 在其 teslamate 的实例中启用身份验证 - If you are running this instance locally in home server then disable portforwarding of that specific port this dashboard running generally its 4000
如果您在主服务器中本地运行此实例,则禁用该特定端口的端口转发,此仪表板通常运行其 4000 - Try to contact services such as Shodan and censys to remove the results of your instance
尝试联系 Shodan 和 censys 等服务,以删除实例的结果
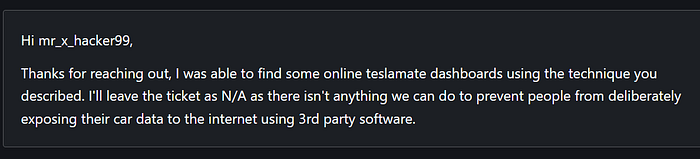
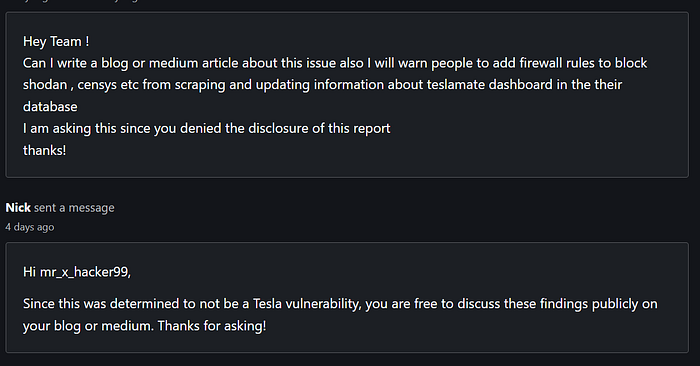
Response from Tesla when I reported about this issue to them and asked them to send push notification to users to remove this from internet via bugcrowd
当我向他们报告此问题并要求他们向用户发送推送通知以通过 bugcrowd 将其从互联网上删除时,特斯拉的回应
Thanks for reading my article!
感谢您阅读我的文章!
Try hacking LLM : https://github.com/harishsg993010/DamnVulnerableLLMProject
尝试黑客 LLM : https://github.com/harishsg993010/DamnVulnerableLLMProject
Hacking into Bard : https://infosecwriteups.com/hacking-google-bard-24f9dfa7b455
入侵吟游诗人:https://infosecwriteups.com/hacking-google-bard-24f9dfa7b455
Hacking into Facial Recognition system : https://medium.com/bugbountywriteup/hacking-into-facial-recognition-system-using-generative-ai-69a741077f0e
入侵面部识别系统:https://medium.com/bugbountywriteup/hacking-into-facial-recognition-system-using-generative-ai-69a741077f0e
Follow me on twitter: https://twitter.com/CoderHarish
在推特上关注我:https://twitter.com/CoderHarish
Follow me on linkedin :https://www.linkedin.com/in/harish-santhanalakshmi-ganesan-31ba96171/
原文始发于Harish SG:How I Hacked 1000 + Tesla Cars using OSINT