Multi-year Chinese APT Campaign Targets South Korean Academic, Government, and Political Entities


Recorded Future’s Insikt Group has conducted an analysis of a prolonged cyber-espionage campaign known as TAG-74, which is attributed to Chinese state-sponsored actors. TAG-74 primarily focuses on infiltrating South Korean academic, political, and government organizations. This group has been linked to Chinese military intelligence and poses a significant threat to academic, aerospace and defense, government, military, and political entities in South Korea, Japan, and Russia. TAG-74’s targeting of South Korean academic institutions aligns with China’s broader espionage efforts aimed at intellectual property theft and expanding its influence within higher education worldwide.
Recorded Future的Insikt集团对一场名为TAG-74的长期网络间谍活动进行了分析,该活动归因于中国国家资助的行为者。TAG-74主要专注于渗透韩国学术,政治和政府组织。该组织与中国军事情报部门有联系,对韩国、日本和俄罗斯的学术、航空航天和国防、政府、军事和政治实体构成重大威胁。TAG-74针对韩国学术机构的目标与中国更广泛的间谍活动一致,旨在窃取知识产权并扩大其在全球高等教育中的影响力。
The motivation behind Chinese state-sponsored actors collecting intelligence in South Korea is likely driven by regional proximity and South Korea’s strategic role in China’s competition with the United States and its regional allies in the Indo-Pacific. Recent tensions have emerged as China expressed concerns about South Korea’s closer relations with the US and its perceived involvement in Taiwan and alignment with the US and Japan’s containment of China. TAG-74’s intelligence collection efforts, which include spoofed domains and decoy documents related to inter-Korean cooperation, are expected to intensify as China seeks information to shape its diplomatic and business engagements with South Korean entities.
中国国家支持的行为者在韩国收集情报背后的动机可能是由于地区邻近以及韩国在中国与美国及其印太地区盟友竞争中的战略作用。最近的紧张局势出现了,因为中国对韩国与美国的更密切关系及其对台湾的参与以及与美国和日本对中国的遏制表示担忧。TAG-74的情报收集工作,包括与朝韩合作有关的欺骗性域名和诱饵文件,预计将随着中国寻求信息来塑造其与韩国实体的外交和商业接触而加强。
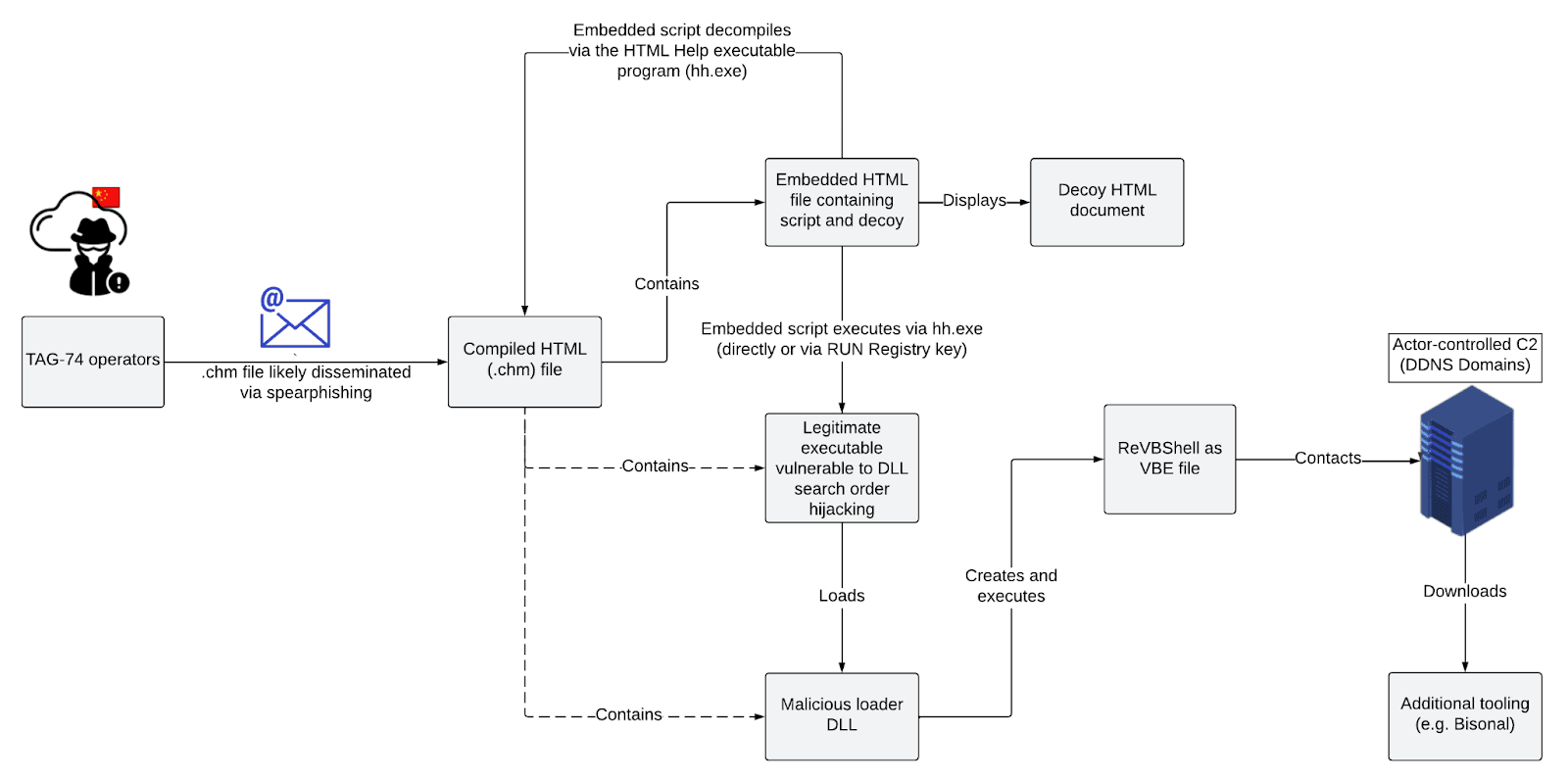 Typical infection chain observed in TAG-74 campaign targeting South Korea (Source: Recorded Future)
Typical infection chain observed in TAG-74 campaign targeting South Korea (Source: Recorded Future)
在针对韩国的TAG-74活动中观察到的典型感染链(来源:记录的未来)
TAG-74 is a well-established Chinese state-sponsored threat activity group specializing in intelligence collection against South Korean, Japanese, and Russian organizations. Their tactics, techniques, and procedures (TTPs) include the use of .chm files that trigger a DLL search order hijacking execution chain to load a customized version of the VBScript backdoor ReVBShell. Additionally, a custom backdoor known as Bisonal is used to enhance capabilities once initial access through ReVBShell is established. This customized ReVBShell variant is likely shared between TAG-74 and another closely related threat activity group, Tick Group, indicating collaboration between these groups.
TAG-74是一个成熟的中国国家赞助的威胁活动组织,专门收集针对韩国,日本和俄罗斯组织的情报。他们的策略、技术和程序 (TTP) 包括使用 .chm 文件触发 DLL 搜索顺序劫持执行链来加载自定义版本的 VBScript 后门 ReVBShell。此外,一个称为Bisonal的自定义后门用于在通过ReVBShell建立初始访问后增强功能。这种定制的 ReVBShell 变体很可能在 TAG-74 和另一个密切相关的威胁活动组 Tick Group 之间共享,表明这些组之间的协作。
The persistence of TAG-74 in targeting South Korean organizations and its likely operational alignment with the Northern Theater Command suggests that the group will continue its active and long-term intelligence-gathering efforts in South Korea, Japan, and Russia. Notably, the use of .chm files by Chinese state-sponsored actors is not particularly common outside of South Korea. However, the use of this attack vector in activity targeting South Korea has been seen both in TAG-74 campaigns and, more widely, in activity attributed to North Korean state-sponsored threat activity groups such as Kimsuky and APT37. Organizations should monitor for the presence and use of .chm files, particularly if they are not commonly used within their environment, as this tactic has gained prevalence among threat actors in recent years.
TAG-74持续针对韩国组织,并可能与北方战区司令部在行动上保持一致,这表明该组织将继续在韩国、日本和俄罗斯积极和长期地收集情报。值得注意的是,中国国家资助的演员使用.chm文件在韩国以外并不特别普遍。然而,在针对韩国的活动中使用这种攻击媒介,无论是在TAG-74活动中,还是在更广泛的朝鲜国家支持的威胁活动团体(如Kimsuky和APT37)的活动中都可以看到。组织应监视 .chm 文件的存在和使用,特别是如果它们在其环境中不常用,因为近年来这种策略在威胁参与者中越来越普遍。
原文始发于recordedfuture:Multi-year Chinese APT Campaign Targets South Korean Academic, Government, and Political Entities
转载请注明:Multi-year Chinese APT Campaign Targets South Korean Academic, Government, and Political Entities | CTF导航